*Bbnm is a variant of Stop/DJVU. Source of claim SH can remove it.
Bbnm
Bbnm is ransomware of the file-encrypting type. Bbnm is highly dangerous and infects one’s system without any recognizable symptoms. The effects of this category of malware can prove to be incredibly devastating as a result of their activity may permanently deprive users of certain valuable data.
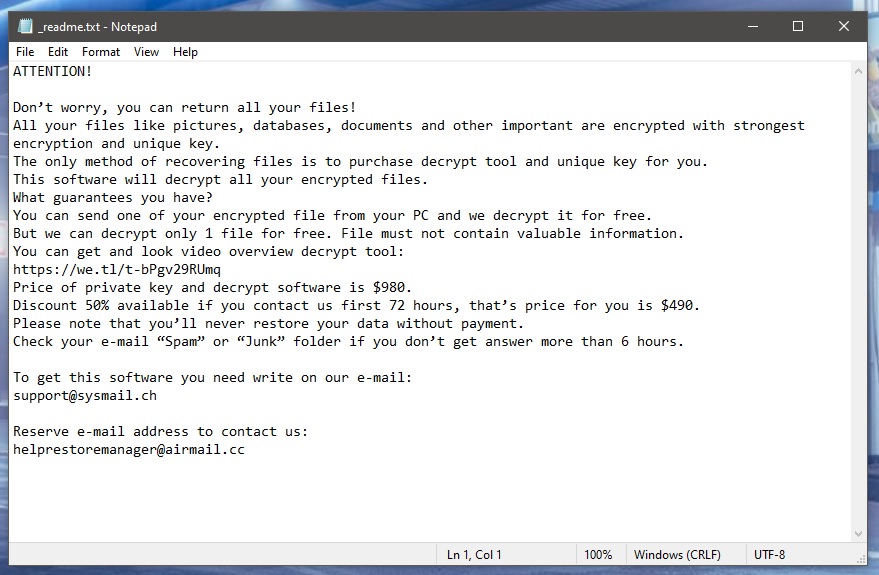
Yes, the criminals behind Bbnm, Hhjk, Jhgn have surely already informed you that you can get your encrypted files back after you’ve paid a certain amount of money. But in reality, those might as well just be empty promises. Unfortunately, there is no one who can guarantee that your files will in fact be restored to their previous state. Encryption is a very complex process and the subsequent decryption is even more complex than that. So, say the hackers allowed a mistake somewhere in their code – that would automatically render it completely useless and you will have spent your money on nothing.
That is why we normally advise users to go about this problem using other means. But those, too, aren’t 100% sure to help with the data that’s been encrypted. In any event, it’s best to try and see before you consider complying with the hackers’ demands. Most importantly, though, is that you remove Bbnm from your system before attempting any file recovery solutions. Below is a detailed removal guide that can help you do just that.
Bbnm virus
The Bbnm virus is often distributed with the help of another piece of malware, usually a Trojan horse. The Trojan acts as a backdoor for the Bbnm virus and ensures its passage into your system. For this reason, we recommend that you also scan your system for any possible Trojans after you have removed the ransomware.

You could have downloaded the Trojan horse virus from within an infected email attachment, for example. You could have received a fake invoice, payment request, or perhaps you were asked to click on a link so watch some scandalous or funny video. Alternatively, you could have clicked on some malvertisement that contained the treacherous piece of software. Either way, if this was the case, as soon as the Trojan entered your system it likely downloaded Bbnm onto your PC right away. And that is how you probably ended up with this rather serious problem on your hands.
.Bbnm file encryption
The .Bbnm file encryption is its most devastating asset. Namely, the .Bbnm file encryption is what ensures that no antivirus software can detect it and inform you about it.
And on top of that, it is such an elaborate process in itself that reversing it can be a challenge even for its creators. Therefore, we want you to have realistic expectations regarding the future of your encrypted files and consider the fact that they may possibly remain sealed for good.
Below are several tips that you can use in an attempt to restore your data. But before you move on to those, please be sure to first eliminate Bbnm from your system completely. Only then will it be safe to try system backups or extracting copies from other drives or cloud services.
SUMMARY:
| Name | Bbnm |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Bbnm is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Bbnm Ransomware

Please bookmark these instructions for the Bbnm removal in your browser so that you don’t have to keep searching for them again and again after each reboot of your system. Also, prior to moving to the next step, be sure to restart your infected computer in Safe Mode, so only the most essential processes and apps are running.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Bbnm is a variant of Stop/DJVU. Source of claim SH can remove it.
Find any suspicious processes in Task Manager by pressing CTRL+SHIFT+ESC on your keyboard. It’s important to keep an eye out for processes that don’t appear to be linked to any of your regular programs, as well as those that consume a lot of CPU and RAM resources without any apparent reason. Right-click on any suspicious process and select Open File Location from the pop-up menu in order to view its files.

The free online virus scanners listed below can be used to check suspicious-looking process files for malware. Drag and drop the contents of the File Location folder of the suspected process in the scanner to check it.

Make sure to delete any potentially harmful files after the scan is complete. Before deleting any files, however, first right-click on the suspicious process and select End Process from the quick menu to end it.

In the third step, use the command msconfig by typing it in the Windows search bar. Then press Enter and open System Configuration. The Startup tab will give you information about the apps that are set to start with your computer. If the tab contains Bbnm-related startup items, your job is to uncheck their checkmarks to disable them.

It is also possible for malicious changes to be made to the Hosts file on a compromised computer. To check if that is the case with you, open the file and see what IP addresses have been listed under “Localhost.”
The Hosts file can be accessed if you press together Win key and R key and then paste the following line in the Run box:
notepad %windir%/system32/Drivers/etc/hosts
Press Enter and let us know if you notice any suspicious IP addresses in the file under Localhost, as shown in the image below. A member of our team will take a look these IPs to see if they pose a risk.


*Bbnm is a variant of Stop/DJVU. Source of claim SH can remove it.
To avoid detection by anti-malware programs, malware authors are increasingly creative at inserting harmful registry entries into the system. As a result, we recommend checking your registry with the help of the Registry Editor to see if any harmful files have been added. You can do that if you go to the Windows search bar, where you’ll type Regedit and hit Enter. Next, open the Registry Editor’s Find window (press CTRL and F at the same time) and search for files associated with the ransomware that has infected your computer by typing its name in the Find box, and then click Find Next.
Remove any ransomware-related search results. After the first result has been found and removed, the registry can be searched again for other files with the same name.
Attention! Damage to your operating system may occur if you mistakenly remove non-ransomware-related files while clearing the registry. That’s why you should use a reputable anti-virus program to safely rid your computer of potentially harmful software and registry entries.
The following locations should also be manually checked for malicious entries. If you want to open one at a time, type each exactly as it is shown in the Windows search bar and press Enter.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete any files that appear to be suspicious and were recently added to these locations. Press Del to delete all of your system’s temporary files from your Temp directory.

How to Decrypt Bbnm files
People who have had the ransomware removed, face the next challenge which is regaining access to their encrypted data. If you’ve been attacked by ransomware, the methods used to decrypt your data will also vary depending on the variant of malware that has infected your computer. Ransomware variants can be identified by the file extensions they add to the encrypted files.
An anti-virus scan of the infected computer with a professional malware removal program (like the one on this page) should be performed prior to any file recovery attempts. You can then safely test various file recovery methods and connect backup sources to the virus-free and ransomware-free computer.
New Djvu Ransomware
There has been a recent discovery of a new Djvu ransomware variant named STOP Djvu. The .Bbnm suffix that this infection adds to the encrypted files makes it stand out from other malware. The good news is that it’s possible to use an offline key decryptor like the one at this link below to decrypt encrypted data.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
After you’ve downloaded the STOPDjvu.exe file from the link above, right-click it and select “Run as Administrator”. Then, read the license agreement and any accompanying brief instructions, so you can begin decrypting your data. Please be aware that this tool cannot decrypt files encrypted using unknown offline keys or online encryption.
The anti-virus software on this page can quickly and easily remove the ransomware if you find yourself in trouble. Additionally, you can use a free online virus scanner to see if there are any suspicious files on your computer.

Leave a Comment