This page aims to help you remove .Boston for free. Our instructions also cover how any .Boston file can be recovered.
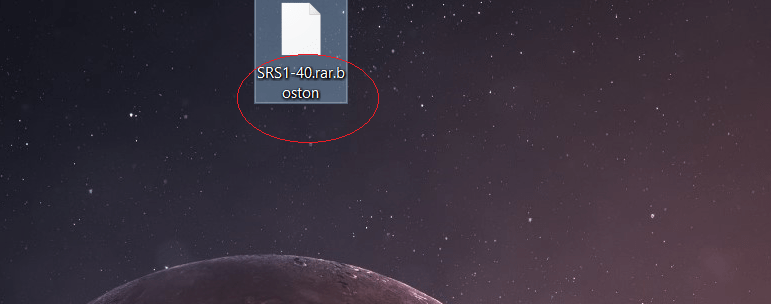
Welcome to our article about the malicious software virus labeled .Boston Virus Ransomware.This is the newset variant of the STOP ransomware, almost identical to previous versions such as .Heroset and .Pidon .
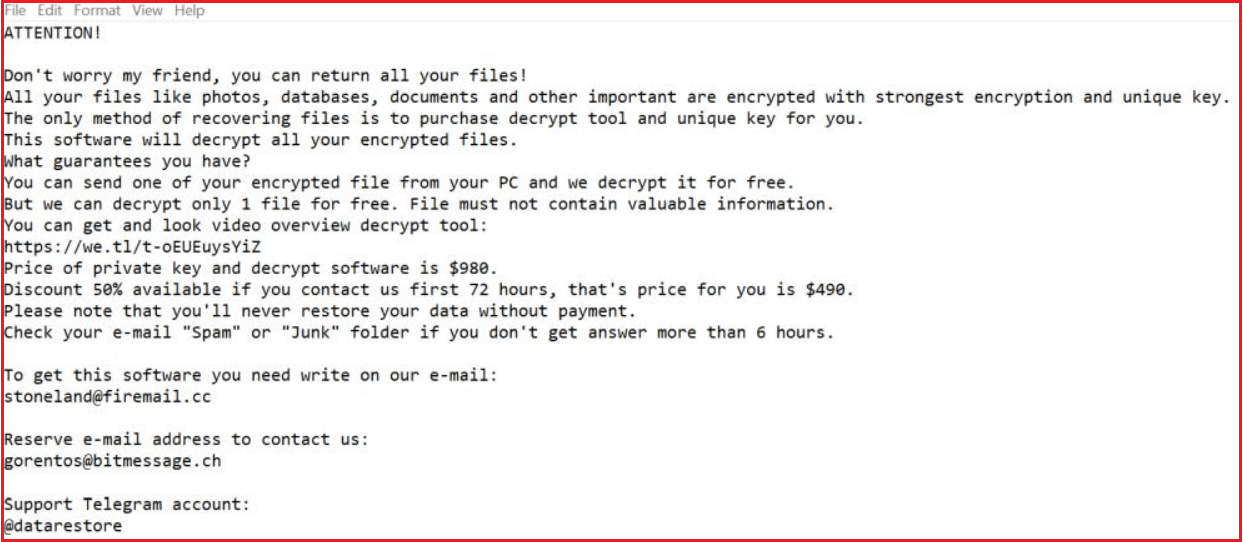
This malicious program is able to seal all private files that the victim has stored on their Computer – this is typical for viruses of the Ransomware cryptovirus category. When all the targeted data has been sealed by the malicious encryption, a ransom-requesting notification appears on the victim’s screen, informing them about the infection. The notification also contains details with regards to how the ransom is to be sent to the criminals, who control the virus. This basically is an incredibly shady blackmailing scheme, in which a ransom is demanded from the user in return for a secret decryption key, which could unseal the encoded data. If the the malware victim refuses to make the money transfer, there could, in many instances, be a threat that the files would remain encoded for good. Regardless of whether you’re a current victim of the malicious .Boston or just a user who’s eager to learn more about how Ransomware virus programs function and also the way one can potentially handle them, make sure you check out the next paragraphs as well.
After the encryption of the victim’s files .Boston virus would drop a ransomware note file called _readme.txt .
How Ransomware Works
Being well informed with regards to the way this sort of virus operates is required if you want to be able to deal with it on time. One important thing which sets apart Ransomware and most other sorts of viruses is the way Ransomware typically works. Whenever a Ransomware invades one’s computer system, it doesn’t start to cause harm to the PC and, instead, it first examines the HDD for certain predetermined computer file formats. What this type of virus threat might aim for are the following forms of private files: video, audio, images in addition to written docs and, in certain instances, even system data documents might get targeted.
After the ransomware virus has found everything, it’d then proceed to make a copy of each and every computer file, removing the original one after the copy has been created. What’s special with regards to the data copies made by the noxious program is that they are all secured by an advanced code. By using this elaborate procedure known as data encryption, the hacker that’s using the Ransomware could deny the targeted user access to the specified data files and afterwards require a money payment in order to unseal the encrypted personal data. Considering that the file encryption does not corrupt or harm anything on the pc system, the majority of antivirus tools often ignore it which is the reason nearly all Ransomware cryptovirus infections oftentimes manage to remain invisible for the duration of the encryption procedure.
Technically, it isn’t impossible to manually recognize the ongoing Ransomware contamination. However, this can only happen if you are constantly looking for certain particular warning signs like, for example, unusually high usage of ram and cpu time. Unfortunately, very few users manage to spot such an infection on time and prevent its consequences from taking place. This is why, in most instances, by the time one notices the infection, the files are already inaccessible due to the encryption applied to them by the Ransomware.
SUMMARY:
| Name | .Boston |
| Type | Ransomware |
| Detection Tool |
Remove .Boston Ransomware Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.




Leave a Comment