This page aims to help you remove .Bora for free. Our instructions also cover how any .Bora file can be recovered.
.Bora
.Bora is a sophisticated file-encrypting virus. You can get infected with .Bora by clicking on a random message or interacting with spam emails.
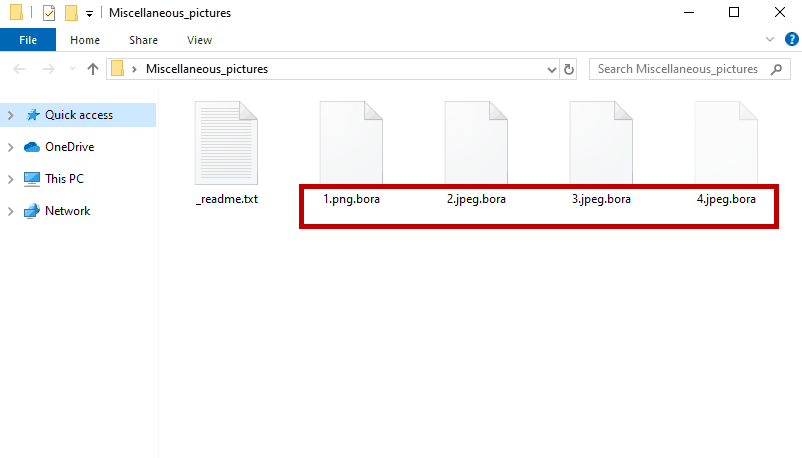
The .bora, once it finishes with the encryption.
You’re likely on this site because you came across a really upsetting message saying something about your files being encrypted or something along those lines. Perhaps, you have also been asked you to pay a certain amount of money to gain access to them.
If all this sounds familiar, then one of the nastiest malware pieces known as .Bora has infected you. This threat is a Ransomware and, as its name suggests, the infection requires a ransom in exchange for being able to use your computer and your files as usual. Sadly, these types of viruses are extremely widespread, and over the past several years, they have undergone exponential growth. We’ve put together the following guide to help you remove .Bora and potentially recover some of the encrypted files without paying a ransom.
The .Bora virus
The .Bora virus is a dangerous Ransomware that can take hostage of your files. Getting infected with the .Bora virus can happen in a second thanks to a careless click on an infected transmitter.
There are many methods of spreading Ransomware such as .Bora, and the most successful one seems to be through malicious emails. In most cases, what happens is that the victims receive either an attached file or a link inside an email that pretends to be legitimate. If they are not careful, the victims will typically download and open the file or click on the link because it might seem harmless. What they don’t know is that at that time the the Ransomware can automatically get downloaded to the device. Sadly, nothing will indicate the procedures that are going on, and until it’s too late, the victims probably won’t suspect anything.
The .Bora file encryption
The .Bora file encryption is a special code, applied to your files by the Ransomware. While the .Bora file encryption process is running, there typically are no symptoms that can give it away.
Once the encryption process completes, however, a scary ransom note normally gets displayed on the screen. The hackers behind it demand a ransom and promise to send you a special decryption key with the help of which to decrypt your files. If you are wondering what to do, however, we advise you not to; The main reason is, there is no assurance that the situation with your files will be improved after you pay. If such a key exists, the hackers behind .Bora may not have the intention to give you the decryption key you need to gain access to your data. At least, not until they extort enough of money from you. That’s why, there is a high chance they may not send you the key the very first time you pay. Instead, they may blackmail you for more money or send you a key that doesn’t work in order to make you purchase another one from them.
Therefore, we suggest you to keep your money and focus on how to remove the Ransomware in order to try some other file-recovery methods. Of course, we do not guarantee that our methods will work 100% either, but at least we won’t charge you for them.
SUMMARY:
| Name | .Bora |
| Type | Ransomware |
| Detection Tool |
.Bora Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment