Ako Ransomware
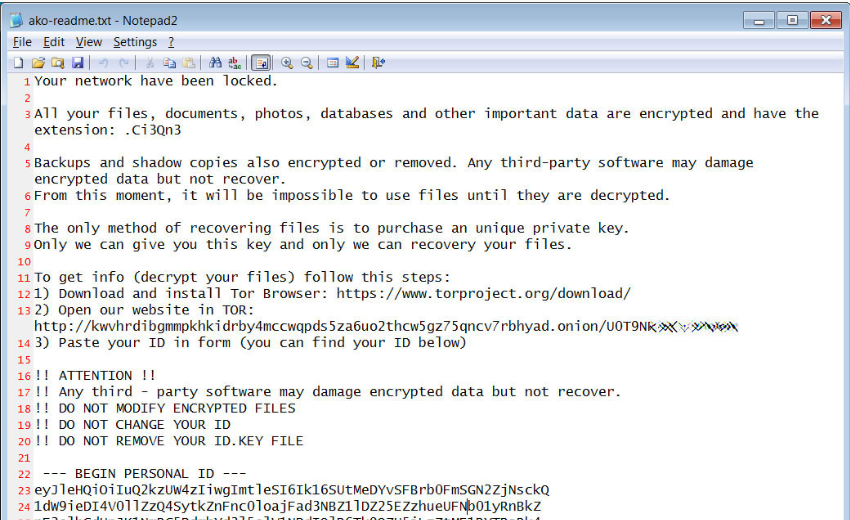
Ako is a ransomware infection developed with the sole purpose to extort money from its victims through a simple blackmail scheme. What Ako Ransomware does is it secretly encrypts the files found on a computer and then places a ransom-demanding message on its screen. The Ako Ransomware Ransomware stays pretty much invisible during the time it is busy locking-up your files. Only once it ends the file-locking process does this virus reveal itself. Typically, a threat like Ako Ransomware would generate a text file or a banner with ransom-payment instructions contained in it.
Тhe Ako Ransomware is distributed through spam emails.
This article was created to discuss the typical features of Ako Ransomware and the possible methods there are to remove it. This program is a new representative of the Ransomware class and what it does is it renders some of your most important information inaccessible by encrypting it with complex code. The article below gives further details and instructions on how to deal with the applied encryption and possibly recover some of your information, as well as steps on how to remove the Ransomware virus from your computer.
The Ako Malware
The Ako Ransomware virus is a harmful computer threat intended to encrypt valuable user information and keep it inaccessible until a ransom is paid. The people behind the Ako Ransomware virus typically demand a certain amount of money in order to provide the victims with a special decryption key to access their files. The Ako Malware virus operates silently and most users fail to notice it during the encryption period. Part of the reason for that stems from the fact that the file encryption is not a damaging process and it doesn’t harm the affected data. Once ready with the encryption, Ako Malware notifies its victims about the required ransom and the way it must be paid.
The first thing that Ako Ransomware does once it gets inside your computer is to determine which files you open and use frequently, and then encrypt them all with a secret encryption code. Then, after the file-encryption process is over, the hackers behind the ransomware alert you about all that has taken place by putting a message on your screen that also requires a ransom payment from you. The crooks want your money in order to send you a secret decryption code that can reverse the applied encryption and typically threaten that if you don’t pay, they will destroy that key and will leave your files inaccessible for good.
The Ako Ransomware file decryption
The Ako Ransomware file decryption is a complex coding procedure which, if performed successfully, can make the files encrypted by Ako Ransomware accessible again. The tricky part about the Ako Ransomware file decryption is that it requires a decryption key to be activated and that key is in the hands of the hackers behind the ransomware.
Being one of the latest representatives of the Ransomware’s file-encoding group, Ako Ransomware is malware that could be extremely difficult to fight off. In many cases, professional assistance may be necessary to remove the virus. Our removal guide below, however, is an alternative to the costly professional help and the ransom payment that the hackers want. Its steps can be quite effective when it comes to successfully removing Ako Ransomware, as long as you follow them closely. If you find it hard to strictly repeat the manual steps, though, it might be faster and better to use a professional removal tool. Whichever method you choose to deal with the Ransomware, we would like to advise you not to pay any ransom money until you try alternative methods to manage the infection. As far as your encrypted files are concerned, in the guide below you will find a section with some free file-recovery suggestions that may work. Of course, we cannot give you any guarantees about the future of your data but if you can extract copies from your system or have backup copies, now is the time to use them.
SUMMARY:
| Name | Ako Ransomware |
| Type | Ransomware |
| Detection Tool |
Remove Ako Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment