AvosLocker
AvosLocker belongs to the category of ransomware cryptoviruses. This means that AvosLocker encrypts the data stored on its victims’ computers, making it inaccessible to anyone not in possession of a special key.
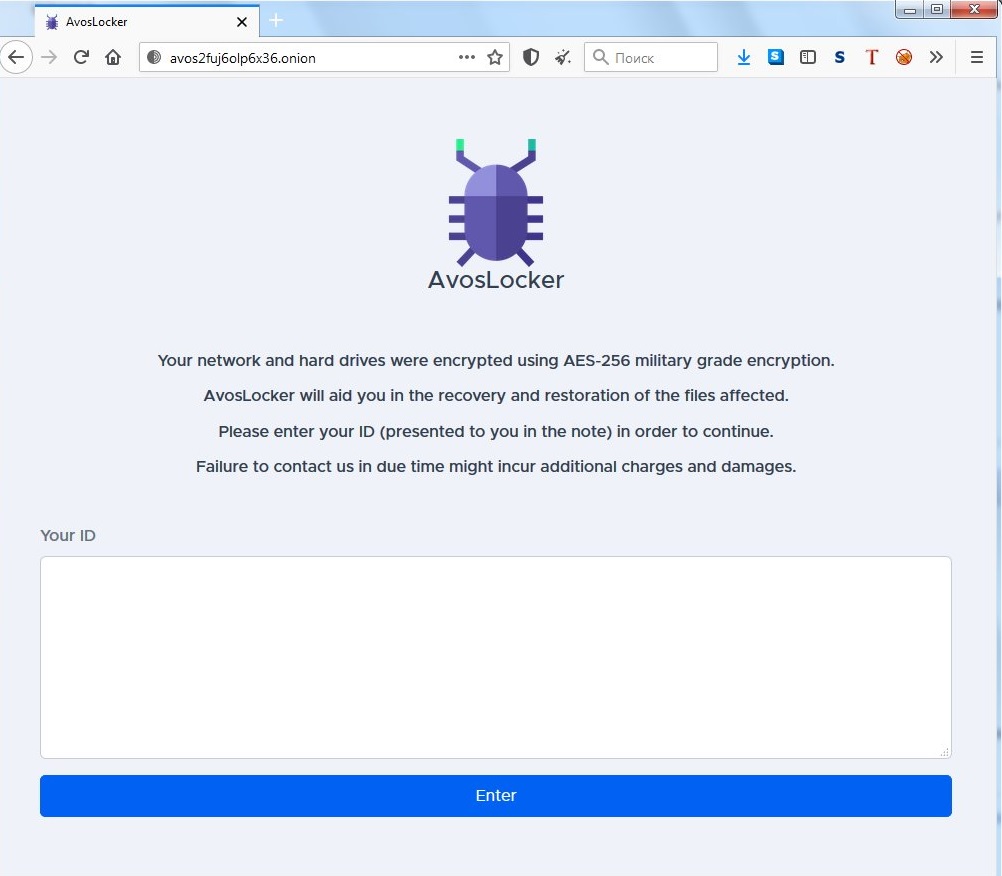
The AvosLocker ransom note
This special key is what the hackers behind this ransomware virus demand that the victims pay money for. And they usually take it a step further and threaten to destroy the key if the money isn’t paid within a certain deadline, for example, or something along those lines. This is a common scare tactic used to throw users off balance and not give them time to think for themselves. The truth is, the decryption key that the hackers have isn’t the only means of getting your files back. There are others, and we have mentioned them in the second part of the removal guide below.
But know that in any event, there’s nothing that will guarantee the successful restoration of your data. Whether you pay the cybercriminals or decide to take an alternative approach, there’s always the risk that you may not be able to recover your files. This is what makes ransomware among the most dangerous, if not the most dangerous, category of malware. Whatever you choose to do, though, it’s vital that you first remove AvosLocker from your system, and the guide below will show you how to do that.
The AvosLocker virus
The AvosLocker virus is notoriously stealthy and will, in most cases, not even trigger your antivirus system. This is one of the main advantages of the AvosLocker virus over other types of malware, and over us users, of course, as well.
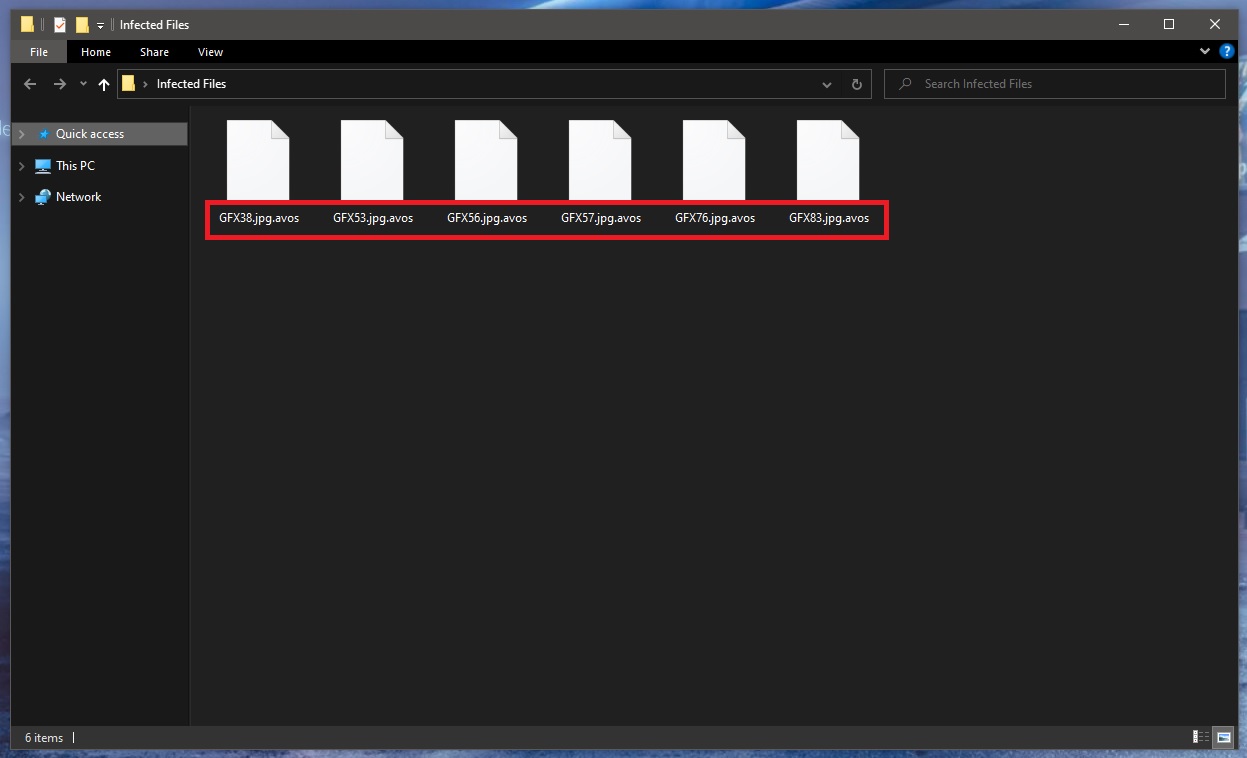
The .avos ransomware encrypted files
The thing is that encryption is not an inherently malicious process, and therefore most antivirus programs, even the ones with all the latest bells and whistles, will let it slide under their radars. And aside from that, the encryption process runs without any noticeable symptoms anyway. So in most cases, users won’t know what hit them until it’s’ already too late and the malware reveals itself with the help of the ransom note that it usually places on the desktop of the infected computer.
With this mind, the only real chance users have of protecting themselves from ransomware like AvosLocker, Moqs, Guid is by preventing the attacks. And for the most part, practicing basic safety measures when browsing the web and using your common sense is enough to avoid such attacks. Don’t interact with suspicious content, stay away from unsafe web locations, and be sure that any incoming emails or other messages are 100% safe before you open any attachments or links that they may contain. In addition, we highly recommend keeping copies of your files on a separate drive so that even if you do get infected again, you will have safe backups available to you.
The AvosLocker file extension
You will notice that all the encrypted files have an unfamiliar suffix at the end of the file name – this is the AvosLocker file extension. The AvosLocker file extension is essentially what ensures that no program can recognize the format.
SUMMARY:
| Name | AvosLocker |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove AvosLocker Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt AvosLocker files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

My wife and I are retired and work from home cleaning homes a business not worthy of any avoslocker ransomware attack extortion of money which we don’t have, can you help us decrypt our files that have been encrypted
Hi, Eric Garner! Firstly, we advise you to complete the guide from the current page in order to remove the malware and clean your PC or download copy of Spyhunter and scan your PC. You should archive your encrypted files on an external HD in hopes of some future breakthrough. It is also possilble the criminals will release the keys for their ransomware, or law enforcement could nab the criminals and/or their servers and release the keys.