Calevent
Calevent is known for hijacking the browsers installed on Apple iPhones and other iOS devices. Therefore, Calevent falls into the software category of so-called browser hijackers.
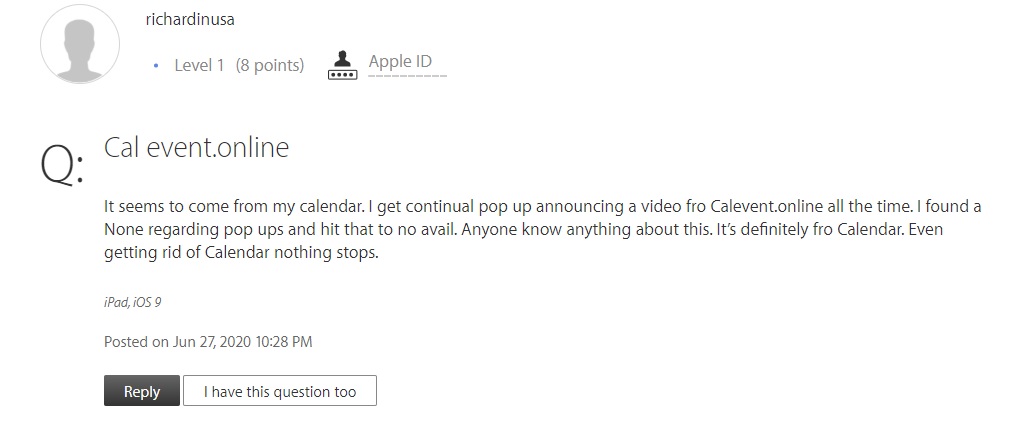
An iPhone user complaining about the Calevent Calendar Virus
This application has the capacity to integrate with your Chrome, Safari or other web browser. And as a result, it begins to impose its own settings and cause the browser to behave in certain ways. These types of programs are generally designed to earn revenue for their developers by means of displaying paid ads like popups and banners. And as other methods of promoting various products and services that they can profit from, programs like Calevent, Msgstars may also start triggering page redirects in your browser and even change its default search engine and/or homepage.
Calevent.online
That goes to say that Calevent.online is merely considered a potentially unwanted program or PUP, though. Hence, it is not a virus and cannot harm your iPhone, iPad or iPod. But it can quite plausibly expose you to various unsafe web locations as a result of its aggressive online advertising practices. And that, in turn, has the danger of leading to infections with Trojan horse viruses, ransomware and other malware.
In order to protect yourself and your system from such things, we highly recommend refraining from tapping on any of the ads that come your way. There’s no telling where they may lead and it’s simply not worth the risk of compromising your device. Instead, the optimal course of action is to remove Calevent entirely. And we can help you with that in the removal guide you’ll find below.
SUMMARY:
| Name | Calevent |
| Type | Adware |
Remove Calevent Calendar Virus
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and clean up your phone’s calendar events if they are infected.
- Find browser extensions related to the threat and how to remove them.
- Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment