The Malicious AnyDesk File
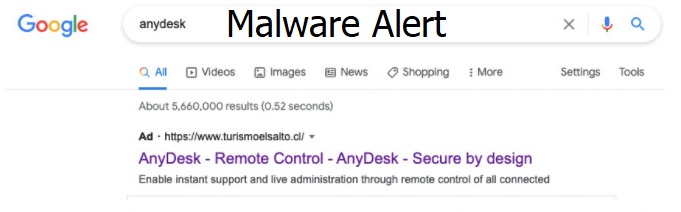
A sophisticated malvertising campaign targeting AnyDesk, a popular remote desktop access solution, has been revealed by cybersecurity researchers this week. Experts reported that they have detected a malicious installer camouflaged as an AnyDesk remote desktop software that has been distributed on the web through rogue Google advertisements. The malicious ads spreading the weaponized software installer appeared in Google search results, according to reports.
The malware distributing campaign is believed to have started on 21st of April 2021, and consists of a malicious file pretending to be an AnyDesk (AnyDeskSetup.exe) executable. Once downloaded and executed, however, this file downloads a PowerShell implant that can be used for collecting and exfiltrating different types of data from the compromised system.
As of the time of this writing, the malvertising attack targeting AnyDesk has not been linked to any specific malicious actor. Based on the available details, professionals are assuming that this is a widespread campaign that is aimed at a wide range of customers. As per details on AnyDesk’s website, its remote desktop software solution has more than 300 million users from all over the globe, which is a large user base to target.
Researchers explain that the malicious AnyDesk installer is served to unsuspecting Google users who are searching for “AnyDesk” through the search engine with the help of malicious ads placed by the criminal actors in the search results.
As soon as the users click on the malicious ads in the search results, they are redirected to a specially crafted page that looks exactly as the AnyDesk official website. Google has been contacted in regard to the discovery and has reportedly taken immediate steps to draw the malicious ads down.
Malvertising has been an effective way to lure users into downloading malware for many years, but this new example of a malicious usage of Google Ads seems to be a more powerful and sophisticated tactic to acquire widespread shell deployment, since it enables cybercriminals to directly target specific companies and their users.

They got me…. And I dimly noticed it went to a 3rd party ‘mega’ type file hosting service… Still ran it and it took out windows security and user account control as well as restarting the system immediately… I went airplane mode and am going to purge the disk as well as change my browser passwords