Captchatest.top
Captchatest.top is a browser hijacker that is notorious for the ads, banners, and pop-ups that it constantly displays in the default web browser. If Captchatest.top has been installed on your Chrome, Firefox, IE or another browser, you may notice a new search engine or a different homepage in the place of your default settings.

In general, programs such as Captchatest.top are commonly referred to as Potentially Unwanted Programs (PUPs). This is a term used for software that might often be misinterpreted as a virus, but in reality does not pose a direct danger to the system. Users whose browsers have been hijacked by Captchatest.top and Custom Search Bar are often bombarded with various pop-ups, banners, redirect links, and pop-under advertisements during their web browsing sessions.
CaptchaTest
Other than the ads invasion, most browser hijackers like CaptchaTest tend to change the default search engine and homepage to a sponsored one, often without the user’s awareness or direct consent. The changes performed to the browser by CaptchaTest are not in any way harmful to the operating system.
However, as a result of these modifications, the user’s computer may be exposed to a broad variety of other online threats such as virus-infected ads or malicious websites. So, if you care about your online safety, you should better uninstall this malware and remove its changes as soon as possible.
Captcha Test Top
Generally speaking, you should remove any hijacker like Captcha Test Top you discover on your computer as quickly as possible because it may not only constantly interrupt you with unexpected adverts, but also make your browser slow, unresponsive, or unstable to sudden crashes. In addition, such software may alter the browser’s settings in a way that it redirects you to websites that aren’t necessarily trustworthy. As a result, the easiest way to prevent being redirected to ads and websites you don’t want to visit is to remove Captcha Test Top from your computer.
The random pop-ups and advertising that appear on your screen may also not be the most trustworthy content that you can interact with. In some cases, such random pop-ups may redirect you to a phony site that may be employing “phishing” forms to steal personal information, or click-baits that directly distribute viruses, Trojans and Ransomware. With all that we said by now, you’ve probably realized how important it is to remove Captchatest.top and its components from your computer sooner than later. The good news is that you don’t have to search for instructions on that, as we have a detailed removal guide that explains all the steps.
Stay safe online
Browser hijackers are pieces of software that can often be found distributed in a bundle with other, more desirable software. They often are promoted as tools that can enhance your web browsing experience and are found under the “Custom/Advanced settings” options in an installation package. Unchecking the checkbox for these extra components is usually enough to prevent them from being installed.
Sometimes, some more aggressive sites may include such ad-generating components in pop-ups that, once clicked on, may function as permission buttons, and clicking on them may enable a browser hijacker to take over your browser and apply its settings.
That’s why it’s always a good idea to avoid browsing random websites and carefully install any new software using the most detailed settings available to protect your computer and personal information from programs like Captchatest.top, as well as viruses and malware, such as Trojans, Ransomware, and Spyware. Keep in mind that many sophisticated threats can only be detected by a professional anti-virus application, so don’t skimp on this software.
SUMMARY:
| Name | Captchatest.top |
| Type | Adware/Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Captchatest.top Virus
If you don’t have time to go through the whole Captchatest.top removal guide, here are some brief instructions for getting rid of the browser hijacker quickly:
Click on the menu button in the upper-right corner of your hijacked browser.
A drop-down menu will display a list of available options. Select More tools/add-ons from the drop-down menu.
In order to access browser add-ons and extensions, locate the Extensions tab in the browser’s menu bar next. Look for Captchatest.top in the list, as well as any other potentially undesirable browser extensions that could be there. The Captchatest.top-related ad-generating extensions may be uninstalled by selecting them and clicking the “remove” button next to them.
After that, open a new browser window and see whether the overall browsing experience has improved after you’ve removed the potentially unwanted extensions from your browser.
After resolving the issue with Captchatest.top, you may return to using your browser as you normally would. If, despite completing these quick instructions, you continue to experience bothersome adverts and redirection to random pages, the detailed steps below will help you remove any hijacker-related browser alterations from your computer.

You may need to restart the compromised computer during some of the Captchatest.top-removal instructions below; therefore, please bookmark this page so that you can easily return to it. There is also the option to access the instructions by opening the guide on another device if that is more convenient for you.
Before you proceed, we recommend that you restart your computer in Safe Mode, you will have a greater chance to completely remove the browser hijacker when just the most essential applications and processes are operating in the background. Instructions on how to restart your computer in Safe Mode may be found by clicking on this link.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
With a few mouse clicks, you can easily see what is going on in the background of your computer. Open the Windows Task Manager by entering “task manager” in the Windows search bar and clicking Enter. This will bring up a list of all currently running processes. Check the Processes tab for processes with strange names or excessive CPU/RAM consumption, and end them if necessary.
By right-clicking on each questionable process, you can access the context menu and choose Open File Location from it.

Check these files by running a scan on them. You may scan your files for free using the scanner that is provided below.

Remove any scanned files that have been flagged as dangerous by your scanner. You may need to end the process that is reliant on these files in order to do this. End the process by selecting “End Process” from the shortcut menu that appears when you right-click on the process in Task Manager. After that, go back to the original place and delete the files that have been flagged as potentially hazardous or harmful.

The third step is doing a manual search of your computer for any potentially unwanted applications. Hold down the Windows key on your keyboard while simultaneously pressing and holding down the R key. Then, in the Run box that appears, enter appwiz.cpl and press the OK button.

In the Control Panel window, you may view a list of all the programs that have been installed. Sort the results by the date they were installed if you want to view the most current applications. To uninstall any software that you believe is associated with the browser hijacker, select it and click Uninstall.
Next, you need to check if Captchatest.top has added some startup entries in the system. To do that, you need to open System Configuration by typing msconfig in the Windows search bar and pressing the Enter key. Using the Startup tab in System Configuration, look for and deactivate any Captchatest.top-related startup items that may be present. In order to deactivate a startup item, all you have to do is uncheck the checkbox next to it and click OK.



Following that, look for DNS changes in your system’s setup. This may be accomplished by typing “Network Connections” into the Windows search bar and pressing Enter.
With your pointer, select the network adapter that you are now using. Right-clicking on it and selecting Properties from the fast menu will open its properties window for you to review.
When you choose Internet Protocol Version 4 (ICP/IP), you’ll see a new Properties button at the bottom right of the new window. Simply click on it.
Choose Obtain DNS server address automatically and then click on the Advanced options button to complete your configuration.
In the new window that opens, choose the DNS tab and delete any DNS entries that are rogue. Once you’ve completed this step, click OK to ensure that the modifications you’ve made are saved.
After you are done with the DNS settings, close the window, and hold down the Windows key and the R key at the same time, launch a new Run window. Type the line below in it and hit the OK button:
notepad %windir%/system32/Drivers/etc/hosts
You should be able to open a new file named Hosts in your Notepad at this point. Once you’re in there, look for suspicious IP addresses that are added below “localhost“.
If you come across any suspicious addresses, copy and paste the addresses from the file in the comments area below this guide so that we can take a look at them and tell you whether or not they pose any danger to you.


You’ll need to search through the registry for anything connected to potentially unwanted software if you want to get rid of the browser hijacker. If these registry entries are not deleted, the potentially unwanted software may be able to reinstall itself. That’s why, if you want to be effective in removing Captchatest.top, you must follow all the actions described below.
Type regedit in the Windows search bar and hit Enter to launch the Registry Editor program.
Next, open a Find window in the Registry Editor, by pressing F while holding down the CTRL key on your keyboard. Search for hijacker-related items by typing the hijacker’s name in the Find window and then pressing the Find Next button. This will assist you in rapidly locating any hijacker entries that have the same name as the hijacker that you want to delete from your computer. Remove the identified result by right-clicking on it and selecting “Delete” from the short menu that appears.
If the Find box does not return any results, you may manually search the Editor’s left panel by heading to each of the three locations listed below:
- HKEY_CURRENT_USER—-Software—–Random Directory.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If you delete anything else from your computer that is not linked to the browser hijacker, you risk causing registry issues that may have a damaging effect on your computer’s operating system and applications. For this reason, while dealing with the register, you should proceed with great care. An anti-virus tool, such as the one available on this website, can make it straightforward to delete hazardous or potentially unwanted software from your computer’s registry, without putting your computer at risk.

In most cases, users prioritize removing the hijacker from their main web browser above screening all of their other browsers for the hijacker. However, this does not remove the hijacker from other browsers, which means that the problem is not totally resolved. As a result, in the sixth step, we’ve given instructions on how to uninstall the hijacker from three of the most common web browsers on the market today.
Right-click with your mouse on the shortcut icon for your browser and choose Properties from the pop-up menu that appears.

The Target section may be found under the Shortcut tab of the Properties window. Please ensure that nothing is added after .exe (as seen in the picture) and that you save your settings by clicking OK after making your changes.

![]() Remove Captchatest.top from Internet Explorer:
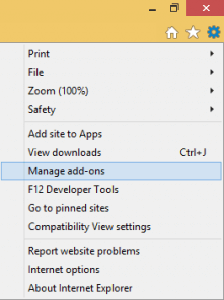
Remove Captchatest.top from Internet Explorer:
If you are using Internet Explorer, the main menu may be reached by selecting the gear icon in the top right corner of the browser. Then, from the drop-down menu, select Manage add-ons and have a look at the add-ons that are listed there. If you discover an add-on that you believe is causing you hijacker-related troubles, uninstall it from your browser immediately!
Next, select “Internet Options” from the drop-down menu by clicking on the gear symbol once again. In general, it’s a good idea to delete any sponsored links from your homepage and replace them with a URL that you are comfortable with. After you’ve done making your changes, click the Apply button to have them saved to your computer.
![]() Remove Captchatest.top from Firefox:
Remove Captchatest.top from Firefox:
The Extensions tab in Firefox may be accessed by selecting it from the three-line menu button located at the upper right of the browser’s window. Select Add-ons >>>Extensions from the menu bar, and then click the Remove button next to any Captchatest.top-related browser extensions you no longer want to keep. Some extensions may require that they first be disabled before they can be deleted.

![]() Remove Captchatest.top from Chrome:
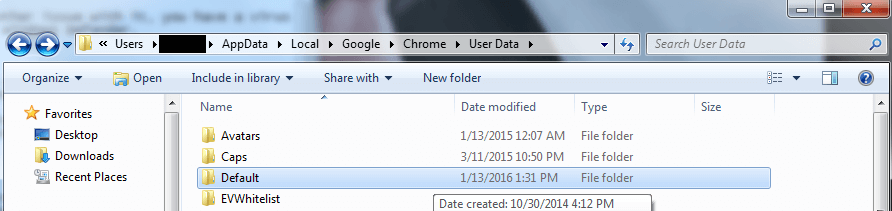
Remove Captchatest.top from Chrome:
Before proceeding, it is required to quit Chrome and manually navigate to the following location on your computer
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data.
The default folder should be renamed to “Backup Default” by right-clicking on the Default folder and choosing Rename from the context menu.
If you don’t have the time or patience to manually remove the browser hijacker, we suggest that you use the removal program that we have recommended on our site instead. Additionally, check to see if any suspicious files have been left behind by using our free online virus scanner. In the event that you have any queries, you may leave them in the following comments area. We’ll get back to you as soon as we can.

Leave a Reply