Answer PCAP
The specific piece of malware we are about to tell you about is named Answer PCAP, and it is a brand new Trojan Horse infection. Due to having been recently released, many antivirus programs may not yet be equipped to detect and handle this malicious program – Answer PCAP may not currently be present in their databases, meaning that it won’t get detected on a computer that uses such an antivirus.
This, in turn, makes dealing with Answer PCAP even more challenging. The longer it stays on a given computer without getting spotted, the worst the consequences of its stay in the machine may become. If you are here because you have spotted this malicious program in your computer, you may yet have a chance to deal with it with minimum harm done to your system or to your virtual privacy. However, you really cannot waste any time, and procrastinate the malware’s removal. As soon as you finish reading this post, you should begin the removal process by taking a look at the guide below, and starting to complete the steps given in it. If you don’t think you will be able to complete everything, or if the manual instructions aren’t enough to rid your computer of the Answer PCAP Trojan, you can also try to use the removal tool we’ve linked inside the guide. It is a tested anti-malware program, capable of handling such threats.
What you can expect from Answer PCAP
In many cases, damage to the system is actually a byproduct of a Trojan Horse’s attack, and not the main goal of the infection. Oftentimes, the malicious program would be focused on stealing your banking details, and online accounts, or spying on your conversations, and other activities you do online. In other cases, the Trojan would initiate processes in your system that restrict your access and control, and others that force the computer to use all of its resources (RAM, GPU, CPU) to mine cryptocurrency for the hacker’s profit. This use of Trojans like Walliant, Great Discover, in particular, is likely to make your machine nearly unusable due to the constant exploitation of most of its resources. The machine would probably be way too slow for you to effectively do anything in it. Backdoor activities are also within the abilities of some Trojans. Backdooring is the process of sneaking another malicious program in an already infected device. For example, this is how many Ransomware cryptoviruses get distributed – via the help of backdoor Trojans.
We could go on and on about the different abilities of such threats, but we can’t cover everything in such a short article, which is why we will instead now give you the removal guide that can help you eliminate the insidious piece of malware. Just remember that Trojans oftentimes disguise their processes and files as ones coming from your system. This increases the risk of deleting some important system file or ending a crucial system process while trying to remove the Trojan, so it’s best to first consult us in the comments if you aren’t sure about whether or not you should delete something. Another option is to scan your computer with the removal tool we already mentioned – it will tell you if something is dangerous and needs to be removed.
SUMMARY:
| Name | Answer PCAP |
| Type | Trojan |
| Detection Tool |
Remove Answer PCAP Virus
To remove the Answer PCAP virus, you must search the system for rogue programs and processes and delete them and then you must restore the system settings.- Look in the Control Panel’s Uninstall a Program section and if you find any sketchy programs there, uninstall them.
- Search for suspicious processes in the Task Manager and remove the ones you think may be rogue.
- Restore the Startup Items, DNS, and Hosts file settings if any of them have been modified by the virus.
- Finally, open the Registry Editor, search for malware entries, and delete them to remove the Answer PCAP virus.
Extended Guide If you bookmark this page, this would make it easier to find it later, after you restart your computer, since system restarts will be needed during the guide. Therefore, it may be a good idea to bookmark the page in your browser.
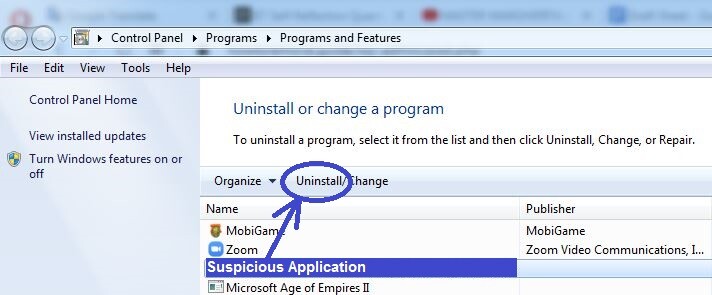
Step 1 Trojans often enter the computer helped by a seemingly legitimate program. Therefore, the first step is to search your PC for programs that may be responsible for allowing Answer PCAP to enter your system and delete any such programs. To do that, you must go to the Control Panel (from the Start Menu), and click on Uninstall a Program. The list that appears on your screen contains all programs on your computer – look through it and pay close attention to the items installed not long before Answer PCAP started showing its symptoms. If you think that there are any suspicious programs in that list that may be related to Answer PCAP, uninstall them by clicking their entries from the list, selecting the Uninstall option from the top, and then proceeding with the steps from the uninstallation wizard. If the uninstallation wizard gives you the option to keep anything related to the suspicious program (including personalized settings), choose not to keep anything.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
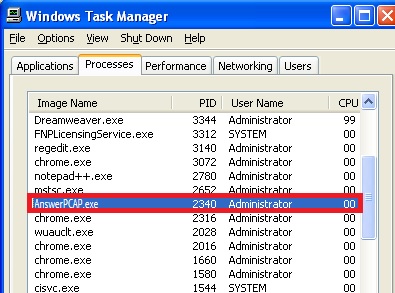
Next, you must try to find any potentially malicious processes running in your system and disable them. You can do that from the Task Manager utility. Search for it in the Start Menu and when you open it, select the Processes section, where you will see what processes are currently active on the computer. Focus on the ones with the highest virtual memory and CPU consumption – see if among them there are any items with unusual or unfamiliar names and if anything looks liek a potential threat, see what information you can find about it on the Internet. In most cases, if a given process is linked to a Trojan Horse virus, this should quickly come up in the search results once you look up the processes’ name.
If you find any posts or articles from reputable sources that say the process you looked up may be linked to Answer PCAP, then right-click the process, select the Open File Location option, and scan each file from the folder that shows up using the powerful and free online scanner that can be found below.


If the scan results for any of the tested files report malware, then immediately quit the process they are coming from by right-clicking it, and selecting End Process.
Next, delete the process’ files as well as its entire file location folder. If an error message appears when trying to delete a given file, come back at the end of the guide and try to delete that file once again – by that time, the error message should no longer appear when you try to delete it.
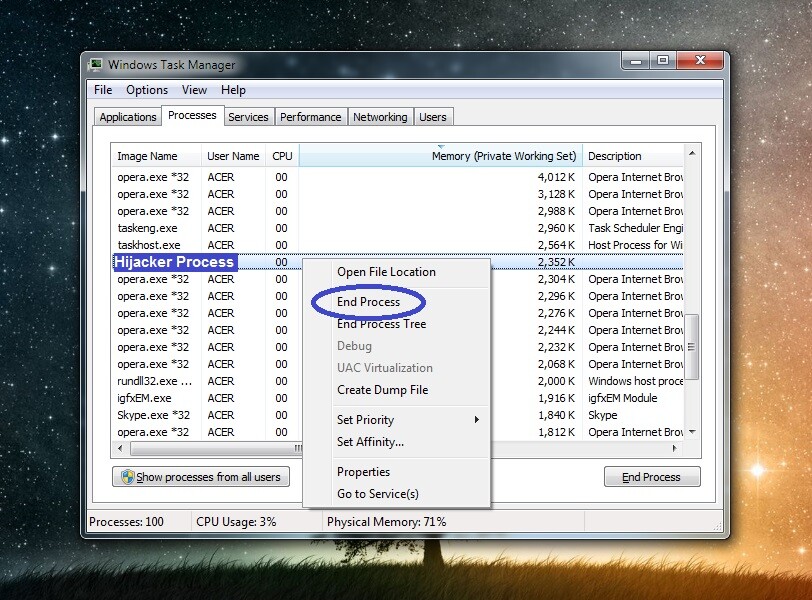
Note: If you are certain that the suspected process is unwanted, quit it and delete its data even if its files do not get flagged as threats.
Step 3 Put your computer in Safe Mode to keep any processes you may have failed to find and quit during the last step from preventing you from completing this guide and removing the malware.
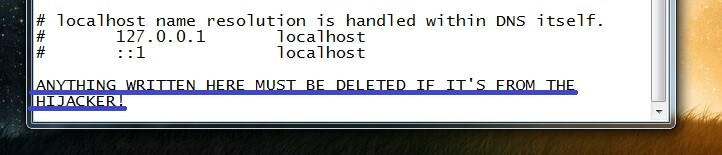
Step 4 Open the Start Menu, paste this line “%windir%/system32/Drivers/etc/hosts” in it, hit Enter, and if you are required to choose what program to use to open that file, opt for Notepad. When the file (Hosts) opens, see if there’s anything written in it after “Localhost” and if there is, copy it and post it in the comments. We will take a look at your comment and determine if the text you’ve sent us from your Hosts file indicates that the file has been hijacked. If it turns out Answer PCAP has modified the file, you will tell you about it, and you will have to delete everything that’s after “Localhost” from the file, and then save the changes.
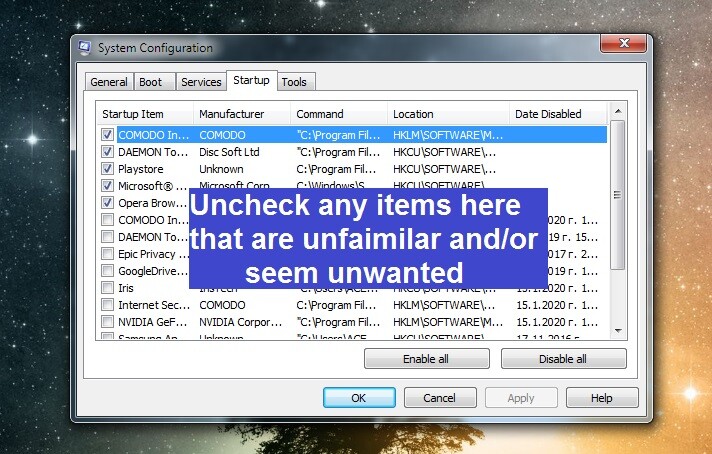
 Again open the Start Menu, type system configuration, click on the first shown item, and open the Startup tab. There, check the list of items, see if any of the entries look odd, unusual, suspicious, or unfamiliar, and uncheck them. Then click on OK to save the changes.
Again open the Start Menu, type system configuration, click on the first shown item, and open the Startup tab. There, check the list of items, see if any of the entries look odd, unusual, suspicious, or unfamiliar, and uncheck them. Then click on OK to save the changes.
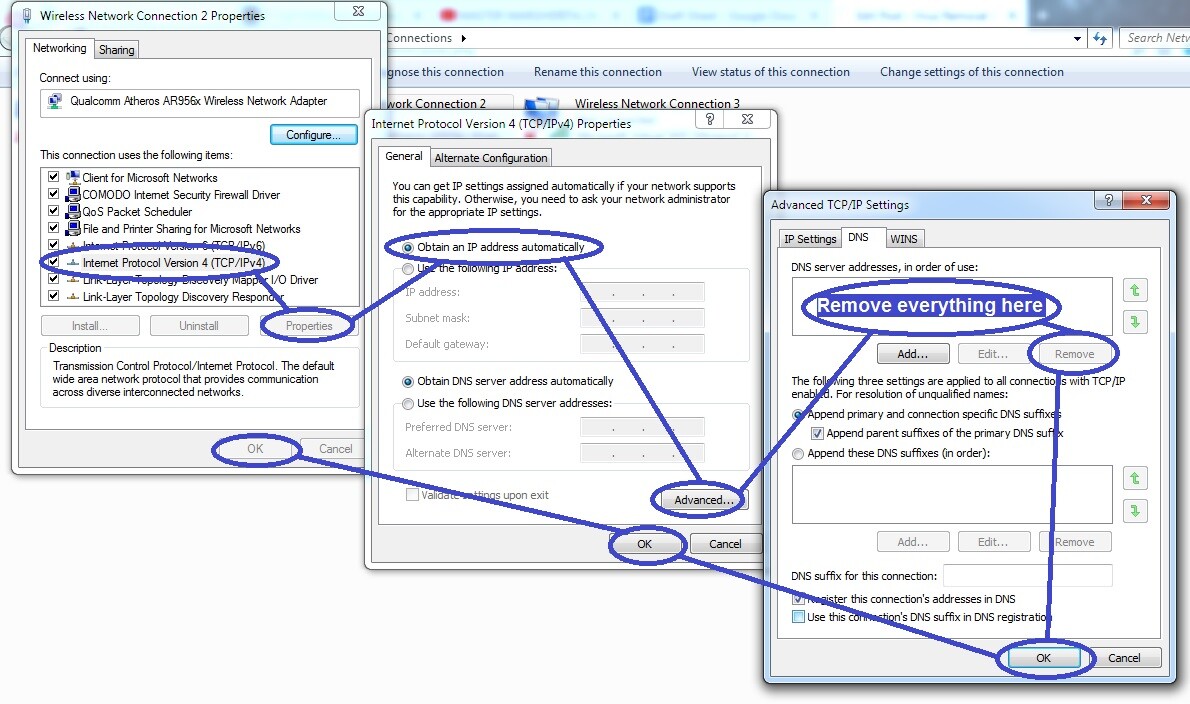
 For a third time open the Start Menu and use it to search for “network connections” – click on the first icon that appears in the results, then right-click on your network’s icon (the network that’s being used by your PC at the moment), and open Properties.
Next, find the item labelled Internet Protocol Version 4, select it, click on the next Properties button, and select Obtain an IP address automatically (if the option is currently not enabled). After that, select the Advanced button, open the DNS section from the top, and if you see any IPs listed in the list there, remove them, and click OK on everything.
For a third time open the Start Menu and use it to search for “network connections” – click on the first icon that appears in the results, then right-click on your network’s icon (the network that’s being used by your PC at the moment), and open Properties.
Next, find the item labelled Internet Protocol Version 4, select it, click on the next Properties button, and select Obtain an IP address automatically (if the option is currently not enabled). After that, select the Advanced button, open the DNS section from the top, and if you see any IPs listed in the list there, remove them, and click OK on everything.
Step 5 Press together the Winkey and the R key from the keyboard and then type regedit in the Run window that pops-up. Hit Enter and then, when asked for a permission, click on Yes. This should open the Registry Editor utility – when it opens, click on the Edit menu, and then select Find. In the Find search box, type Answer PCAP, click Find Next, and delete what gets found. You should keep repeating the search and deleting what items get found for as long as there are rogue items related to Answer PCAP in the Registry. Be warned, however, that you must only delete items that are from Answer PCAP and nothing else – if you don’t know if a given item is from the virus, be sure to first ask us through the comments instead of directly deleting something that maybe shouldn’t be deleted. Otherwise, you may cause damage to your system that may be difficult to repair.
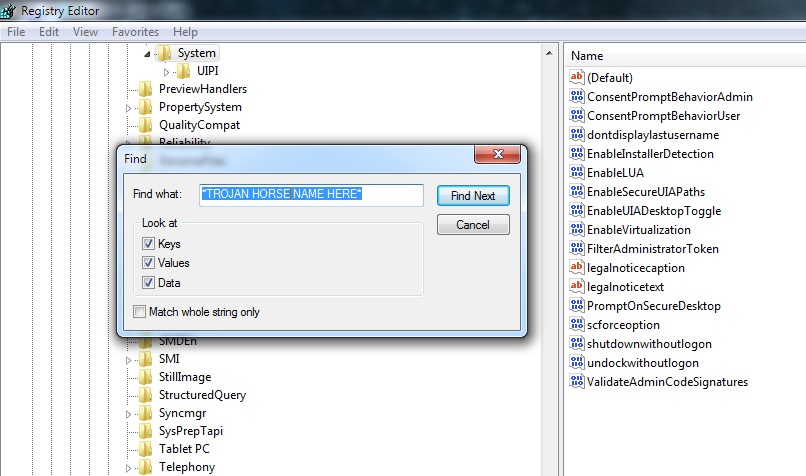
Lastly, find these next Registry locations in the left panel and see if there are any (sub)folders in them that have very long names made out of randomized characters. For example, if you see anything like this: “adf99g70dtq0as7g03fur89tye0r309f90q“, you should probably delete it.
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main

Leave a Comment