Cationoppo
Cationoppo is an unwanted iPhone application that changes the behavior of the Chrome or Safari browser and causes sudden page redirects for the user. Cationoppo is also known for obtaining extensive permissions without the user’s knowledge and for displaying obstructive advertisements.
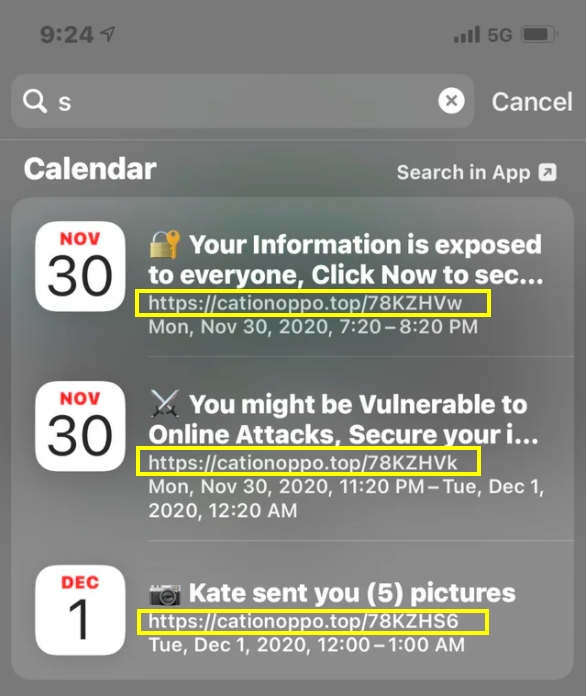
The Cationoppo Virus will display fake pop up messages.
This app is one of the many so-called browser hijackers. A browser hijacker is basically a software tool used for site and product promotion. Its main job is to provide exposure to the content it is programmed to advertise by forcing the browser to display various ads (e.g. popups, banners) and to open certain sites without the user’s permission.
While these apps aren’t viruses and cannot be compared to Trojans or Ransomware in terms of how problematic they are, it is still worth noting that a hijacker app is not supposed to be on your device. Changes in the search engine and the homepage address of the browser are also likely to occur if there is a hijacker present on your iPhone, which is yet another example of the intrusive nature of these unwanted apps.
Intrusiveness aside, however, the real problem related to applications like Cationoppo is that they do not always promote the safest of contents. Oftentimes, users get their Safari browsers sent to unreliable and questionable sites that have a low reputation. This could, in some cases, lead to different security issues, including the exposure of the device to malware. The advisable course of action when faced with a representative of the browser hijacker category is to quickly remove the invasive app. If you need any help with the removal of Cationoppo, be sure to try out the following instructional guide.
SUMMARY:
| Name | Cationoppo |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | iPhone hijackers cause unwanted browser page redirects and generate obstructive banners on the device’s screen. |
| Distribution Method | Mainly distributed as an added element to another application. |
Cationoppo Removal
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and clean up your phone’s calendar events if they are infected.
2. Find browser extensions related to the threat and how to remove them.
3. Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment