This page aims to help you remove the Check-now.online Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Check Now Online
Check-now.online is one of the latest pesky page-redirecting applications and here we will be focusing on it. Check-now.online is undesirable software that messes around with the search engine and the homepage of Firefox, Chrome, Internet Explorer and many more.
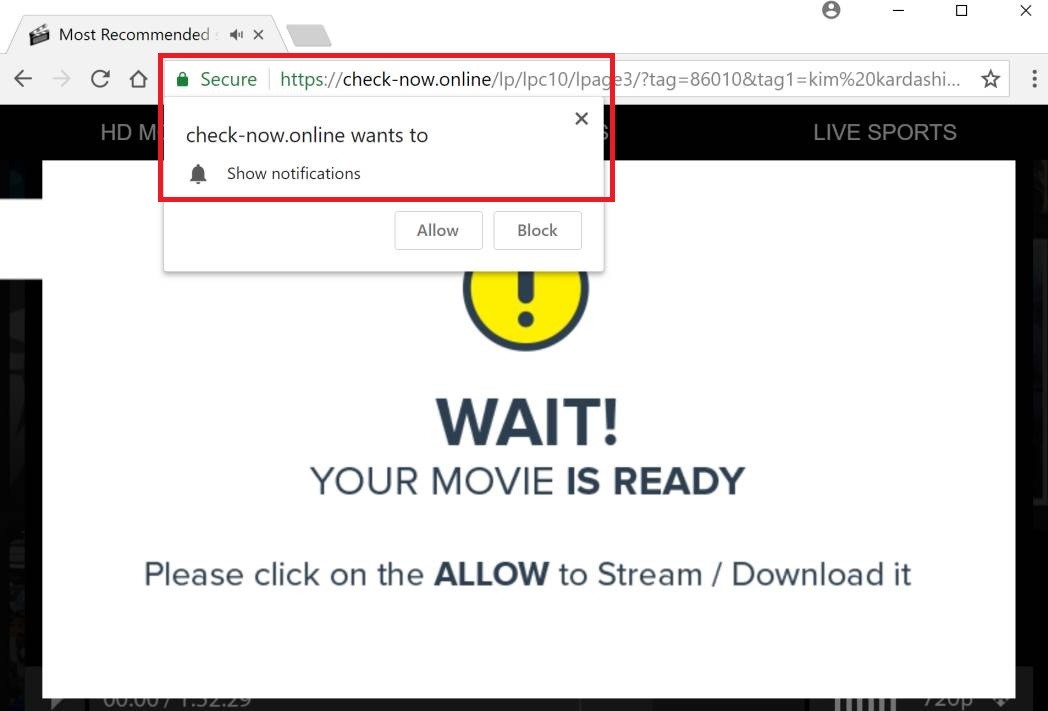
The Check-now.online Virus will display pop up ads and messages
Specific details about browser hijackers:
The possible ways in which such redirects may affect your system are explained in the intro. Usually, the targets of such hijackers are your browsers – none of them may really be spared. Check-now.online Virus and the page-redirects like it are specialized in changing the manners in which your Firefox, Chrome or Internet Explorer browsers work and the ways they look.
Also, you will see that the redirecting and the ad-production processes you might be experiencing could actually be related to your very recent search requests. If a representative of the hijacker get on your PC, it may be able to monitor your online activity. After that, such a the hijacker could connect the ad campaigns to the results of this research into your tastes and preferences. As a result, you might only see the pop-ups and deal with some redirection only to the sites the hijacker designers think you may like.
Is this illegal?
Really, this kind of activities might appear somehow too intrusive to some of its targeted users. Still, these redirects do not usually access any piece of sensitive data and, therefore, they do not perform anything against the law in most of the cases. Such redirecting and hijacking programs could be considered unwanted due to their typical features, and all the probable tricks they could use to get spread. However, most of the time no actual dangerous consequences would result from them. For the most part, hijackers simply seek t generate revenue for their creators through various online advertising models and techniques without really looking to cause damage to your PC or to your virtual privacy.
What about Check-now.online in particular?
Luckily, no matter how fishy browser hijackers may seem to be, they haven’t been classified as malicious. In comparison with actual forms of malware, browser redirects are not harmful in the real sense of the word. For instance, if your device has been infected by a form of a Ransomware virus, you might get harassed because such a virus never asks for your clear permission to access your PC, get installed there and encrypt something on it. You see – encryption like the one used by Ransomware does not normally result from the activities of any browser hijacker.
What if you can’t really remember installing any hijackers into your system?
Usually, such web page-redirects like Check-now.online may really trick you into installing them yourself. To begin with, it is necessary to mention that the greatest source of hijackers is normally some freeware distributed in the form of file bundles. Such bundles are sets of various apps, games and programs, and are normally free so you are able to download them from the web at any time. As it often happens, they may include some newly introduced apps and you might be tempted to try them for free to such an extent that you may completely disregard the fact that not all software added to the bundle might be something that you want installed on your machine.
Despite that, simply remember that any program or a bundle may be safely installed on your system – you don’t necessarily have to become a victim of any unwanted browser modifications, irritating ads or any suspicious consequences. You just have to install them right.
The only RECOMMENDED way of installing anything on your PC is to complete this process carefully by making sure to customize the installation process. The features providing this kind of customization opportunities are the ADVANCED or the CUSTOM/MANUAL setup options. Make sure that you choose that instead of the Quick installation option as that will likely have all bundled software opted-in by default which might get some unwanted applications the likes of Check-now.online installed on on your PC.
How to handle the Hijackers successfully:
To perform a successful removal process, we advise you to use the instructions in the Removal guide below.
SUMMARY:
| Name | Check-now.online |
| Type | Browser Hijacker |
| Detection Tool |
Remove Check-now.online Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment