*Cdcc is a variant of Stop/DJVU. Source of claim SH can remove it.
Cdcc File
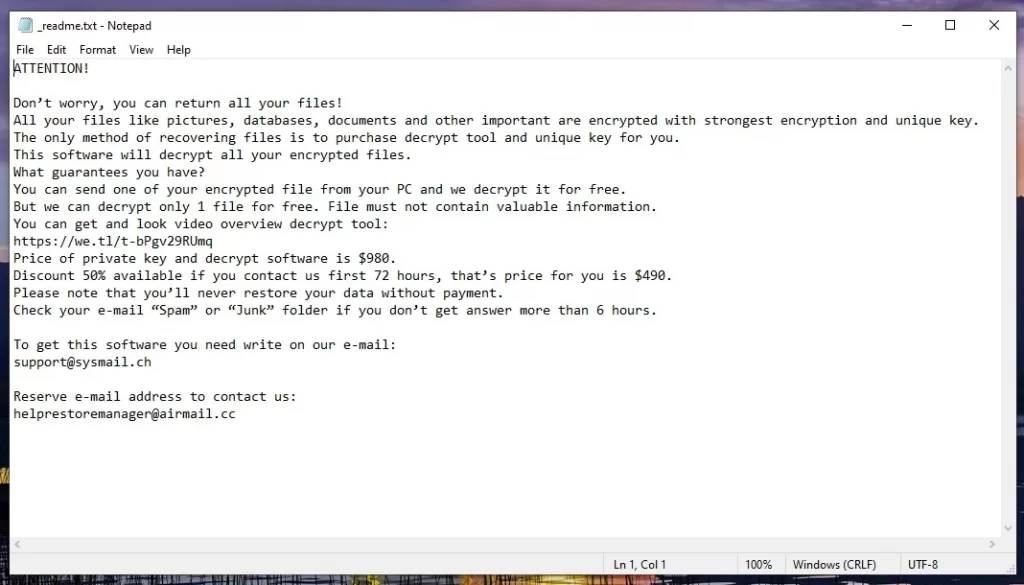
If you have stumbled upon a Cdcc file on your computer that doesn’t want to open, this could mean that trouble is knocking at your digital door – you might have fallen victim to a ransomware attack. The initial observable indications of a ransomware infection typically manifest as anomalies in your computer system’s behavior and file accessibility. Certain files, such as the Cdcc file, may appear to be encrypted or inaccessible, and when you try to open them, a ransom note may appear on the screen that demands payment in exchange for data decryption. If this is your case, it’s important to remain vigilant for any unexpected changes and to address them promptly to mitigate the potential impact of a ransomware attack.
Decrypting Cdcc ransomware files typically requires obtaining the decryption key from the ransomware operators, which often involves paying a ransom, though this is not recommended due to the risks involved. Alternatively, some cybersecurity experts and organizations may develop decryption tools that can unlock certain ransomware strains, including Cdcc, without paying the ransom. It’s crucial to first isolate and remove the ransomware from your system using reputable security software before attempting any decryption process. If a decryption tool is available, carefully follow the provided instructions. Prioritizing preventive measures such as regular data backups, maintaining up-to-date security software, and practicing safe online habits remain essential to safeguarding against ransomware attacks in the first place.
To remove the Cdcc ransomware virus and restore the compromised files, isolate the infected system from the Internet to prevent further damage. Next, use reputable antivirus or antimalware software to scan and remove the ransomware from your computer. Once the ransomware is eliminated, explore available options for file restoration. If you have recent backups, restore your files from a clean backup copy. Alternatively, check online resources and security organizations for potential decryption tools specifically designed for the Cdcc ransomware variant. Remember that paying the ransom is discouraged due to its risks and uncertain outcomes.
Cdcc Virus
The Cdcc virus can infiltrate a system through various means, with the most common sources being malicious email attachments, deceptive links in phishing emails, compromised websites, and malicious downloads from untrusted sources. Cybercriminals often craft convincing emails or messages that entice users to open attachments or click on links, thereby initiating the ransomware download. Additionally, exploit kits on compromised websites can take advantage of software vulnerabilities to deliver the ransomware payload. Users who download cracked software or pirated content from unofficial sources also expose themselves to the risk of ransomware infection. Vigilance against suspicious emails, cautious web browsing habits, and avoiding unauthorized software downloads are crucial defenses to thwart the entry of the Cdcc virus and other similar threats like Cdxx or Cdpo.
Cdcc
Keeping your system safe from Cdcc requires a multi-pronged approach. Our recommendation is to maintain up-to-date security software that can detect and block potential threats. Also, you should regularly update your operating system, software, and applications to patch vulnerabilities that ransomware exploits. You should also not forget to implement robust email security by exercising caution with email attachments and links, and consider using strong spam filters. Your most effective protection against the Cdcc attack, however, is to backup critical data regularly to an offline or secure cloud storage that is disconnected from the network after backup. In this way, you can always have access to a copy of your data in case of an attack or hardware failure.
.Cdcc
Identifying the .Cdcc encryption, utilized by the Cdcc ransomware, can be a challenging task, since it is applied to your digital files without any specific visible symptoms. Once your files have been locked by the .Cdcc encryption, however, you will see a ransom message on your screen. Here, it’s important to realize that completing the ransom instructions is not a good solution. Even if you pay the cybercriminals, they may not send you a decryption key and may decide to ask for another ransom. For this reason, we recommend a proactive approach: explore other file recovery strategies, such as those outlined in the guide below, and make use of specialized removal tools or professional help to minimize the effects of the attack.
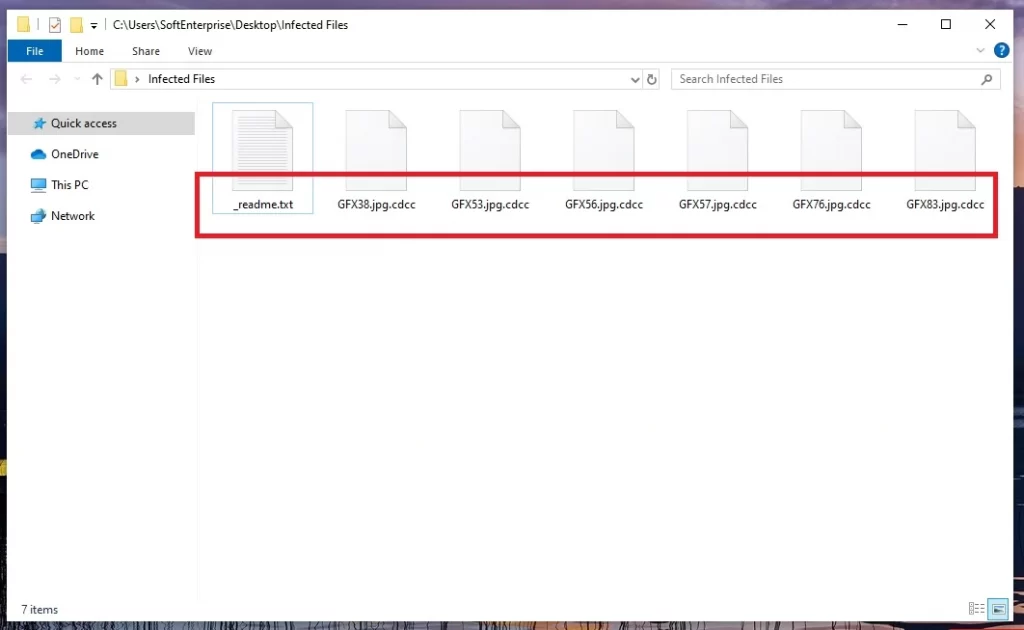
Cdcc Extension
The Cdcc extension is a specific suffix added by the ransomware to filenames as a way to indicate that specific files have been encrypted and are being held ransom. It’s a distinct identifier that helps both the victim and the ransomware operators recognize which files have been affected. Simply removing or reversing the Cdcc extension, however, will not automatically decrypt the files. Reversing the encryption process requires a decryption key, which is held by the ransomware operators. It’s important to note that attempting to reverse the extension on your own, or tampering with the encrypted files without proper decryption solution can result in permanent data loss. So, if you’re a victim, it’s advisable to seek guidance from cybersecurity professionals and reliable software rather than experimenting with the situation.
Cdcc Ransomware
The Cdcc ransomware infection stands out with its covert encryption of files that makes them impossible to access. This malicious software typically shows a ransom demand, usually in the form of a text document or an image on the desktop background and urges its victims to pay in cryptocurrency to acquire a decryption key. The Cdcc ransomware often employs robust encryption methods, complicating data recovery without the corresponding decryption key. It can also disable or limit access to system functions and network resources, causing disruptions to normal computer activities. The successful ransomware attack can be very harmful as it can result in data loss, financial harm, and potential exposure of sensitive data.
What is Cdcc File?
The Cdcc file is originally a regular system file that has become the victim of encryption through malicious software known as ransomware. It is stored on your system and is inaccessible unless the corresponding decryption key is provided. Practically, any digital file found on your hard drive can become an encrypted Cdcc file because the ransomware exhibits a wide-ranging encrypting capability, encompassing various file types such as documents, spreadsheets, images, videos, databases, and archives. Following encryption, these files often adopt a distinctive file extension, signifying their encryption, and are kept hostage by cybercriminals who demand a ransom in exchange for a decryption key.
SUMMARY:
| Name | Cdcc |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
*Cdcc is a variant of Stop/DJVU. Source of claim SH can remove it.
Cdcc Ransomware Removal

It is recommended that you bookmark this page by clicking on the bookmark button that is placed in the URL bar of your browser in order to get things started.
The next step is to restart your computer in Safe Mode, after which you should return to this website to finish the remaining Cdcc removal instructions.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Cdcc is a variant of Stop/DJVU. Source of claim SH can remove it.
In order to do considerable damage, ransomware threats like Cdcc often run in the background of a computer’s system, undetected. Therefore, one of the most challenging tasks when dealing with this type of malware is to be able to detect and end any potentially harmful processes related to the ransomware that are currently operating on your computer. To do that, you must carefully adhere to the next instructions.
By using CTRL+SHIFT+ESC, open the Windows Task Manager and select the Processes Tab from the top-level tabs pane. You should make a note of any processes that consume a significant amount of resources, have an unusual name, or otherwise look suspicious and right-click on each of them to access the quick menu. Then, select “Open File Location” to view the files of that process.

Next, scan for potentially dangerous code in the process’s files by running them through the free online virus scanner below:

If any of the files that you scan turn out to be dangerous, it is important that you stop the process that is linked with them as soon as possible and then delete those files from your computer.
Continue in the same manner for each process that includes potentially hazardous files until the system has been cleared of all threats altogether.

If the ransomware has added potentially harmful startup items to the system, these items must also be disabled, just as the Cdcc-related processes in Task Manager.
To accomplish this, type msconfig in the Windows search field and select System Configuration from the results. After that, take a look at the following entries under the Startup tab:

You should look into any startup item that has an “Unknown” Manufacturer or a random name, and tick it off if you discover enough proof that it is associated with the ransomware. Also, look for any other startup items on your computer that you can’t associate with one or more legal programs on your computer. Only startup items associated with apps that you trust or that are tied to your system should be left operating.

*Cdcc is a variant of Stop/DJVU. Source of claim SH can remove it.
It is necessary to search the system’s registry in order to determine whether or not the ransomware has left any malicious entries there. To get to the Registry Editor, type Regedit in the Windows search field and press Enter to open up the program. To locate the ransomware infection more quickly, hold down the CTRL and F keys on the keyboard, then type its name in the Find box. After that, click on Find Next and carefully remove any entries that match the name you just typed in.
To prevent causing more harm than good to your system, avoid deleting anything that you aren’t sure you want to be gone. Instead, use expert removal programs to completely delete Cdcc and other ransomware-related files from your registry, avoiding any unintentional damage to your system.
Next, manually search each of the places mentioned below for suspicious files and folders that appear to belong to Cdcc or to be associated with the threat. You can use the Windows Search bar to open the locations, one by one, and then press Enter to gain access to these locations:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Anything that looks to be a threat should be removed from these locations as soon as possible. Select and remove everything in the Temp folder in order to get rid of any temporary files that might be stored on your system.
The next thing to do after you clean the registry is to check your computer’s Hosts file for any changes that may have taken place without your knowledge. Start by clicking the Windows and R keys together to bring up the Run box, where you can type in the following command and hit the Enter key:
notepad %windir%/system32/Drivers/etc/hosts
Please notify us if the Hosts file has been updated to include certain suspicious-looking IP addresses in the Localhost section, as seen in the image below. They will be checked by our team, and you will be informed if there is an impending danger.


How to Decrypt Cdcc files
Depending on the virus variant that has infected your computer, you may need to use a different solution to successfully decode the encrypted data. In order to figure out which Ransomware variant you are dealing with, you must check the file extensions that the virus has attached to the encrypted files.
New Djvu Ransomware
STOP Djvu Ransomware is the most recent version of the Djvu Ransomware family to infect computers. It is easy for victims to identify the infection with this new malware since it uses the .Cdcc file extension, which is attached to the files encrypted by this threat. At this moment, only files that have been encrypted using an offline key are able to be decrypted with the available decryption solutions. You can access a decryption tool that may be of use to you by visiting the following link:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
To start the decryption application, download the file from the link above, choose “Run as Administrator” and then press the Yes button. If you have not already done so, please read the licensing agreement as well as the brief instructions that show on the screen before proceeding.
To begin the process of decrypting your encrypted data, click on the Decrypt button in the app. When using this tool, keep in mind that data encrypted with unknown offline keys or online encryption may not be decrypted. Additionally, if you have any questions or concerns, please share them in the comments section below.
Important! Please remove any ransomware-related files and potentially harmful registry entries from your infected computer before attempting to decrypt any files stored on it. A free online virus scanner and an anti-virus software such as that available on our page will help you get rid of Cdcc and other viruses that are spreading over the internet.

Leave a Comment