Apple Security Breach
Applications like Apple Security Breach “Virus” are a source of a very common browsing disturbance. They fall into the category of the Browser Hijackers and tend to invade users’ browsers in attempts to push their advertisements. Such applications typically integrate well with all the popular browsing programs, such as Safari, Chrome, Firefox, etc. and impose some changes of their browsing settings without the users’ direct approval.
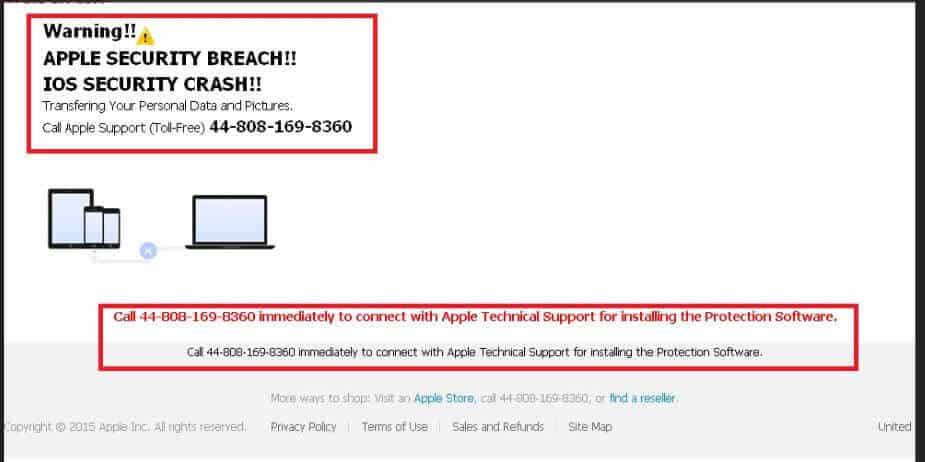
Apple Security Breach, for instance, may install a new toolbar or add a new search engine, set a new homepage or launch a page redirecting service without being authorized to do so. This hijacker may also generate numerous ads, pop-ups, banners and blinking boxes on your screen, which may appear every time you try to start a new browsing session. Basically, with all these changes, the nagging piece of software tries to promote certain sponsored web pages, products, services and offers by making sure with all possible means that you are exposed to them as much as possible.
In this article, we will try to provide you with a permanent solution to these changes and the browser hijacker that is causing them so if you are looking for help with uninstalling Apple Security Breach and removing all of its annoying search engines, toolbars, ads and homepage settings, stay with us. Our “How to remove” experts have prepared a detailed Removal Guide below specifically for this purpose. Before you scroll down to it, however, let us give you some more information about the nature of the browser hijackers, their danger level, their distribution methods and the possible issues they may cause.
What is the purpose of a browser hijacker like Apple Security Breach “Virus”?
Many users are concerned about the real intentions behind the annoying browser changes, the sudden page-redirects and the never-ending stream of ads. What could all these activities be after? Well, fortunately, the browser hijacker’s purpose is not to cause harm to your system or to perform some sort of a cyber crime. Its goal is to advertise certain pages, services, products and offers. Therefore, you should not regard such software as a virus. Unlike a typical threat, such as a Trojan horse or a Ransomware infection, an application like Apple Security Breach Virus typically serves online advertising purposes and not criminal ones. It generates money for its creators through revenue-gaining models such as Pay-Per-Click and Pay-Per-View. It does not have malicious code and cannot encrypt your data, corrupt your files or software in any way. In fact, most creators of such software are not criminals but legitimate software developers which simply benefit from the online advertising models and make money out of that.
The web users, however, may have issues with browser hijacking software because not only does it aggressively imposes browser changes and advertising content on their screen but it also oftentimes offers no useful features to make up for the intrusiveness from its aggressive advertising campaigns. Most of the hijackers rarely offer any useful feature in exchange for the browsing irritation they create and applications like Apple Security Breach are not any different. Such pieces of software may actually redirect you to various unfamiliar pages and make you spend all your time trying to remove ads from your screen. What is more, they may expose you to content, which might not be safe and this way may indirectly be the cause for an infection with a nasty virus such as Ransomware or a Trojan horse. Therefore, we generally advise our readers to limit their interaction with the content that the hijacker may display or to simply uninstall it as a preventive measure.
How to keep page-redirecting applications like Apple Security Breach “Virus” away from the PC?
Typically, a lot of browser hijackers can be found freely on the Internet. Such applications are usually available for free download from various freeware or shareware platforms, torrent sites, spam messages, ads, links, or some suggested software updates and installs. If you don’t want them to become part of your system, you should avoid such sketchy sources and download and install applications only from reputed developers and their official web pages. Another very important piece of advice that we have is to always pay attention during the setup process of any new software that you intend to install on your PC because sometimes, applications like Apple Security Breach might be promoted as additionally bundled or “recommended” components along with the main application. That’s why, you should make sure you check the setup customization options every time and manually disable any component which you may not want.
SUMMARY:
| Name | Apple Security Breach |
| Type | Browser Hijacker |
| Detection Tool |
Apple Security Breach “Virus” Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment