*Source of claim SH can remove it.
Checkmate
Checkmate is a recently detected Ransomware representative and is likely the reason why a lot of this article’s readers have come to this page in the first place. The Checkmate ransomware can block the access to a number of valuable documents, archives, images, audios, videos or maybe even system files and ask you to pay a ransom if you want to access them again.
If you suddenly have lost the access to your most used and most valuable files due to an encryption that has been placed on them and if a scary ransom-demanding message is now asking you to pay money to access them, then most probably you have been attacked by a Ransomware cryptovirus like this and Eemv. Now, Ransomware, in general, is a very sophisticated form of malware and if you are about to deal with any of its representatives, you should carefully study all of your options. Sadly, there are not that many alternatives and, in some cases, the consequences of the attack might not be fully reversed. Still, in the next lines, we will offer you some methods which you might like to try in order to clean your computer from the infection and restore some of your files. The particular malware piece that we will focus our attention on goes under the name of Checkmate. However, you should not give your money to the hackers behind this infection right away. We are here to help you deal with the malware in the most sensible way and save whatever could be saved from your data without risking your money in the process. There is a Removal Guide below at your disposal as well as a trusted Checkmate removal tool for professional assistance.
The Checkmate Ransomware
Most of the victims who get attacked by the Checkmate Ransomware do not know how to react and what to do. If you are also confused, this is perfectly normal.
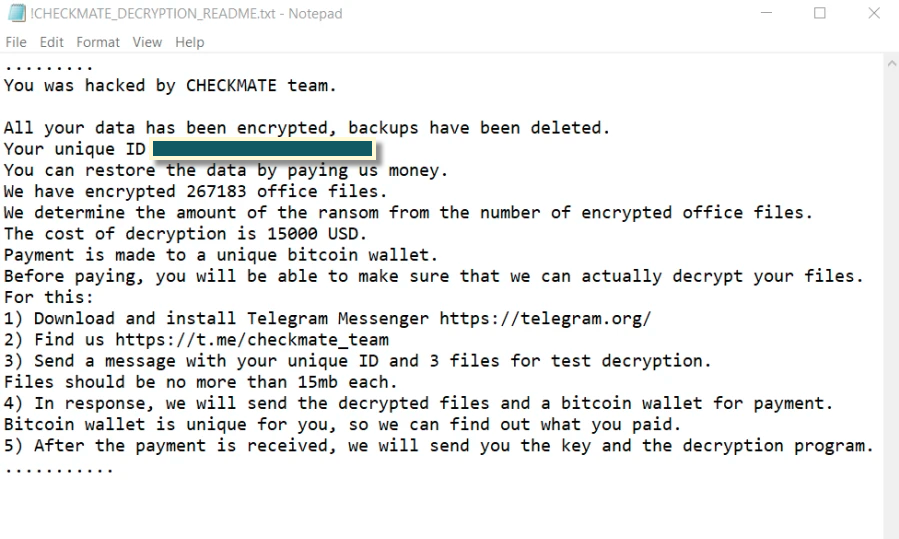
Usually, the sneaky virus gets inside the system in complete stealth and tries to remain hidden until it completes its nasty file-encrypting process. There are rarely any symptoms and, typically, the ransom-demanding message is what reveals the consequences of the attack. With its help, the hackers behind the infection state their ransom demands. They usually offer the victims to send them the decryption key if the latter pay a certain amount of money within a short deadline. Some people believe that this is the fastest way to regain their access and forget about the dreadful Ransomware, but we need to warn you that things might not go as smooth as the hackers promise. That’s why, we do not recommend that you trust them.
The Checkmate Virus
Malicious pieces of software such as the Checkmate virus are created for one single purpose – to blackmail their victims and extort money from them. That’s why, oftentimes, the criminal creators may use various tactics and threats to make the users pay.

They may promise to send a decryption key, they may lie about a helpful decryption solution or even threaten to delete all the data forever if the required money is not received. After the victims get scared enough to give their money, however, the crooks usually disappear. Those who have paid may oftentimes be left without a decryption key or may receive a key that doesn’t function properly and is unable to liberate the files. This is why, paying the money is risky and may not always yield the desired results.
You don’t have to lose your money, though. Since you are on this page, we suggest you take a look at the information from the guide where we have listed some file-recovery steps as well as good tips on where you can find copies of your data and recover it. If you wonder where to start from, first make sure you remove the Ransomware from your computer. This is very important if you want to make your PC safe for further use.
How to protect your PC from Ransomware?
There are many potential transmitters which can deliver Ransomware such as Checkmate to your system. Only one careless click on a misleading link, on a fake ad or on an infected email attachment could easily get your system infected and that’s why you should be very careful with the types of content you typically interact with while surfing the web. Do not get tricked by intriguing spam messages, harmless-looking pop-ups or offers which come from unverified sources. Most of these are commonly used channels for virus distribution and may carry exploit kits, Trojan horse infections or Ransomware inside of them. Sadly, without proper antivirus software, you may not be able to detect and remove them on time which is why you should not neglect the role of the reliable system protection and install a quality antivirus program on your PC if you don’t currently have one.
SUMMARY:
| Name | Checkmate |
| Type | Ransomware |
| Detection Tool |
*Source of claim SH can remove it.
Remove Checkmate Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:
After you open their folder, end the processes that are infected, then delete their folders.
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

*Source of claim SH can remove it.
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Checkmate files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment