*Cdqw is a variant of Stop/DJVU. Source of claim SH can remove it.
Cdqw File
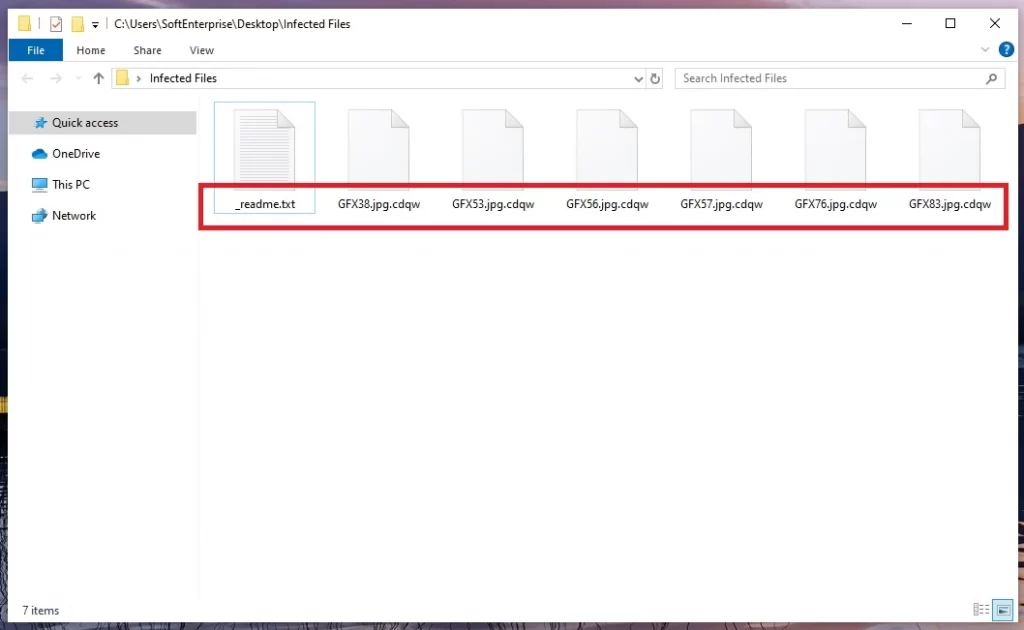
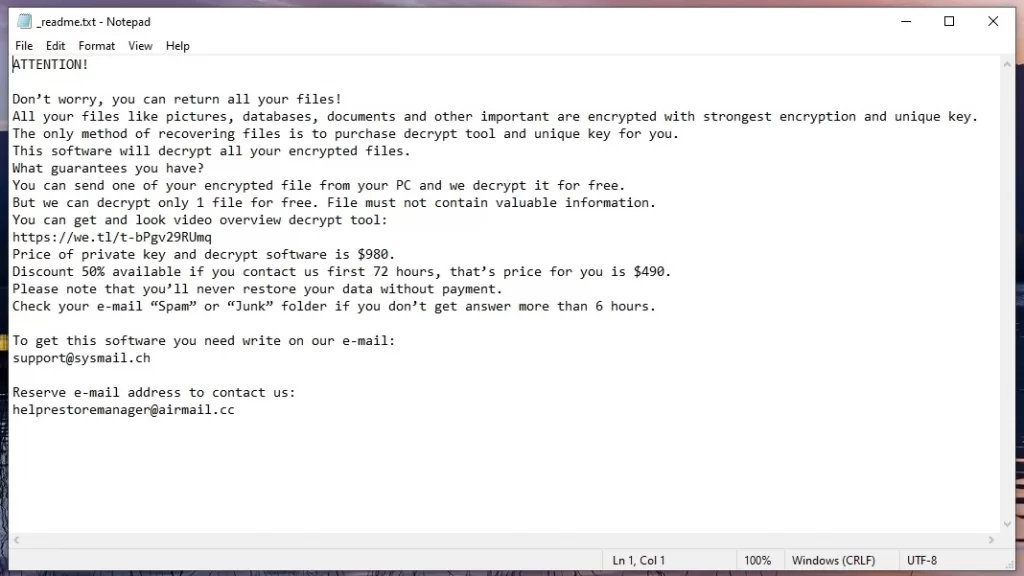
If you find yourself reading this due to a blockade on your data caused by Cdqw file encryption, it is crucial to read the details that follow attentively. Regrettably, you have been attacked by a ransomware cryptovirus, a dangerous money-extortion malware operated by cyber criminals. The visible sign of this infection, the Cdqw file encryption, serves as a tool used by the ransomware to selectively block your access to critical data stored on your systems. The encryption transforms your data into an undecipherable format using a complex cryptographic cipher. The attackers then present a fix: a decryption key that has the ability to undo the encryption and restore your data to its initial state. This “fix”, however, comes at a cost, known as a ransom.
To decrypt Cdqw ransomware files, the first thing is to disconnect your infected computer from the internet right away. Then, figure out which specific version of ransomware you’re up against – this will help you figure out potential solutions to unlock your files. Look to reliable online cybersecurity resources to give you guidance and methods to retrieve your captured files. And when you find a recovery method that fits your ransomware type, stick to the instructions as, the closer you follow them, the better the outcome.
How to remove Cdqw ransomware virus and restore the files?
To remove Cdqw ransomware virus and restore the files, there is no need to panic. Start by pulling the plug on your internet connection. Next, use a powerful antivirus software and run a full system scan to find and remove the malware. Once you’ve got the system all-clear, you can begin the mission to retrieve your encrypted files. If you have backup files, you’re in luck and can copy them to the ransomware-free computer. If you don’t have backups, however, don’t lose hope. Reach out to seasoned data recovery specialists or try your hand at reputable recovery software. They’re your allies in this rescue operation.
Cdqw Virus
The Cdqw virus is the latest addition to the notorious ransomware family, a group of malware known for taking your digital files captive and blocking access to them. Such malware can creep into your system through several means – it could be spam emails that seem harmless, tempting advertisements that draw you in, or even backdoor viruses that pave the way. Tackling the Cdqw virus can be a challenge, and the fallout from its attacks is often permanent. This is because the ransomware employs cutting-edge file encryption methods that leave your files in an unreadable state, with no existing software being able to decipher them without the right decryption key. The criminals behind the ransomware demand a steep ransom in return for the decryption key.
Cdqw
You know how the online world keeps on evolving, right? And with that, ransomware threats are getting slicker. The one that’s making headlines right now is Cdqw, a real nightmare for anyone who’s had the misfortune of encountering it. This illegal piece of software uses a super-advanced encryption method to block you from accessing your own files. Oh, and Cdqw has its favorites – documents, videos, and images, since these are typical of high value to the victims. Once the malware has applied its encryption to all of them, it slaps you with a ransom-demanding note that reveals the consequences of the attack and the exact ransom amount that you need to pay to regain access.
.Cdqw
Normally, the path to the .Cdqw decryption requires a special key – held, of course, by the hackers who operate the ransomware. But don’t lose hope just yet, there are other ways you can explore to retrieve some of your .Cdqw data without depending on the decryption key. Opting not to pay the ransom doesn’t just keep your wallet safe, it also discourages these digital crooks from their nasty business. Let’s face it, the less they earn from this, the less appealing their dirty job becomes. And let’s not forget, their goal isn’t to help you; it’s to get their hands on your money. So, paying the ransom doesn’t necessarily guarantee you’ll get the key in return. Think it through before you take that gamble!
Cdqw Extension
Let’s be honest, if you’re faced with the daunting task of dealing with the Cdqw, Lomx or Loqw extensions on your files, there are not so many solutions that you can try. Aside from the decryption key owned by the hackers that you can use to decipher the encryption, there are only a few alternatives and none can promise you a full recovery. The criminals count on this uncertainty to scare you into paying up. They’re not shy about threatening you with the permanent loss of your data and setting tight deadlines to rush you into paying up. But if you’re not ready to give in, a reliable removal guide and a top-notch antivirus software can be your best weapons to combat the Cdqw extension safely.
Cdqw Ransomware
The Cdqw ransomware could strike just about anyone. Doesn’t matter if you’re Joe from down the street or a big multinational corporation. And the statistics are rather grim – the average Joe and Jane who innocently surf the web are no less enticing to these cybercriminals. So, let’s bust this myth that they only go after the big leagues, shall we? Truth be told, if you’re tech-connected, you’re a target. Once you’re hit, you’re in for a tough call – do you part with a hefty chunk of money to retrieve your data, or do you go down the road of alternative file-recovery solutions? Before you panic, check out our handy Cdqw ransomware removal guide right here on this page for a first step toward resolution.
What is Cdqw File?
If you find yourself unable to access important files on your computer, labeled as Cdqw files, it is likely that you have fallen victim to the Cdqw ransomware. These files, whether they are family videos or crucial work documents, appear intact but are rendered useless due to encryption. Regardless of the file type, the ransomware encrypts and locks them away, making them inaccessible. The only solution to regain control over your Cdqw files is to obtain the correct decryption key. This unique key is the key to unlocking the encryption and restoring your files to their original, usable state.
SUMMARY:
| Name | Cdqw |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
*Cdqw is a variant of Stop/DJVU. Source of claim SH can remove it.
Cdqw Ransomware Removal

It’s a good idea to restart your computer in Safe Mode by following the instructions in the link before attempting to remove Cdqw.
Prior to restarting the system, though, make sure you’ve bookmarked this page by clicking on the bookmark icon in your browser’s address bar. In this way, you don’t have to keep looking for the removal instructions every time your computer or browser restarts, and you can immediately access the removal guide.
The remaining Cdqw removal actions listed on this page can be completed safely once your computer has been properly rebooted in Safe Mode.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Cdqw is a variant of Stop/DJVU. Source of claim SH can remove it.
Most ransomware viruses, such as the Cdqw, operate invisibly in the background of a computer’s operating system, making detection nearly impossible. Because of this, they are able to wreak havoc on the system while remaining unnoticed.
If you’re dealing with ransomware on your computer, one of the most difficult chores is to identify and terminate any potentially harmful processes that may be operating on your computer. To successfully detect and stop potentially harmful processes, it is imperative that the following instructions be followed as described:
Using CTRL+SHIFT+ESC key combination, open the Windows Task Manager, and then choose the Processes tab from the top menu.
Right-click on any processes that are consuming a lot of CPU and memory resources, have an odd name, or seem suspicious, and then use the fast menu to check the files linked with the selected process by clicking on “Open File Location“.

Use the free online virus scanning tool below to ensure that the files associated with the process in question are clean of any potentially harmful code.

As soon as a potentially harmful file is identified, the process associated with it should be ended and the files themselves should be properly erased from your computer.
If a process contains potentially harmful files, to end it, you need to use the right-click menu (right-click on the process) and select End Process.

The next step is to disable any harmful startup items that might have been added to the system as a result of the ransomware attack.
Using the Windows search bar, type in msconfig, and open System Configuration from the results. After that, browse through the Startup tab and see if there are any suspicious Startup entries:

You should investigate online any startup item that comes from an “Unknown” manufacturer or has a weird name, and uncheck the checkbox next to it if you find enough evidence that it belongs to the ransomware. Also, consider looking for any other startup items that you are unable to identify with the programs that launch when your machine starts up. Make sure you don’t disable the start-up items associated with programs that you trust or that are connected to the system.

*Cdqw is a variant of Stop/DJVU. Source of claim SH can remove it.
If you want to thoroughly remove all traces of Cdqw from your system and prevent the ransomware from reappearing or leaving dangerous components behind, searching the system’s registry for malicious entries is an incredibly critical step.
The Registry Editor may quickly be accessed by typing regedit in the Windows search field and pressing Enter. When the Registry Editor window open, use the CTRL and F key combination to search for the ransomware by carefully typing the virus’s name in the Find box. Remove any entries that include the ransomware’s name from the list by right-clicking and carefully deleting them.
Attention! Delete just the ransomware-related entries from your registry. If you delete anything else, you may risk damaging your system and the applications you’ve already installed on it. To safely remove all traces of Cdqw and other ransomware from your computer’s registry, please use professional removal software like the one linked on this page.
When no more results are found, exit the Registry Editor and manually search each of the locations listed below. To open them, type each one in the Windows search field and press Enter:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Once you’ve opened each location, search for and remove any hazardous files or folders that may be connected to the infection. For the sake of purging your system of any potentially dangerous temporary files, just empty the Temp folder by deleting everything stored there.
The next place to check for malicious modifications on your machine is the Hosts file. Keep an eye for any changes that could have been made without your knowledge, and let us know if you spot anything unusual in the comments section. We’ll investigate and get back to you with a reply.
If you want to go to the Hosts file, press down Windows and R keys together. A Run box will pop up, where you’ll need to paste the following command and hit Enter to for it to work:
notepad %windir%/system32/Drivers/etc/hosts
If your Hosts file has been altered to contain some suspicious-looking IP addresses under Localhost, as seen in the following example, please notify us:

If everything in your file appears to be in order, you may just close it without making any modifications.

How to Decrypt Cdqw files
In order to decrypt the encrypted data, victims need to first investigate alternative solutions depending on the variant of ransomware that has infected their machine. In order to detect which Ransomware variant you are dealing with, the first step is to look at the file extensions attached to the encrypted files.
New Djvu Ransomware
STOP Djvu Ransomware is the latest variant of the Djvu Ransomware family, which demands a ransom from the victims and targets machines all around the world.
To find out if you have been attacked with this variant, search for the .Cdqw file extension at the end of the files that have been encrypted by the virus. Files that have been encrypted by this malware usually have this extension automatically added to them. Even though this is a new threat and, typically, decrypting files of new threats can be quite challenging, if your flies have been encoded by using an offline key, there is a chance to decrypt them. A decryption tool may be found on the following page, which you can access by clicking on the link provided:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
First, you need to download the decryption application from the URL provided above, then click “Run as Administrator” on the downloaded file, and then select “Yes” to begin. If there are any short instructions or the licensing agreement on your screen, make sure you read them both before continuing.
To begin the process of decryption, you must click the Decrypt button. This will begin the process of decrypting the encrypted information. Keep in mind that this program may not be able to decode data encrypted using unknown offline keys or online encryption. Please let us know if you have any questions or concerns in the comments section below, and we will try our best to help.
Important! Check your computer for ransomware-related files and harmful registry entries before attempting to decode the encrypted data. The online virus scanner and the anti-virus software available on our site can help you remove Cdqw and other harmful malware that is circulating on the internet.

Leave a Comment