Adobe Flash Player Install Manager
Adobe Flash Player Install Manager is an unwanted Mac app that belongs to the family of browser hijackers and is designed to take over your Mac’s main browsing program. Adobe Flash Player Install Manager will replace the default browser homepage and begin to page-redirect your searches to sites it’s programmed to promote.
Keep in mind that Adobe Flash Player Install Manager is a legitimate app and the official Flash Player installer Adobe Flash Player Install Manager.app can be found in the Utilities directory. However, sometimes it may be a target of malicious virus by cybercriminals.

The Adobe Flash Player Install Manager Pop up
If you notice any unwanted changes in the browser’s starting page, toolbar, or search engine and if you start to experience sudden page-redirects while surfing the web, do not panic because the likely cause of all this unusual behavior is exactly a browser-hijacking app such as Adobe Flash Player Install Manager, Search Marquis, Vevatom.com.
While it is certainly irritating to have it added to your browser, in the majority of cases, a hijacker wouldn’t harm the computer it is installed on because that is not why it has been created. The reason such apps latch onto popular browsers like Firefox, Chrome, and Safari is because they seek to fill them with various types of ads that generate revenue when clicked upon. Even if you don’t want to interact with the ads, you are still likely to end up clicking on some of them because that is usually the only way to get them away from your screen, at least for a couple of minutes.
Adobe Flash Player Install Manager for Mac
Adobe Flash Player Install Manager for Mac is an invasive and aggressive advertising app programmed to attach itself to and hijack the main browsers of Mac computers. Upon entering the browser, Adobe Flash Player Install Manager for Mac makes changes to it and begins triggering redirects to unknown to the user websites.
Those sudden redirects are probably the worst part of having a browser hijacker on your Mac. Not only are they very unpleasant and prone to obstruct your browsing but also the fact that you cannot control them means that you could end up getting redirected to some unsafe and potentially hazardous site if that is what the hijacker has been programmed to promote. There’s no need to tell you what dangerous forms of malware you could get exposed to in that way – Trojans, Rootkits, Phishing malware, and Ransomware are only a few examples of all the threats you could potentially be faced with.
The Adobe Flash Player Install Manager Pop up
The Adobe Flash Player Install Manager pop up is a rogue browser-hijacking app that needs to be uninstalled immediately because of its aggressive advertising activities inside the main browser. The Adobe Flash Player Install Manager pop up can scan your browsing history to determine what types of content you like and then show you relevant ads.
The problem here is that the info gained from your browser is likely to get sold to third parties for extra profit and those third parties may use the data in all sorts of ways, some of which may be harmful to your online security and privacy. Needless to say, you are not given a say in how your data would be utilized after it’s been collected from the browser.
The Adobe Flash Player Install Manager app is a Mac application that carries the browser hijacker inside of it as a “bonus” feature that gets installed automatically. The Adobe Flash Player Install Manager app cannot be separated from the hijacker and so you’d have to uninstall it to get the hijacker removed.
We believe that with the help of the next set of instructions, you will be able to achieve this without any difficulty and so we recommend that you complete the steps sooner rather than later. Remember, removing the hijacker is important to your system’s safety as it will help you stay away from more hazardous forms of malware such as the aforementioned Trojans, Spyware, Rootkits, and Ransomware.
SUMMARY:
| Name | Adobe Flash Player Install Manager |
| Type | Browser Hijacker |
| Detection Tool |
Remove Adobe Flash Player Install Manager from Mac
Removing the hijacker extension
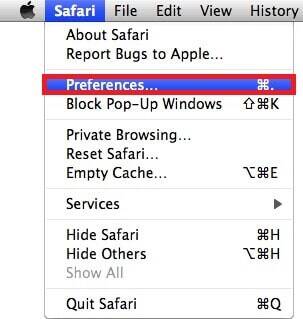
If Adobe Flash Player Install Manager has added its own extension to Safari and you manage to remove that extension, there may be no need to complete the whole guide so we suggest you try this first. To do it, start the browser, click on the Safari menu and then on Preferences.
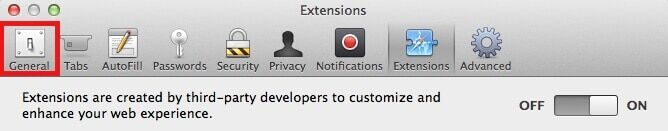
From the Preferences window, go to Extensions and try to find the extension placed there by Adobe Flash Player Install Manager. It may or may not have the same name but it shouldn’t be too difficult to find the extension that is causing disturbances in the browser.

If there is an item in Extensions that has not been installed there by you, that one is likely the hijacker extension. Once you think you have figured out which Safari extension you must remove, select the Remove/Uninstall button next to it. In case you are not certain what you must remove, it is okay to delete all of the extensions but be sure to remove them one at a time so that you can determine which one is problematic and safely re-install the other ones.
After you delete the unwanted extension(s), restart the computer, go to Safari’s Extensions page again to see if the removed ones are still gone. If they have returned or if you still see signs of the hijacker’s presence, proceed to the next steps.
![]()
You should keep Safari closed for the next steps so quit it. If the hijacker doesn’t allow you to do this or you cannot close the browser for some other reason, select the Apple Menu and then Force Quit. Now click on the Safari entry and then use the Force Quit button to close the browser.
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Go to Applications > Utilities , open Activity Monitor and find the Adobe Flash Player Install Manager process. If you don’t see a process with this name there, look for other suspicious ones such as processes with high RAM and CPU expenditure that are not coming from programs you have opened at the moment or processes that have odd names that you do not recognize.
If you think that a given process is from the hijacker, look for its name on the Internet to verify that the process isn’t supposed to be running on your Mac and rule out the possibility of it being an important OS process that you must’t touch.

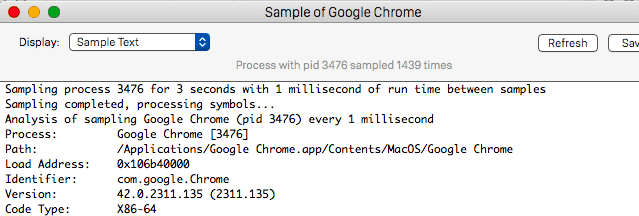
Next, select the suspicious process, click on the Information button, select Sample, and then Save the sample file on your Desktop. You must now test the sample file with this free online scanner:

If the scan results conclude that there’s malicious code in the scanned file, select its process from the Activity Monitor and then click on the Quit button to end that process.
![]()
Hold the Shift key and open Safari – this will Safe Launch the browser, preventing any previously opened tabs and pages from loading. If any such pages/tabs do load again because of the hijacker, close Safari, stop your Internet connection and Safe Launch the browser again.
If you are using cable Internet, plug out the Ethernet cable to stop the connection. If you are using Wireless, hold down the Option key, click on the Wi-Fi menu at the top, and select Turn Wi-Fi Off. Once you finish the rest of the steps from this guide, go to the Wi-Fi menu again to re-enable your Wi-Fi connection by selecting the Turn Wi-Fi On option.
![]()
Once you manage to Safe Launch Safari, first go to the Extensions page again and if the unwanted extension (or extensions) you removed earlier has returned, delete it again and then proceed to the Privacy tab of Preferences.
There, you will find a Remove All Website Data option which you must select to clean the browsing data and remove anything that may be left from the hijacker. This action will get you logged out of your website accounts so you must make sure that you are able to log into them afterwards.

After that, open General from Preferences and see what the current address of the Safari homepage is – if it seems that the hijacker has changed that address, you change it again to an address chosen by you, one that you trust and know is safe and reliable.
It is very important to not allow the hijacker to determine what your homepage address is because oftentimes the sites that are made browser homepages by such hijackers are not particularly safe and could expose the user to various sorts of virtual threats.

Finally, go to the History menu of Safari and use the Clear History button to delete the browser’s history. Make sure to delete it “from the start” so that there’s no chance that any hijacker-related data is left inside the browser. If this action seems to be taking a while, do not quit Safari and wait patiently – it is normal for it to take some time if you haven’t recently deleted the browsing history.
![]()
It is not uncommon for browser hijackers to take over other browsers that may have been installed in the system so, if you have other browsers on your Mac, you must check them for hijacker extensions and clear their data too.
![]() Removing ads from Firefox for Mac:
Removing ads from Firefox for Mac:
If you have Firefox, open it, click on its menu, and go to Add-ons > Extensions. Look for items with the Adobe Flash Player Install Manager name or anything close to this and delete them. Also delete any other extensions that look like they shouldn’t be in Firefox and/or that you cannot recall installing.

Now, to learn how to clear the browsing data for Firefox so that there’s no traces left from the hijacker in it, visit this guide on how to refresh Firefox and follow its instructions.
![]() Removing ads from Chrome for Mac:
Removing ads from Chrome for Mac:
For Google Chrome users, open the Chrome browser, select its menu, and then select More Tools. From there, click on Extensions to reveal what extensions are installed in the browser and delete the ones you deem suspicious as well as anything that carries the Adobe Flash Player Install Manager name or a name similar to it.
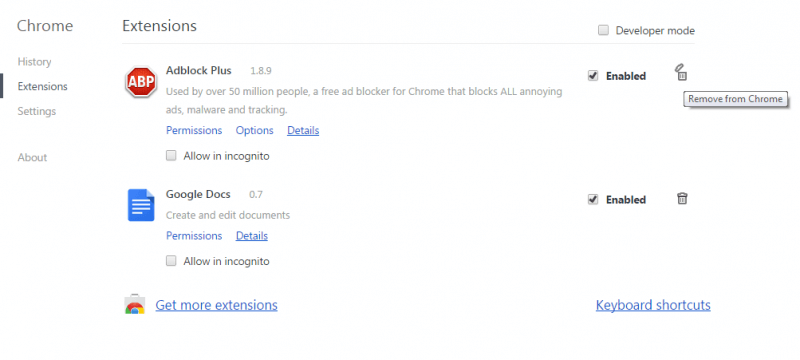
Now, from the browser menu, go to Settings, and click on the Search Engine option from the left panel. Next, select Manage Search Engines and carefully look at the list of search engine tools that are used by the browser. If you see search engines there that you do not recognize, select the three-dot button next to each and then click on the Remove from list option to remove the engine from the browser. This is important because if the hijacker has added some rogue and unreliable engine to the browser, your web searches may start to get redirected to unsafe content, potentially exposing you to different web hazards.
Finally, to ensure that everything in Chrome is cleaned, go to this guide where we show how to clear Chrome data and follow the steps so that any potential remnants of the hijacker would be removed.
Final Notes
Completing the steps from above should usually result in full removal of the hijacker but if you still seem to have the unwanted software even after finishing the guide, we recommend that you use the professional removal tool we have included in our guide and/or contact us through the comments section below for further assistance.

Leave a Comment