Cerber Ransomware
Ransomware is a very malicious tool that hackers use to lock and take hostage of the data on your PC. Cerber Ransomware is one such representative that uses a special file encryption algorithm to “secure” user’s data and make it unreadable, unless the demanded ransom is paid.
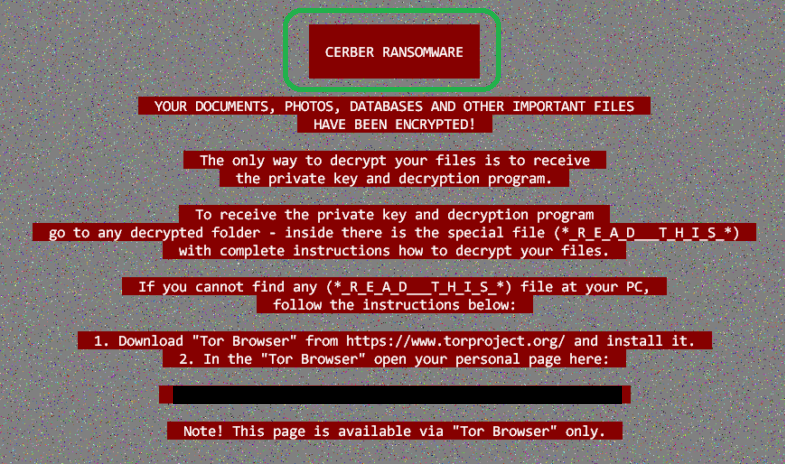
The Cerber Ransomware will display this message.
In case you are reading this, then you have probably become a victim of one very dangerous threat – Cerber Ransomware. This is indeed one of the nastiest viruses and it falls under the category of Ransomware. Our “How to remove” team will give its best to help you clean your computer from it. Below you will find a removal guide with proven steps that will help you identify the infection and manually delete it. Also, we will give you some suggestions on how to recover your data and most importantly, how to prevent Ransomware in the future. It is worth to spend a few minutes checking this information.
Ransomware – the data kidnapping tool.
In the past, kidnapping and taking hostage of important information has been a favorite tool for crooks to make money. Nowadays things have not changed much, except the fact that now everything has moved to the digital realm. And so has the old crooks’ scheme. Very often, the victims of this nasty ransomware are asked to pay from a couple of hundreds to a couple of thousands in exchange for the decryption key that is in the hands of the hackers. Therefore, it is understandable why people would like to try everything possible to find another solution to decrypt their files and save their money.
How can Cerber Ransomware infect you?
Ransomware infections happen through various ways that depend on the methods of distribution the hackers have chosen. Usually, their aim is to infect as many people as possible, that’s why they release massive email spam campaigns and spread the malicious payload as an attachment. Of course, the emails are masked like almost legitimate messages that ask from the unsuspecting victims to perform some action, usually, to open the malicious attachment in the email or click on a link. Once that action is performed, the virus is activated and immediately introduces the ransomware on the machine. This is commonly done through a Trojan horse, which creates system vulnerabilities and allows malware to get inside the computer. However, email isn’t the only way Cerber Ransomware distributes itself. It may also be found in pop-up messages, ads, torrents, and installations or infected websites.
What are the symptoms of the infection?
Victims of Cerber Ransomware usually experience something like this. They may find a ransom note on their screen, containing information about the encryption that has been applied to their files. There are hardly any symptoms that could reveal the encryption process while it’s still running, therefore victims can’t stop it before it locks all of their data. In the ransom note, they can find detailed instructions about how the payment should be made. The ransom is usually required in Bitcoins, which is a type of untraceable cryptocurrency. In order to make people pay faster, the crooks set a timer with a short period of time for the payment to be made. They may threaten to double the sum or even delete the decryption key if the victims don’t fulfill their demands.
Should you pay?
Dealing with the hackers behind the ransomware is a bad idea. Many security experts, including our team warn people about the risks of entering into negotiation with the cybercriminals. There is no guarantee that the victims would really get their decryption key if they make a payment. There are many cases of people who only burn out their money and never hear from the hackers again, or they get decryption keys that don’t work and remain with their data locked forever. There is another thing – the more people agree to pay, the more profitable and, of course, more popular this nasty form of robbery becomes. Therefore, one should carefully think if the risks are really worth the trouble. Removing the infection and restoring the files without paying is the best solution and in the removal guide below we are going to help you with some proven steps on that.
What is the best defense against Ransomware?
Firstly, ensuring your system protection from start to end is something you should never neglect. Suspicious online locations, sketchy content, and spam should be avoided. This would minimize your chances of interacting with malicious content. Proper antivirus and antimalware software should also be part of your system protection. However, in order to prevent the loss of precious data, you should keep a backup of all your valuable information on an external drive or a cloud. This is the best solution against Ransomware infections and you will always have your data copy at hand when you need it. Now, to clean your system from Cerber Ransomware, please proceed to the instructions below and in case you need any help, let us know.
SUMMARY:
| Name | Cerber |
| Type | Ransomware |
| Detection Tool |
Cerber Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

what is autoexec.bat? is it a virus?
We cannot be hundred percent sure, but if you do not know where it came from, you’d better not interact with it. You can send us a screenshot if you want. Do you have any idea how it got on your PC?
Sort the entries by date and see if anything has been added after or just before the moment of the first occurrence of the Ransomware problem. If you are not sure what’s new, you can send us a screenshot – just make sure to sort the folder by date.
Is there any way to decrypt the cerber3 files
Hello, Mrunmay. You should check out our guide on how to decrypt ransomware which is linked at the bottom of the article. There you can find all decryptors that we’ve found so far as well as instructions on how to use them in addition to other helpful tips pieces of advice.
Hello, we attacked the version that changes the file extensions on .b550. All files utility encrypt us.
Those two Ransomware viruses are fairly recent and are significantly more advanced than their predecessors which is why, unfortunately, there are no decryptors for them yet. We always make sure to post the latest decryptor tools and keep this article updated. We advise you to pay visits to this page every once in a while so that once we have found out about the release of a decryptor for those viruses, you will be informed about it.
Sadly, there aren’t decryptors for those versions of Cerber. As soon as we learn that such a tool has been developed, we will make sure that it gets posted on this page. Therefore, we advise you to visit this article every now and then in order to stay updated.
For detailed decryption instructions, we advise you to visit our How to Decrypt Ransomware article.
What note are you referring to?
https://uploads.disquscdn.com/images/d3082b9002cf1aabd154a6f98caf4ffdfb89b89e2d27856012fde89de9bfbc94.png I found these kind of notes in the directory that has been infected
It is a note from the Ransomware telling you how to make the Ransom payment. Normally, we would first advise you to try the guide form our article instead of going for the ransom payment.
We advise you to go to our How to Decrypt Ransomware article and see if the instructions there help you.
Thank you for your reply
But I do not seem to see the Cerber4.0 decryption method but only 1.0
How can i decrypt?
thank you very much
We are still looking for decryptors for this version of Cerber. So far, it seems that no decryptor has been released. You can try file restoration through shadow copies but success is unfortunately not guaranteed.
I think I got it off but the desktop screen still remains what can I do to get rid of it?
What screen are you referring to?
Check the Task Manger Processes tab and see if you can find the process behind the Ransomware message.
My folders/files got infected by cerber ransomware so any solution for decrypting files infected by cerber ransomware
Have you tried the guide we provide below the article. Also, you might want to visit our separate article on How to Decrypt Ransomware.
got these after local host. please email your suggestions at [email protected] thanks
127.0.0.1 down.baidu2016. com
127.0.0.1 123.sogou. com
127.0.0.1 http://www.czzsyzgm. com
127.0.0.1 http://www.czzsyzxl. com
127.0.0.1 union.baidu2019. com
127.0.0.1 down.baidu2016. com
127.0.0.1 123.sogou. com
127.0.0.1 http://www.czzsyzgm. com
127.0.0.1 http://www.czzsyzxl. com
127.0.0.1 union.baidu2019. com
You should remove those IP’s from your Hosts file as they aren’t supposed to be there.
Hello, you must first learn the exact name of the Ransomware to figure out if there is a valid solution for it. Use ID Ransomware as described in the beginning of the article above.
I have been attacked by cerber ransomware and all of my hard disk has been encrypted. I was wondering if your company could decrypt my files. The extension of my files are .84fe. Please provide me the quotation for this
Firstly, we advise you to complete the guide from the current page in order to remove the malware and clean your PC. Then, you can visit our How to Decrypt Ransomware article on this site and use the methods suggested in it to hopefully restore some of your data.
My all data in H.Drive got hacked, now they demand money in Bit coins currency, but I can’t afford. All the files got (RBS type) please help me out from this trouble.
Hello Sana Ullah, look for a file decrpyption program on our page, if there is none then I’m afraid this ransomware is not yet decryptable.
i have same problem
Hello
I have an old HDD encrypted with cerber, I guess. It has some files with cerber, but a lot of others with different types. SpyHunter recognize absolutely no threats when scanning.