This page aims to help you remove the Cerber Ransomware Virus. These Cerber Ransomware removal instructions work for all versions of Windows.
Cerber is a type of computer virus known among experts as Ransomware. This is currently probably the worst kind of virus that an end-user might get unlucky enough to contract. In this article we are looking to provide you with as much information about Cerber as possible. In order to do that we are going to explain how Cerber works, what its sub-type is (it’s a thing, seriously) and even discuss the pros and cons of paying the ransom demanded by the hackers behind it.
It would be a wise investment of your time if you allocate enough of your attention to carefully reading this article before committing to the actual removal of Cerber. It is quite important that you know what you will be dealing with before actually trying to uninstall it. So without further ado, let’s get down to it!
Cerber Ransomware
Types of Ransomware
You might be surprised to read this, but there are actually different types of Ransomware applications. They could be reviewed based upon the type of encryption used – whether it be RSA-4096, RSA-2048, AES-128 or something else. Yet I would explain them after first dividing them into two major groups – encryption ransomware and “pretend” ransomware.
- The “pretend” ransomware has been a very popular form of online-based extortion for a long time. Mostly in the years past, so it is a rare thing to encounter nowadays. This type of ransomware relies mostly on scare tactics to achieve its goals. Typically, it would lock the affected user out of the computer, displaying some form of threatening or embarrassing images on the user’s screen. In other words, the tried and tested “shock and awe” tactic fully utilized to extort some money out of unsuspecting users. This type of ransomware is actually easier to deal with, as it does not actually encrypt any of your files, which is probably why it’s become so rare nowadays in the first place. This type of ransomware is also known as a screen locker, due to the way it behaves.
- The much harder to cope with and much scarier type of ransomware is the one that actually does encrypt your files. Unfortunately, most of the ransom applications nowadays are of this kind. Cerber belongs to this group as well. We will explain how this process works in the next paragraph. Suffice to say that if your files have been encrypted, it will be tough to recover them. Yet there is some hope, and we will explain more further in this article.
How the Cerber Ransomware works.
Cerber finds its way inside your system by employing the help of a “friend” – a Trojan horse virus. Please take note of this and once you’ve dealt with the bigger problem, remember to also look out for the Trojan and eliminate it as well. It is most commonly distributed via email and the following information might even come across as familiar to you. Usually, you would receive an email in your inbox with either some form of attachment or a link to some website in it. The Trojan virus will typically be inside the attached file (this could even be a Word file) and will proceed to download the ransomware, as soon as you have opened the said file. Same goes for the link, if that has been the case – it will redirect you to a website from which Cerber may be downloaded from. Naturally, your consent won’t be asked for.
The encryption process is done via the help of two keys – a public and a private one. The job of the Trojan horse is twofold – it is supposed to download and install the ransomware on your machine, but it also has to connect to the remote server and receive instructions on what key to use. This means that offline computers are safe from the ransomware, as it will lay dormant until a connection to the remote server is established.
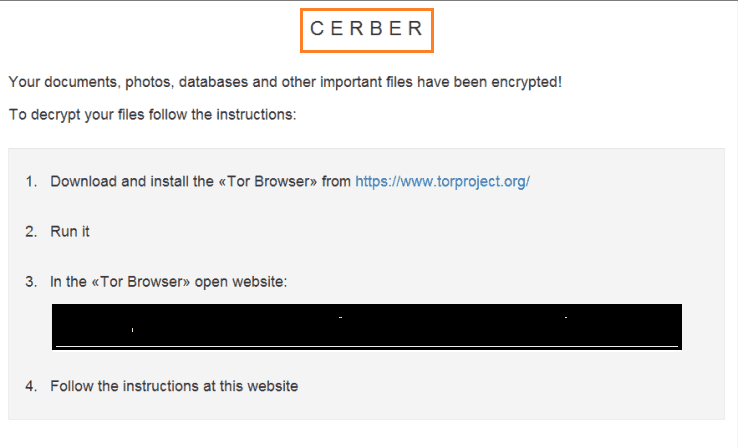
Once inside your computer, the ransomware will begin scanning your hard drives and compiling a list of your most often accessed files Cerber is capable of attacking both hard drives and removable flash drives, so keep that in mind and never plug-in a flash drive on a computer you know to be infected. As soon as that list is done, the encryption process of your files will begin. At that point you are really in hot water and realistically there’s not much you can do, unless you sense that there might be something wrong. A possible telltale sign of being infected could be that your computer is working at a terribly slow pace. If this is so, you will have to check your Task Manager for processed using the most RAM and shut your PC down as soon as you’ve discovered something suspicious. If the encryption process is successful, though, you will see a ransom “post-it” on your desktop the next time you start your machine. Usually by this point all of your files are encrypted, but if you are lucky it may still be possible to recover all (or at least some) of them.
Should you pay?
We will not pretend that this is not a hard decision to make. In fact, we encourage you to seriously consider your options. You should carefully review and determine how important the encrypted information is to you. If you are interested in our advice, however, we recommend NOT paying. At the very least, you should first try all other possible options. Please be aware that you are facing cyber criminals. There is no reason to believe that they will keep their “word” and give you a decryption key, even if you pay them. Also, keep in mind that the whole process of paying is extremely shady. Buying Bitcoins and trying to complete transactions in the dark web could turn out to be a recipe for disaster. It is a far safer option to follow our instructions and try to retrieve your old information back, than to indulge in speculative transactions with people facing jail time if ever caught!
Please note that no 100% sure method exists to recover your files. The alternative solution we propose involves restoring the original files before they were encrypted with the help of their shadow clone copies stored on your hard drive. This technique has a greater success rate if you haven’t recently written on deleted any files on your HDD and on how much empty space their was at the time of encryption. Unfortunately virus creators have caught up with this strategy and they frequently employ multiple writings and deletions of the same file to make their recovery method hard. There is nothing to be done about this – try your luck and if it works you are good, otherwise you can keep dwelling on the issue.
Cerber Ransomware decryption software – a scam
It is possible that you may encounter different offers for software, which is capable of restoring files encrypted by Cerber. Be very wary of those, as currently no working solution exist. Everything that promises such a functionality is either a scam or a program released by the hackers. Only they are the people who know the proper codes and this is just another way to go after your money.
SUMMARY:
| Name | Cerber |
| Type | Ransomware |
| Detection Tool |
Remove Cerber Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Hello,
Please copy/paste the whole line, not just the ip.
Did not find anything in processes down to Register but several entries with cerber were found however I received an error msg eact time I tried to remove /delete them!!!
Hello Steve,
What was the error message exactly?