Alka
Alka is a Ransomware infection that demands a ransom payment to liberate user data from its encryption. Typically, Alka displays a ransom-demanding notification on the victims’ screen to notify them about the file encryption. The Alka Ransomware is a virus that won’t directly cause harm to the files it encrypts or to the system of your computer. However, if Alka is in your PC, it is possible that there might be another virus in your computer. Oftentimes, infections like the Alka Ransomware are distributed with the help of Trojan Horse viruses, meaning that you might currently have a Trojan in your system as well.
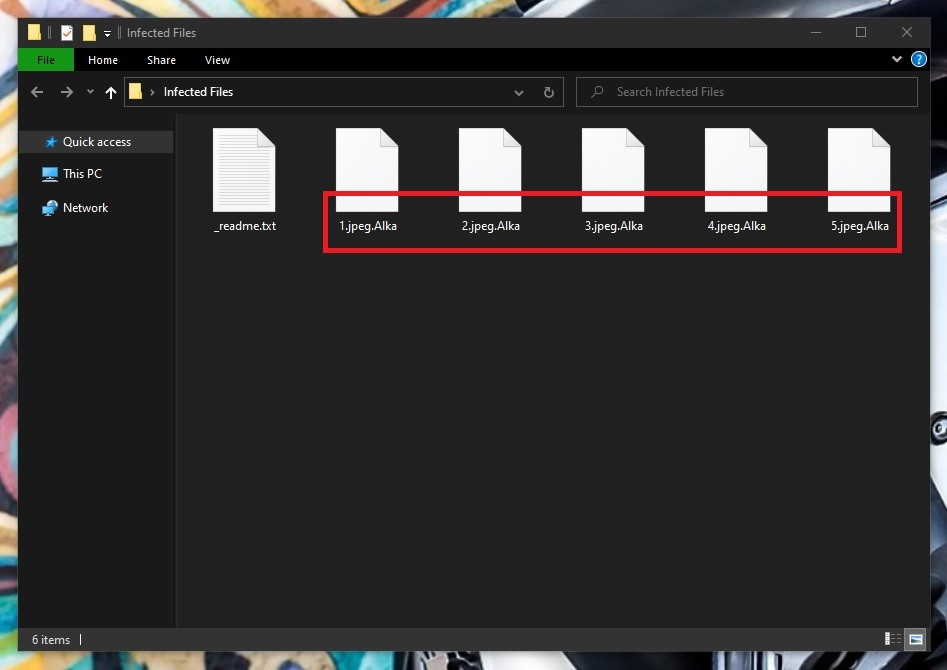
The Alka Virus will encrypt your files
Alka is one of the many new ransomware viruses, released on the internet. If your computer currently has this threat in its system, the chances are the files stored on it have been locked with secret encryption and you are unable to open them. A scary ransom-demanding message is also probably placed on your screen, asking you to pay some money to the cryptocurrency account of some anonymous hackers.
Our removal guide below, however, is created to help you potentially regain access to your files and remove the terrible file-encrypting virus from your system. While we can’t promise that the provided instructions will be 100% effective, it’s still something we suggest trying instead of paying a ransom to the hackers behind Alka.
The Alka Virus
The Alka virus is demanding a ransom in cryptocurrency to provide the victims with a decryption key. The ransom notification, displayed by the Alka virus, informs the users about the ransom payment methods and prompts them to release a payment immediately. The Alka virus requires you to follow the instructions provided in its ransom-requiring message. If you don’t do everything exactly as required, your files won’t get released from the Alka encryption. However, the problem with Ransomware threats like this one is that you could pay the money and still not get your encrypted files back.
Ransomware, as a malware category, has been around for decades and is presently possibly one of the most malicious online threats. Today, almost anyone who uses the web is at risk of becoming infected with Ransomware. Especially, if they do not implement some basic web security measures and are careless about their browsing. The easiest way you can get compromised with a cryptovirus like Alka is through a spam email with malicious attachments. Trojan Horses are also used as Ransomware transmitters as they oftentimes are programmed to distribute different kinds of additional malware. Typically, Trojan infections happen when you open or click on an infected spam message, malicious email attachment, or a misleading link.
Regardless of the contamination method, once inside, the Ransomware gets down to its dirty work right away. It scans the entire machine for specific file types and then encrypts them one by one with a secret algorithm. Sadly, the chances of detecting the infection while it is encrypting your files are minimal. The file-encryption process typically goes under the radar of most security programs and is not flagged as malicious. This helps the malware complete its agenda without being interrupted and surprise the victims with its scary ransom-demanding message at the end of the encryption.
The Alka File Decryption
The Alka file decryption is available only to those who pay for a decryption key. However, the hackers give no guarantees that the Alka file decryption key they will send will work flawlessly. Paying the ransom required by the Alka virus can backfire and make things worse for you because you may get a key that doesn’t work or you may even not get a key whatsoever. That is why it’s safer to try alternative methods for dealing with the Alka Ransomware while leaving the money transfer as your last possible option in case nothing else has helped you
Not having access to your files can be a really frustrating experience. But even more frustrating could be the fact that you are getting blackmailed to pay a ransom to access them. This is a criminal tactic, which relies on your panic and your desperation. However, since you are here, we won’t let the panic take over you.
Apart from the ransom payment, there are some other alternative methods, which may potentially help you get back your much-needed files. One of them is through file backups. If you keep copies of your data on external drives or cloud storage, or if you have them in your inbox, all you’ll need to do is remove the infection from the computer and simply copy the files back on the clean system. Another option is to try to extract backup copies from the OS. Of course, such methods may not always be enough to retrieve all the encrypted information, but paying the ransom will also not guarantee that everything will go back to normal. That’s why, if you decide to give our file-recovery suggestions a try, in the removal guide below you will find all the instructions, as well as a professional Alka removal tool that can scan your computer for hidden ransomware-related code.
SUMMARY:
| Name | Alka |
| Type | Ransomware |
| Detection Tool |
Remove Alka Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment