This page aims to help you remove Brightvar.bid. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
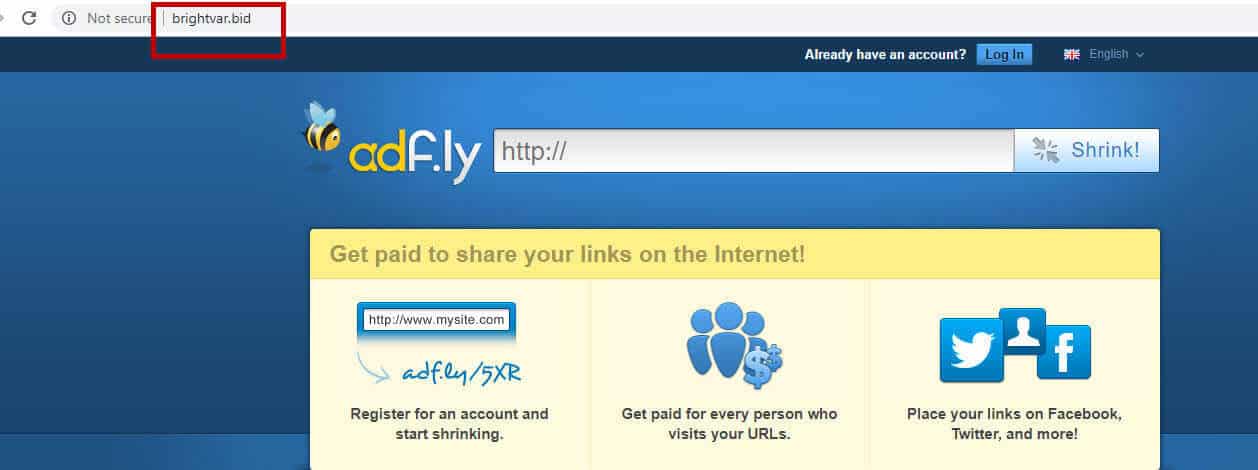
Have you recently been experiencing some automatic page-redirects to various unfamiliar websites? Or has your default browser started to flood your screen with hard-to-remove pop-ups, banners and ads? If yes, then stay with us to learn how to remove them. These above-described activities are usually caused by a very common type of software known as browser hijackers and, in the next lines, we will talk about this software class. In fact, we will describe the characteristics of one particular representative of the hijacker group called Brightvar.bid, which is the most probable source of the ads invasion on your screen. Though oftentimes seen as viruses, the real nature of the browser hijackers is not the same as that of actual malware threats. The security experts categorize hijackers as advertising tools for the online marketing industry which integrate with popular browsers such as Chrome, Mozilla Firefox, Explorer or others and use them to display hundreds of sponsored advertising materials on the people’s screens.
Apps like Brightvar.bid usually claim to provide the web users with some free functionality and to enhance the web surfing experience by generating relevant search results. They typically appear similar to other normal browse extensions but the way they operate might be very different. In most of the cases, instead of generating genuine and relevant search results, the browser hijackers tend to take over the default browser, install some sponsored search engine tools, homepage domains or toolbars and through them start to display some promotional websites, ads, pay-per-click links and sales pages much different than the ones that you actually want to visit. Due to this behavior, they are known as sources of browsing disturbance and many web users seek methods to have them uninstalled from the system. If you, too, can’t tolerate the presence of the hijacker on your system, we have prepared special instructions below, which will help you remove Brightvar.bid and get your browser settings back to normal.
Can a browser hijacker like Brightvar.bid threaten the safety of your system?
A significant number of web users refer to the browser hijacking applications as quite irritating. Having in mind the behavior that we described above, this is quite understandable. But many people also find pieces like Brightvar.bid questionable and fear that the hijacker might harm their system or infect them with other security threats such as Trojan horses, Ransomware, Spyware or similar malware. This is a rather exaggerated fear because the nature of the browser hijackers is more or less harmless. Yes, such software may gain control over your Chrome, Explorer or Firefox browsers, but this most probably would be the only thing on your PC which would be affected. Generally, the hijackers’ primary goal is to advertise and to generate traffic and clicks to the links they display. Their aggressive ads exposure is also oftentimes linked to popular remuneration models such as pay-per-click or sponsored ads positioning. That’s why, apps like Brightvar.bid typically are programmed to flood the screen with a never-ending stream of promotional content. Luckily, apart from that ads-related disturbances, it is really unlikely for the users to experience any serious system corruption, destruction or software damage. Real viruses such as Ransomware, Spyware or Trojans, however, will definitely cause significant issues to your system’s performance, your data and the processes in the OS. Oftentimes, they can’t be removed without leaving serious damage while the browser hijackers could be easily uninstalled without any negative consequences. You don’t even need to be an expert to deal with them because a detailed removal guide like the one on this page or a simple scan with a professional removal tool can help you deal with them.
How to prevent browser hijackers from entering your system in the future?
If you want to keep potentially unwanted applications away from your PC, then you should pay close attention to what software you install on your system. This is very important because, in most of the cases, apps like Brightvar.bid can be found in different software bundles, games setups, free app installers, browser add-on packages and could be installed alongside them if not specifically left out by the user. For that reason, we strongly advise our readers to first carefully select their software sources and also to always use the Advanced/Custom installation options instead of the Automatic/Quick ones when running a given setup.
SUMMARY:
| Name | Brightvar.bid |
| Type | Browser Hijacker |
| Detection Tool |
Brightvar.bid Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment