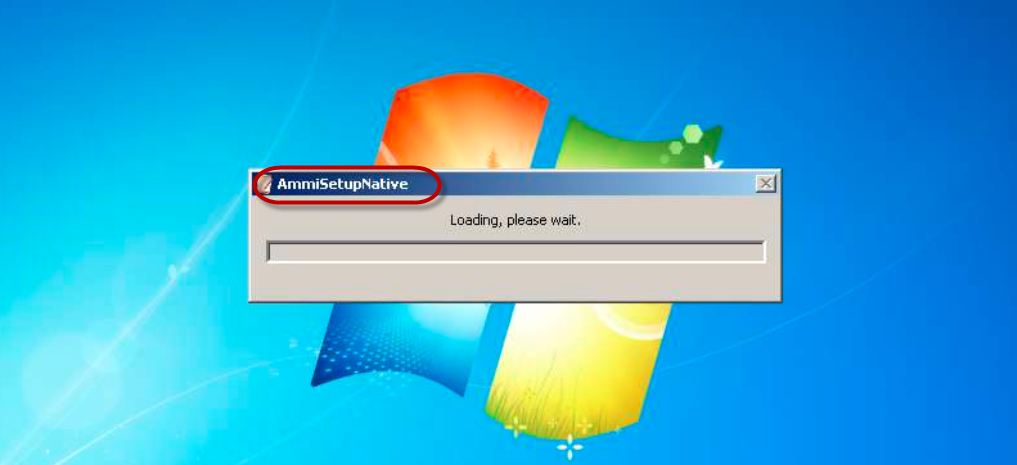
Ammi Setup Native
Ammi Setup Native is evidence that some ad types of applications or potentially unwanted tools are active on your system. While Ammi Setup Native is running, you will certainly regularly experience countless system issues leading to poor system performance.
The Ammi Setup Native virus is brought right into your workstation with some suspicious sources
A computer problem that very many people have is the appearance of intrusive and irritating advertising messages on their screens during browsing sessions. Such a problem could typically be attributed to one of two possible reasons. The first one is that the sites the user visits simple have way too much advertising content in them in which case the logical way to put an end to the ads invasion would be to simply stop visiting the said sites. Of course, an ad-blocker tool could also help but there are many forms of adverts such as pop-ups, pop-unders, page-redirects and others that oftentimes seem to get pass the blocker and still get displayed on the screen. The other possible cause for the invasion of ads on the user’s screen is the presence of an adware or a browser hijacker or some similar app inside the Chrome, IE, Firefox or whatever browser is currently being used on the computer. An app such as this would normally seek to swarm the user’s browser with various types of advertisements and try to lure the user into clicking on the different ads. Each click on such an ad earns revenue for the creators of the ad-generating software component which is also the main reason why having such an app on your computer would likely mean that the web ads you see will be quite aggressive and invasive.
AmmiSetupNative.exe
Here, we will give you an example with an application named AmmiSetupNative.exe which belongs to the adware family. You can get AmmiSetupNative.exe software on pretty much any browser and it may actually be rather difficult to get rid of the intrusive application.
Here, however, we can help you uninstall Ammi Setup Native in case you are struggling with its presence on your computer – have a look at our removal guide manual below and use the steps that are in it to successfully eliminate the unwanted software from your browser and computer.
Why it is important that you do not interact with the commercial messages that are coming from Ammi Setup Native
It may be tempting to click on some of the adverts since they may seem to represent interesting offers and discounts of products that you may like to purchase. However, you must remember that not everything is what it seems and this fully applies to the adverts that you could see inside our browser, especially if you have an adware in your computer. While Ammi Setup Native or Web Navigator Browser itself isn’t technically a dangerous piece of malware like a Trojan Horse or some nasty Ransomware program, it’s ads could sometimes be less than reliable and safe. Unfortunately, it is possible that you may land on some sketchy and obscure page after clicking on some adware-generated ad and this may potentially expose your computer to various forms of malware threats – viruses, Spyware, Rootkits as well as the above mentioned Ransomware and Trojan Horse infections. The Internet isn’t exactly a safe place and there is no need to further risk the security of your computer by clicking on random questionable adverts. Therefore, the removal of Ammi Setup Native is the advisable course of action so we advise you to waste no time and use our removal instructions form the guide above in order to eliminate the ad-generating software element.
SUMMARY:
| Name | Ammi Setup Native |
| Type | Browser Hijacker |
| Detection Tool |
Ammi Setup Native Removal
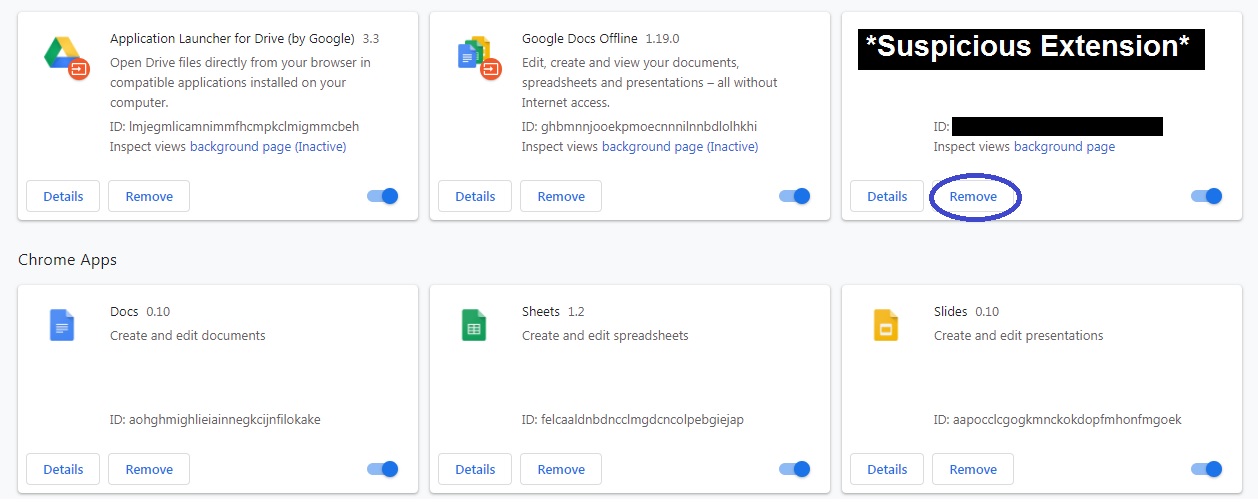
Deleting the Ammi Setup Native extension
If there is an extension in your browser placed by Ammi Setup Native, you may get rid of the hijacker problem by simply removing said extension which could remove the need to complete any of the more complex steps from this page.
The process of removing an unwanted extension slightly varies from one browser to the other but it is quite similar across most popular browsing programs. Regardless of what your browser is, you must open it, go to its menu, and select its Extension settings. On Chrome, for instance, you must select More Tools from the browser menu and then click on Extensions. On Firefox, you must go to Add-ons > Extensions from the Firefox menu. This is similar for other browsers as well. Once you get to the list of browser extensions, you must find the Ammi Setup Native one and delete it. If there isn’t an extension with the Ammi Setup Native name, look for other suspicious ones and if you find any, remove them. You can also try removing all of the extensions, one at a time, if you are uncertain which one might be linked to Ammi Setup Native. Once you figure it out, you can safely restore the other deleted extensions that aren’t related to the hijacker. If any particular extension wouldn’t get removed or would come back instantaneously after you delete it, first click on its Disable button (on Chrome this is a toggle button that must be toggled off) and then quickly select the Remove/Uninstall button again.
Revoking site permissions
In some cases, a simple notifications permission given to a site related to the hijacker could be the whole cause behind the browser disturbances you’ve been experiencing so here is how you can take care of that.
First, go to the browser’s Settings from its main menu and type permissions in the Settings’ search bar. Look through the results and select the one labeled Notifications.

In the Notifications settings, scroll down to see what sites are allowed to show notifications inside the browser and if any of those sites seems like it could be linked to Ammi Setup Native (or has the Ammi Setup Native name), block that site from showing any more notifications. On Chrome, you must first click on the three-dots icon next to the site and then select the Block option.


If you don’t know which site may be causing unwanted notifications to show up on your screen, simply block all of them for good measure.
Also, another thing we suggest you do is scroll back up to the top of the Notifications settings and disable the Sites can ask to send notifications option (or any similar option depending on the browser). Doing this will prevent sites from requesting such permissions in the future so you don’t accidentally allow them to disturb your browsing with their pop-ups, banners and ads.

If after you completed the previous two suggested methods the problems with Ammi Setup Native continue, this would typically indicate that the hijacker has been installed inside your computer and you’d need to go a bit deeper to fully eradicate it. The following steps will guide you through this process and let you rid your PC of the undesirable browser hijacker.
![]()
The first step of this part of the guide is to try to find the process of the hijacker from the Task Manager’s processes tab. To access the Task Manager app, you can press together the Ctrl, Shift, and Esc keys and the Task Manager will open. Once inside it, select the Processes section and look for the Ammi Setup Native process, for other processes that have a similar name, as well as for processes that generally seem questionable and suspicious to you. For instance, if there is a process in the Task Manger that uses very high amounts of Processing (CPU) power and/or RAM memory and if that process isn’t run by a program that is presently open on your computer or by a program that you know is safe, then that process could also potentially be linked to the Ammi Setup Native hijacker.
An important thing to do when you think a given process may originate from the hijacker is to look up the name of said process. In some instances, users may mistake legitimate OS processes for suspicious hijacker-related ones so it is important to first determine if a given process you deem suspicious isn’t actually run by your OS because if you end such a process, this may cause further problems in the system.

Once you have ruled out the possibility that the suspicious process in the Task Manager is from your OS, then you should proceed to select that process, right-click on it, and Open its File Location. The files in the newly-opened folder must be scanned for malicious code. To scan them, you can use the antivirus or the anti-malware tool you have on your computer or you can try out the free malware scanner we have provided down below:

Of course, you can scan the files both with your own security tool and with the online scanner, which is something we’d actually suggest for best results. If during the scanning process it turns out that any of the files are determined to contain malicious code, you should go to the suspicious process, select it, and then click on End Process to quit it.
After that, go to the file location of that process and delete the entire folder. If you are not permitted to do this because some of the files stored in the folder cannot be deleted, remove the other files and proceed with the next steps. Once you are finished with the whole guide, you will come back to this folder and you will then hopefully be able to delete the remaining files that you weren’t allowed to remover earlier.
![]()
Before you move on to the next steps, we advise you to boot the computer into Safe Mode as this could help with the removal process by preventing the hijacker from interrupting your attempts to delete the latter. Follow the provided link above if you need help with accessing Safe Mode.
![]()
Once you have entered Safe Mode, go to your Start Menu, type Uninstall a Program in it, and press the Enter key. Once the Uninstall a Program window opens, try to find the app or program that may have brought Ammi Setup Native to your PC. You may or may not see an item with the Ammi Setup Native name listed there – if you do, select it and then click on Uninstall at the top to delete that program. If there is no program named Ammi Setup Native in that list, look for other items that may be related to the hijacker. If, for instance, you notice a program in that list` you don’t recognize and that may have been installed automatically on the computer without your informed permission, this could also be linked to the hijacker so it should be uninstalled. Also, look at the installation dates of each program – normally, the one related to the hijacker would have been installed right before the disturbances in your browser started to occur.

Once you click on Uninstall, follow the prompts from the uninstallation wizard and if you come across the following dialog box, click on NO or else you may get more unwanted software installed on your PC.

![]()
For this next step, search for System Configuration in the search box under the Start Menu and click on the first icon shown in the results. Then go to the Startup tab where you will see items representing apps that start automatically when Windows loads. If any of the apps listed there carry the name of Ammi Setup Native or seem like they could be related to the hijacker, uncheck them. Do the same with any item with an Unknown manufacturer unless you are sure that the item is trusted and is not related to Ammi Setup Native.

After you uncheck the suspicious apps, click on Apply and then on Ok.
Next, copy the following line of text and paste it under the Start Menu. Hit Enter and a file named Hosts will open up: notepad %windir%/system32/Drivers/etc/hosts.
You must look at the bottom part of the text and see if there is anything written below “Localhost“. Normally, there should be nothing there but since you have a hijacker on your PC, there may be some strange IP addresses listed below Localhost. Copy anything you see there and send it to us in the comments and we will tell you if the lines you copied could be related to Ammi Setup Native.

If we tell you that the IP addresses you see below Localhost may have something to do with Ammi Setup Native, go back to the Hosts file and delete those addresses from it. Once you are done, save the changes to the file by pressing Ctrl + S from your keyboard.
![]()
For this step, search for Network Connections in the Windows search field, open the first result, and right-click on the icon of the network that your machine is currently connected to. Select the Properties option from the context menu, click on the Internet Protocol Version 4 (ICP/IP) entry, and click on the next Properties button. In the next window, select the Obtain DNS server addresses automatically if that option hasn’t been selected already and then click on Advanced. From the Advanced window, go to the DNS tab and in there delete all listed DNS server addresses (if there are any). Once this is done, click on OK on all of the open windows and proceed to the final step of this guide.

![]()
You will now have to make some changes to your PC’s Registry by deleting items from it that may be linked to Ammi Setup Native. Since there are some very important system settings and data stored in the Registry, you must be really careful not to delete the wrong thing because, if you do, there may be some pretty severe unforeseen consequences for the state of your PC. Therefore, we strongly suggest to always consult us through the comments section when in doubt about a given item you are not sure whether you should delete.
Now, to get to the Registry Editor, press Winkey + R, type regedit in the small search box and then hit Enter. The system will ask for your Administrator permission so click on Yes to proceed to the Registry Editor. Once you are at the Editor, press Ctrl + F to evoke the search field and type the name of the hijacker (Ammi Setup Native). Click on Find Next to search for items in the Registry that have the hijacker’s name. If anything is found, select the item and then delete it by pressing the Del key. Keep clicking on Find Next and deleting the found results until there is nothing left that has Ammi Setup Native in its name.
Lastly, check these following Registry directories for folders that may have been added by the hijacker. Such folders would normally have very long names that seem like a randomly-arranged sequence of characters. Here, it is best to tell us about the folders you think should be deleted by telling us their names in the comments so that we can confirm that they indeed must be removed from the Registry of your computer.
- HKEY_CURRENT_USER/Software/
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/
Once you have completed all the steps, go to the folder from Step 1 (the file location of the hijacker process) and try deleting the files that you weren’t able to remove earlier (if there were such files). Hopefully, you will now be allowed to delete the remaining files that are stored in that folder alongside the folder itself.

Leave a Comment