*Source of claim SH can remove it.
Black Basta
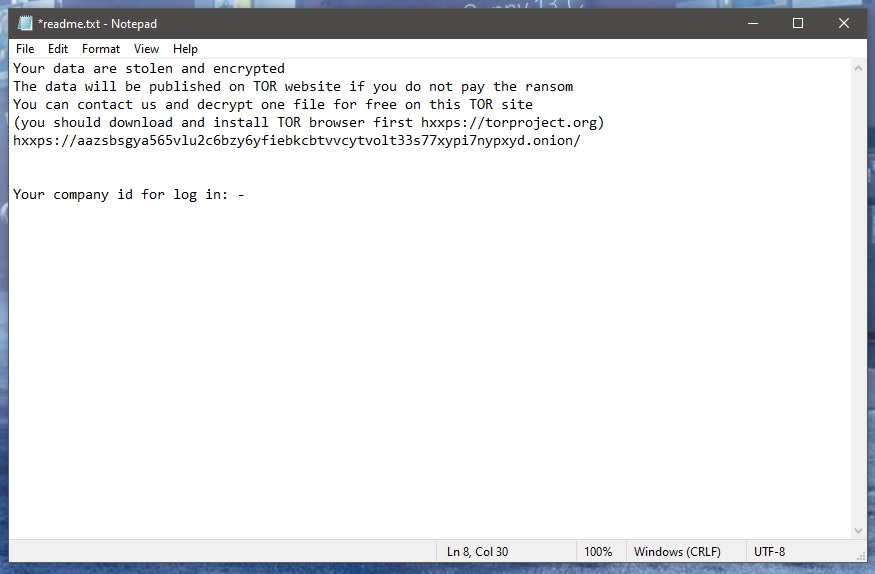
Black Basta is a dangerous ransomware virus that encrypts the files on the computers it infects. And Black Basta is called ransomware because it then requests a ransom payment from the victim users in exchange for decrypting those files.
Unfortunately, ransomware like Black Basta, Dewd, Jhgn is a very common type of malware and over the past few years its numbers have been increasing exponentially. It also happens to be a very lucrative criminal scheme that offers the hackers behind it the perfect cover of anonymity. Hence, they almost always get away with their crimes. On top of that, the viruses themselves are extremely harmful in and of themselves. Imagine losing access to all your important corporate data if you’re a large business for example, such as client databases, tax and revenue documentation, banking details, etc. And of course, the effects are just as devastating for private persons as well.
This is why we’ve designed a special removal guide to help you remove Black Basta from your system and potentially recover your files without having to pay the shameless criminals behind it.
The Black Basta virus
The Black Basta virus acts in total stealth and normally doesn’t show any symptoms. Therefore, most antivirus software is incapable of detecting ransomware like the Black Basta virus.

However, on certain occasions, it may be possible to spot the ongoing infection process. It can sometimes cause a significant system slowdown, especially in cases where the infected computer doesn’t have much processing power and/or has a large amount of data stored on it.
If this happens, you might be able to see an unfamiliar process drawing on most of your PC’s CPU and RAM in the Task Manager. And should that ever be the case, you must immediately force shutdown your computer and get in touch with a specialist for further assistance. This will stop the encryption process in its tracks, but do no attempt to switch the system back on yourself, as the virus will resume its activity and there will be nothing you can do about it.
The .Basta file decryption
The .Basta file decryption requires a specific key that the hackers promise to send you after you’ve made the payment. However, there are no guarantees that the .Basta file decryption will actually work even with that key.
This is one of the main reasons why ransomware viruses are such a tremendous threat to people. The truth is that encryption is a very sophisticated thing and decryption is more sophisticated still. This is a tricky and complex code and even the slightest mistake in it can render the decryption code completely useless, leaving your files inaccessible forever.
There are certain decryptor tools out there that you can make use of, if available. But the only surefire way of getting your precious files is back is from backups. If you have any stored on a cloud or separate drive, use them only after you have first removed Black Basta from your computer. This is vital, as otherwise the virus will encrypt the backup copies as well.
SUMMARY:
| Name | Black Basta |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Source of claim SH can remove it.
Remove Black Basta Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Black Basta files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment