C4H
C4H is a ransomware program that prevents users from accessing digital files on their computer and asks them to pay a ransom. To block access, C4H applies encryption to the targeted files, thus, it is considered a cryptovirus.
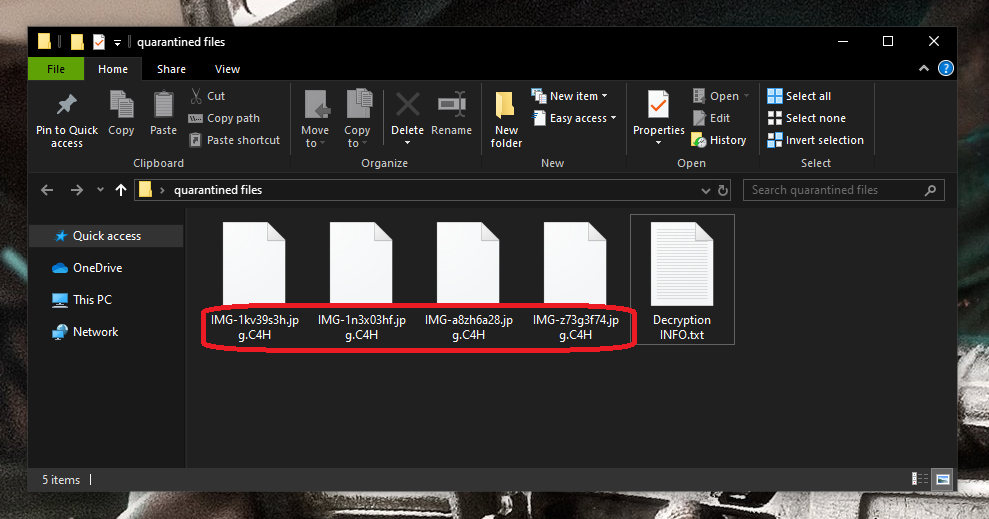
The C4H Ransomware will encrypt your files and leave a .txt file when it is done.
Ransomware threats are very common extortion tools, used to quickly raise money through blackmail for cybercriminals. These threats are often very successful in remaining undetected by the computer’s security software while applying their complex encryption to the files of the victim. Usually, they do not display clear signs of their activities and do not trigger a response from most antivirus programs.
C4H is specifically designed to target digital data and to lock it with the help of a complex encryption code that cannot be reversed without a decryption key. This infection demands money from its victims to undo what has been done to the files. The hackers that stand behind this infection typically place a .txt file on the screen which serves as a ransom note and explains how to send the money to their cryptocurrency account. In exchange for the payment, they promise to provide the victims with a corresponding decryption key that can reverse the encryption that C4H has applied.
But trusting the promises of the same people who are responsible for hacking your machine and encrypting your own data isn’t the best thing you can do. After all, C4H’s hackers do not worry about whether you can retrieve your files or not. The only thing they are after is your money, and when you send it to them, it is very likely that they disappear without sending you a decryption key or whatever file-recovery solution.
The C4H Ransomware
The C4H virus is a ransomware-based infection that scans infected computers for specific digital files and encrypts them with a complex algorithm. The ultimate goal of the C4H virus is to restrict the owners’ access to them and to demand a ransom for a file decryption key.
Users who keep really important files on their computers are the ones that are most affected by the attack of C4H. They may lose access to the encrypted information and may never be able to get it back even if they fulfill all the ransom demands or remove the ransomware from the system. This is because once the complex encryption code is applied, there is no guarantee that it can be reversed successfully. Even the decryption key that the hackers promise to send may fail to do that. Not to mention that the crooks may never send such a key to the victims.
Those who keep backup copies of their information on external drives, cloud storage or another device, however, can easily recover from the ransomware’s attack. They only have to remove the infection from the computer in order to safely connect their backup sources and copy their files back. The problem arises when there is no backup and the encrypted files are very important. In this scenario, victims are advised to consider all the available options to better deal with the ransomware. Fortunately, such options exist and, in the removal guide below, you can find a section with some of the possible file-recovery suggestions.
The C4H file decryption
The C4H file decryption is a method of file recovery, which makes the files encrypted by C4H accessible again. The C4H file decryption requires a specific decryption key that is available only in exchange for a ransom payment.
If you don’t want to pay ransom to cyber criminals, we recommend that you first investigate our guide on how to remove the virus and explore our free methods for file recovery. If nothing works, you may also want to explore other alternative methods online or even contact a specialist rather than giving your money to anonymous hackers.
SUMMARY:
| Name | C4H |
| Type | Ransomware |
| Detection Tool |
C4H Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Hi dear friend
My system has received C4H ransomware, the information of which is very important to me, to the extent that there is a possibility of being fired from the company, if you can help me in this regard to solve the problem and recover my information, also from I am not in a good financial position and I am paying for two families,
Hi reza,I’m sorry but your files are still undecryptable. For now, the only other alternative to paying the ransom and best thing to do is back those files up onto another drive for safe keeping until a decrypter becomes available.