BlackByte
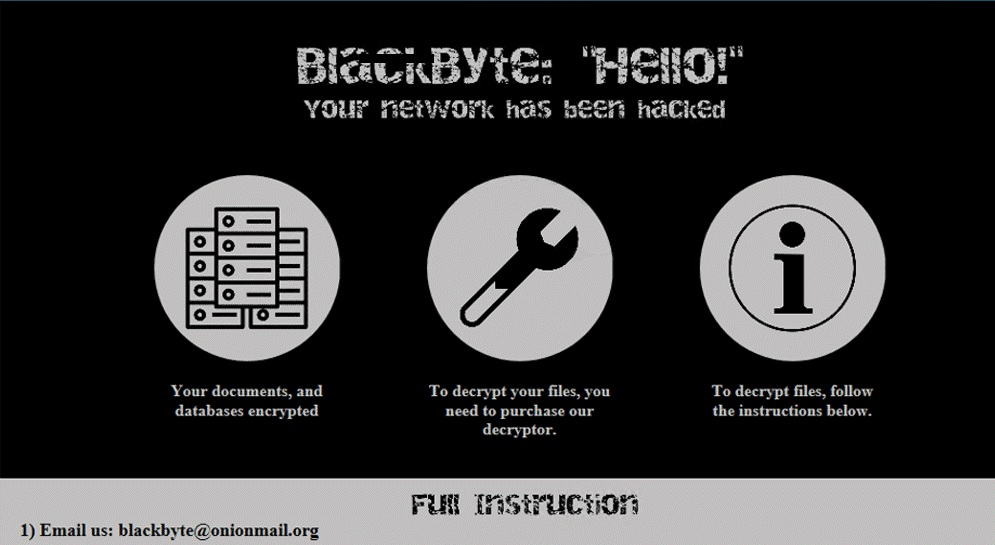
BlackByte is an infection based on Ransomware that attacks user files by applying encryption to them. The BlackByte victims are typically greeted with a ransom notification on their screen which requires money to decrypt their files.
The BlackByte Ransomware
This article and the removal guide below have been dedicated to BlackByte which is one of the new variants that belongs to the ransomware cryptovirus subcategory. This threat makes it difficult for the user to access their files. After infiltrating the victim’s device, the cryptovirus quickly encodes them all with a complex algorithm and requests a ransom to decrypt them. BlackByte or other ransomware viruses such as Moqs, Ufwj, usually show a ransom note on the infected computer which tell the victim to pay a fixed amount of money for a decryption key which is needed to unlock their data. The ransom notice can also include a deadline so that the victim is stressed to pay as soon as possible in fear of losing their files forever. But, if you are here, we presume you are not looking to pay a ransom to some criminals and want to know what your best choice is. Therefore, we encourage you to read the directions and use the removal guide at the end of the post.
The BlackByte virus
The BlackByte virus is sophisticated malware of the ransomware type that encrypts your personal files in a stealthy manner. The BlackByte virus may not be detected by standard antivirus software since it uses advanced techniques of infection and file encryption methods.
In the majority of cases, the web users get infected with ransomware by clicking on a compromised ad, an infected web link or a sketchy spam message. Unfortunately, you won’t know what is happening since the Ransomware attacks typically show no symptoms and can encrypt your file without interruption. The worst part is that the file encryption process cannot be recognized as something worthy of your attention even by the antivirus program on your computer. This is because it simply is not a malicious process at all. The antivirus software usually allows it to function as something completely legitimate because the file encryption, when not used in ransomware, is primarily a means of data protection.
The BlackByte file encryption
The BlackByte file encryption is a complex code that is applied to a variety of user files and keeps them inaccessible. Upon the completion of the BlackByte file encryption, a ransom will be demanded by the attackers.
Now that you are clearly not on this site for fun, you must be more concerned with how to remove the infection and how to possibly restore access to your files. We have already agreed above that paying a ransom to the hackers isn’t the best available option. After all, they are criminals and hoping for their help will be more naive than rational. That’s why it is much better to rely on your own efforts to remove BlackByte rather than wait for the crooks to send you a secret decryption key. Besides, as soon as you successfully remove the ransomware, you will be able to proceed with alternative file restoration methods. You can also connect your personal backup sources and copy your files from there. If you decide to go this road, our removal guide below can be of use, so don’t miss it. There is also a professional removal tool which can save you tons of time and delete BlackByte from your system.
SUMMARY:
| Name | BlackByte |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove BlackByte Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt BlackByte files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment