Allow-space.com
Allow-space.com is an unwanted Chrome and Firefox extension that is known for modifying the affected browser and using it as a platform for advertising certain sites. Allow-space.com causes automatic page redirects in the browser and spams the screen with ads in order to generate advertising revenue.
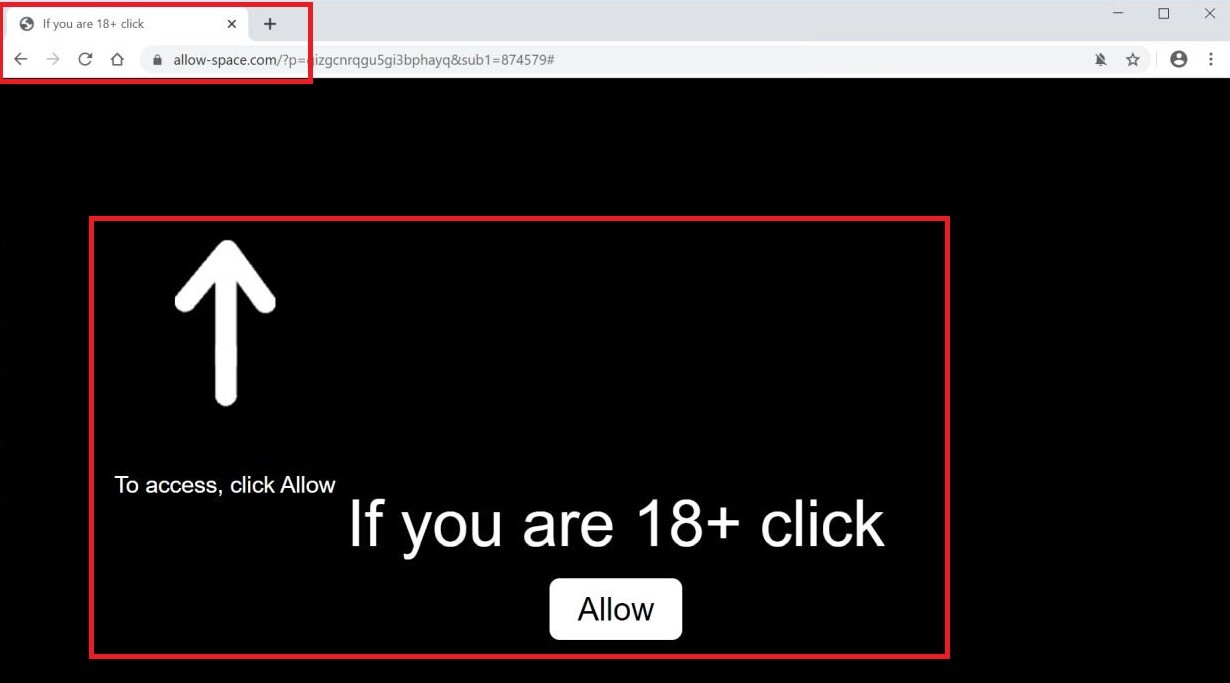
The Allow-space.com Virus will display pop up ads and messages
This type of applications is actually quite common and many users may have an extension similar to Allow-space.com inside their browsers without even realizing it. The thing that sets a regular browser extension apart from one like Allow-space.com is the aggressive advertising techniques used by the latter. This is why Allow-space.com and other similar applications are referred to as browser hijackers. They take over the browser’s search engine, replace the default homepage, and add new buttons in the toolbar without requesting permission from the user. At first glance, it may seem like these new elements are there in order to benefit the user by providing some new function or a useful online tool. However, it doesn’t take long before people realize that the purpose of the introduced changes is almost entirely advertising-oriented. Any modifications a browser hijacker makes in the browser are almost guaranteed to be part of its advertising agenda. The new search engine will probably redirect your searches to the sites that sponsor the hijacker instead of showing you the information you are actually looking for. The homepage imposed on the browser is likely from one of the sites that Allow-space.com is tasked with promoting or maybe the official site of the hijacker. All in all, there’s little to no benefit to be gained from such an app, which is why uninstalling it is the most advisable course of action.
Some security hazards you must know about
The good news if you are faced with Allow-space.com is that the app that is currently bothering you is not as dangerous as a virus, Spyware, or a Ransomware infection. The aforementioned are actual harmful computer threats and compared to them the Allow-space.com hijacker is more of an inconvenience than an actual danger.
That being said, it is unwise to trust the content put on your screen by the hijacker or to allow this app to keep using your browser as an advertising platform instead of removing it. Something you must understand about this type of apps is that, even though a hijacker would usually not possess harmful abilities, the sites it may promote on your screen could sometimes be unreliable, have a low reputation, or be outright unsafe. The developers of the hijacker aren’t concerned with the quality and the reliability of the websites they promote. All they care about is making money from the paid ads and page redirects. Of course, this means that even if a given site is questionable, illegal, and/or filled with Trojans and Ransomware, as long as it pays a commission to be advertised, the hijacker’s creators will promote it through their app. That is why it is a bad idea to allow the unwanted app to keep spamming you with unverified advertising content and it’s also why we advise you to try out the detailed guide from below and, with its help, uninstall the hijacker from your PC and remove its changes from your browser.
SUMMARY:
| Name | Allow-space.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Allow-space.com Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment