This page aims to help you remove Bubble Dock “Virus”. These Bubble Dock “Virus” removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
NOTE: The Bubble Dock “Virus” is not truly a virus. We called it as such in the beginning so people do not get confused until we can properly explain what it is. Bubble Dock is part of a group of software dubbed “adware.” A Bubble Dock “Virus” by itself means an illegitimate software that tries to scam you. Adware are technically legal and while they are NOT a virus, they may still prove a security risk, because of their ability – and inclination – to install other programs, many of which may be shadier.
The Bubble Dock “virus” comes in many colors and shapes. Although some people consider Adware applications like this relatively harmless the fact is that this assumption is not totally correct. It is true that this program will not cause any damage to your computer or steal information, but it should not be underestimated either. The Ads it creates can link to various malicious webpages and the software advertised can be a huge security risk.
Some people call the creators of these programs hackers, but that is not technically correct. Many of these so-called hackers work for big companies that make millions of dollars in yearly revenue. Adware applications are generally considered unwanted, but not illegal. There is usually some fine-printed text which the user usually fails to read, but that protects the application and its owner from lawsuits. Generally preventing your PC from becoming infected in the first place is easier than dealing with the consequences once that happens.
Bubble Dock is just another member of the pack
Bubble Dock acts similarly to other Adware applications. It likes to work ‘under cover’. For example, it really enjoys being camouflaged, i.e., hiding under the real/legit files. If you, per say, like to download files from websites that offer some software for free, you will most likely end up with a bundle of files. One of them, aka, the one you were looking for, will be OK, but the rest that install on your PC can become a real problem. The only way to get rid of them and the malware is to immediately uninstall ALL of them. We should mention that illegal or semi-legal distribution platforms like torrents and online storage sites carry a greater risk of infection. Sometimes it’s better to pay a couple bucks for a song or video, then to get random infected files that could and probably will damage your computer.
Other tricks employed by Adware
You may have heard of what is called a phishing e-mail. These are pretty dangerous as they can steal your online credentials and accounts, emptying your bank account in the process or stealing your identity. Fortunately this is not what Bubble Dock does, but its similar in execution. What does such an e-mail look like? Well it basically contains an executable file to download&install or a malicious link to click on. Not all such emails contain google-translated gibberish. Some are very well written and can be indistinguishable from a day-to-day work related email. WE urge our readers caution when they check their mailbox – never open files sent by strangers without scanning them for viruses first.
E-mail attachments are the regular and usual way for Bubble Dock to spread. Even if the letter has been sent to you by your most trust worthy and loyal friend, don’t be 100% naive, and secure yourself by scanning the attachment and making sure there is no surprise coming along with it. Once you’ve verified that it’s all clear, you may do whatever you wish with it: simply open it or save it.
When Bubble Dock comes to your computer it will not remain silent forever. Eventually it will start expressing its presence in many ways. One popular way is through browser redirects — you are using Chrome and suddenly Firefox windows begin to open and you can’t seem to be able to close them. Another way is through random tab opening in your current window. Those tabs will lead you to crazy websites that will clearly show you that something is definitely wrong with your computer. BUT not in all cases! Sometimes the webpages maybe just as fine, but watch out for excessive pop-up ads, such as: banners, flashing boxes, etc. The regular and easier to be recognized symptoms include: slowness of performance, glitches, bugs, frozen screen, hardship in navigating and controlling settings, and all computer activity in general.
These are all scary things, we know. Thus, we have put the removal guide to help you.
SUMMARY:
| Name | Bubble Dock |
| Type | Adware |
| Detection Tool | Malware and Adware are notoriously difficult to track down. Download SpyHunter – a professional parasite scanner – to make sure you find all files related to the infection. |
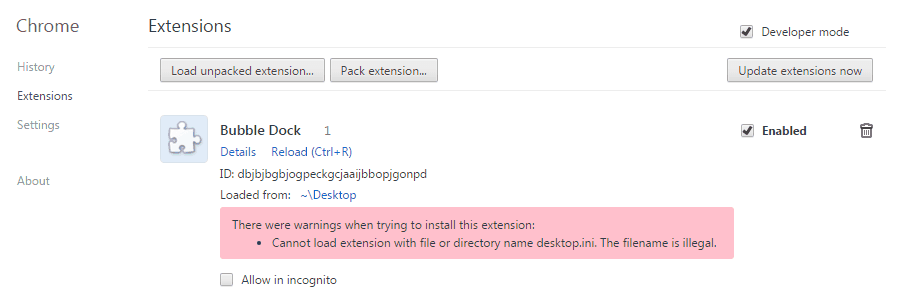
Bubble Dock Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment