Banjo
Banjo is the name of a dangerous Ransomware-based cryptovirus which is part of the Phobos family. Unlike other computer threats, such as Trojans or Spyware, which try to secretly perform something malicious which can benefit the criminal creators and compromise you, this virus tries to extort money out of its victims with a different strategy.
It secretly sneaks in the system and applies a special encryption code to a number of files which are considered as valuable for the user. Typically, the files that become a target of the encryption are commonly used file types such as documents, images, audios, videos, archives, spreadsheets and more.
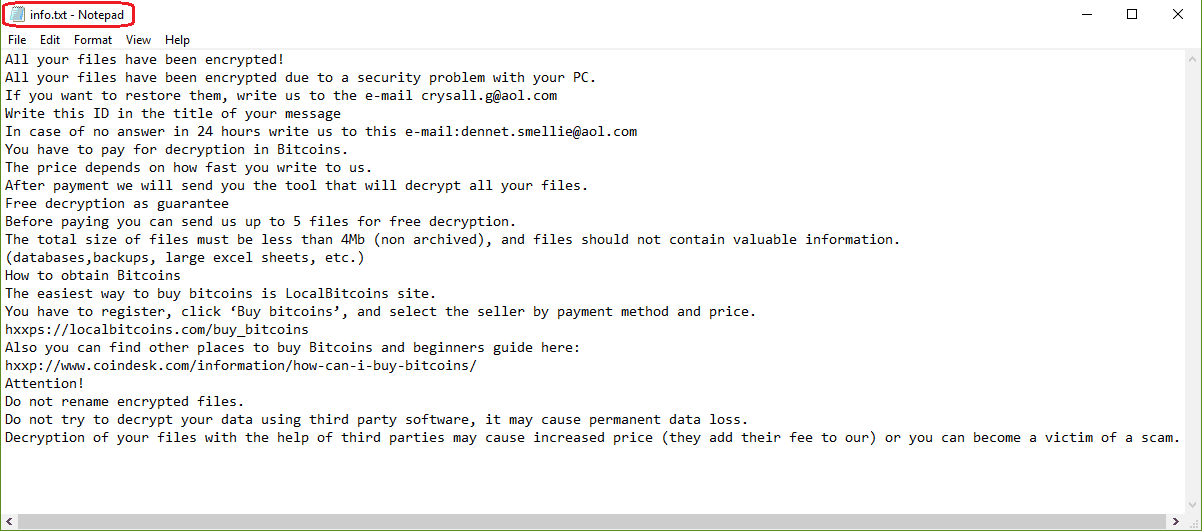
Once they become encrypted, they remain on the system but the victim cannot open or use them in any way. To recover them, the Ransomware requires a ransom payment via bitcoins or another cryptocurrency. The amount of money that the hackers who stay behind Banjo usually ask for may vary, but there is no guarantee that it will not increase over time. According to the ransom-demanding message which usually gets displayed by this dangerous program right after the file-encryption process has completed, the people have only a short period of time to pay the ransom and regain their access to the locked files. Those who strictly fulfill all the hackers’ demands are promised to receive a special decryption key to reverse the applied encryption.
Can the .Banjo virus cause damage if you have backups?
Fortunately, Banjo cannot hurt those who back up their data and keep copies of their files on an external drive regularly. If you have copies of photos, business documents, and other files which you store on a removable HDD or cloud storage, you do not have to pay a ransom. The only thing you have to do is to correctly detect and remove the Ransomware from your computer and prevent further damage.
To remove Banjo quickly and safely, you are advised to scan your computer with an updated professional malware removal tool. Alternatively, you can do that manually if you carefully follow the instructions in the Removal Guide below.
.Banjo file-recovery suggestions
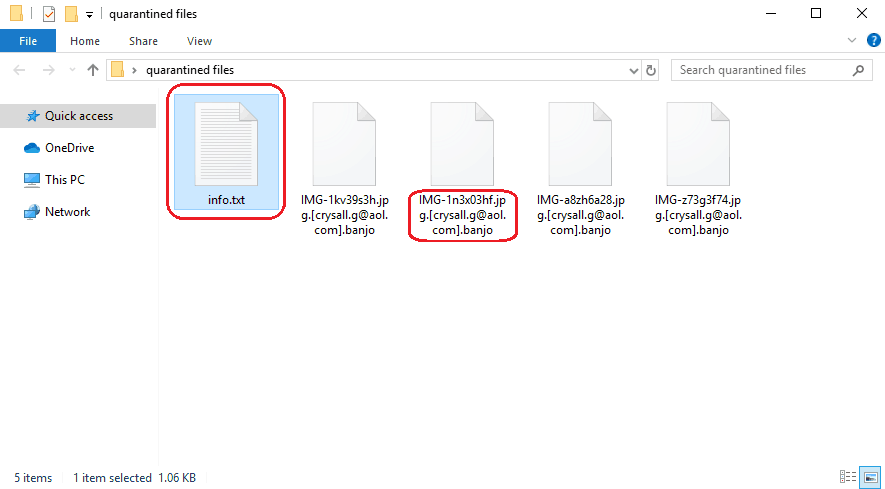
A screenshot of an encrypted .Banjo File.
In case you don’t have backup sources to recover your files from, you may want to explore some of the file-recovery suggestions mentioned in the guide. We feel obligated to tell you that paying the ransom and hoping that the hackers behind Banjo will send you the decryption key for your data is not a good option. First of all, this can lead to a loss of money since there is absolutely no guarantee that you will actually receive something in exchange for your payment. The crooks may simply disappear without sending you anything. Or, even if they send you the key, there is still a chance that it may not work properly and it may fail to decrypt the applied encryption. So please consider those risks and explore other available alternatives which can help you remove the infection and recover from its attack. Not to mention that giving your money to the anonymous hackers only encourages them to keep blackmailing you and sponsors the creation of more Ransomware.
SUMMARY:
| Name | Banjo |
| Type | Ransomware |
| Detection Tool |
Remove Banjo Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment