Alert-fix.club
Alert-fix.club is an unwanted online advertising app that latches onto the main browser in the system and alters its settings and behavior. Alert-fix.club aims to expose the user to aggressive online ads and to draw more traffic to the sites that sponsor it.
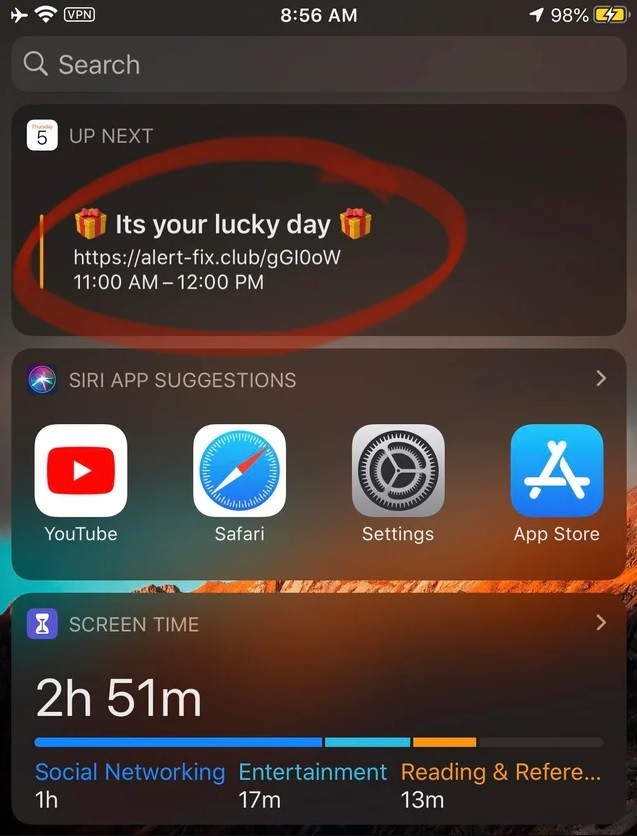
Apps like Alert-fix.club are really common and you can encounter them all over the Internet. They are not as dangerous as Ransomware, Trojan horses, Spyware, or other forms of harmful malware, but they are still mostly regarded as unwanted because of their aggressive advertising behavior, the unwanted changes they introduce to the browser’s homepage and search engine without user permission, and their ability to look into the browser’s history and to collect data from it. Most apps like Alert-fix.club are compatible with many different browsers, including Firefox and Chrome. Their wide compatibility ensures that they can get installed onto more computers and redirect their users to the sites they are supposed to advertise. The end goal of this and other similar apps is, of course, financial profit. The ads generated by the hijacker and the sites they redirect to all earn money based on clicks and views. There are online remuneration models known as Pay-Per-View and Pay-Per-Click that make all this possible. Needless to say, a lot of advertisers seek to profit from these models and implement them in their sites and products. However, some go a step further and create apps the sole purpose of which is to generate ads and page redirects that use the Pay-Per-View and Pay-Per-Click models in order to earn money for their creators. In those cases, there is little to no use from the hijacker app for the end-users such as yourself. This fact, combined with the overall aggressiveness and intrusiveness of the hijacker is what makes apps like Alert-fix.club particularly unpleasant and undesirable.
If you have a hijacker in your system, you must make sure to uninstall it sooner rather than later. The reason isn’t that the app itself will corrupt your system or data or carry out some other harmful activity but the fact that the ads and the redirects coming from it may be unsafe and you’d usually have no way of knowing that before it gets too late.
In most cases, the creators of software like Alert-fix.club don’t concern themselves with the online safety of the users too much. They need to gain better profits and that’s why they oftentimes allow all kinds of ads and sites to get advertised by their hijackers. Unfortunately, what this means is you can get sent to some sketchy site that offers low-quality products or even land on sites that spread pirated content and may expose you to dangerous viruses, Ransomware, Trojans, Worms, and more. It is always inadvisable to keep software in your computer that doesn’t benefit you in any way and simply takes up space and wastes your computer’s resources. In the case of apps like Alert-fix.club, this is especially true because if you don’t uninstall this hijacker and if you don’t remove its unwanted changes from your browser, you may end up getting your computer exposed to much more dangerous forms of software.
SUMMARY:
| Name | Alert-fix.club |
| Type | Browser Hijacker |
Remove Alert-fix.club Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply