CGGBT
CGGBT is a piece of malware, part of the Ransomware family. The ability of CGGBT to lock up the user’s files is what makes it a particularly dangerous virus. This is especially true when important user files are kept inside the attacked computer. Once the Ransomware gets to them, it may make them inaccessible for good.
The CGGBT virus
The CGGBT virus locks the targeted files through an encryption process. The reason the CGGBT virus does this is in order to extort money from you in exchange for the files’ release.
After the lockdown on the files is completed, the next step of the Ransomware’ agenda is to inform the infected customer through a desktop pop-up notification about the encryption process that has just been carried out and then blackmail them into paying a ransom for the key that could be employed to unseal the documents. The Ransomware’ notification typically provides strict instructions regarding how to send the requested ransom to the hacker who has sealed your private data. The money is required in return for the decryption code, which can allow the Ransomware victim to restore their access to the encoded data files. If the demanded money does not get paid, the user is threatened to never regain access to their data. In case you have come across this article because of the fact that you’ve had your system infiltrated by the nasty CGGBT, it is advisable to check out the remainder of the current article, as well as the added guide manual for eliminating, and fully removing the noxious Ransomware.
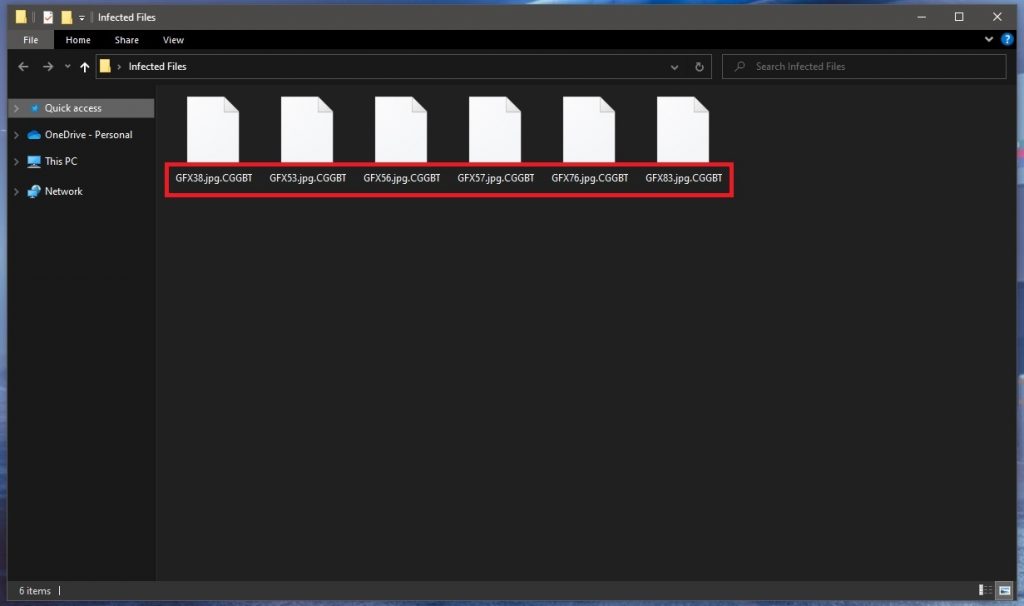
The .CGGBT file extension
The .CGGBT file extension is placed on your files, replacing their previous extensions. This makes the affected data unrecognizable to any software that you may have.
In addition, makes Ransomware such a huge problem is its ability to remain under the radar during the period it locks-up the targeted files. Sadly, even in cases where the user has their computer equipped with a good quality system security software, the presence of an antivirus might still be insufficient to spot the malware on time.
If you are wondering how Ransomware achieves such stealth, the answer lies in the fact that the file encryption method that it uses isn’t dangerous in itself. Sadly, this means that the chances of intercepting a Ransomware before it has gotten too late are quite low, because you, in most cases, cannot depend upon your anti-virus tool. However, once you know what to be on the lookout for, you might be able to spot a Ransomware cryptovirus invasion before it’s managed to secure your data files and replace their extensions. As an example, if you think your pc is operating in an unusual way, have a look at the Task Manager, and see if there are Ram memory or Processor spikes, which may expose a potential infection.
Additionally, to complete the encryption, the Ransomware virus programs such as Stax, .Cool demand free hard-drive storage space, which too may be regarded as a symptom that something sketchy is taking place on your PC. Those signs or symptoms are especially visible on machines which have a lot of data files kept on their hard-drives, or ones that are not too powerful. If you happen to notice anything which can be deemed suspicious, you ought to straight away turn off your computer and look for professional help.
SUMMARY:
| Name | CGGBT |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove CGGBT Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt CGGBT files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment