Clear Your iPhone From Malicious Attacks
Clear Your iPhone From Malicious Attacks is a potentially unwanted software that can redirect your web searches to suspicious websites full of sponsored ads. Many web users refer to Clear Your iPhone From Malicious Attacks as a browser redirect virus that targets Safari, Google Chrome, Mozilla Firefox, and other popular browsers.

The “Clear Your iPhone From Malicious Attacks” Calendar Spam
You have likely become aware of the presence of “Clear Your iPhone From Malicious Attacks” due to the many pop-up ads and banners it has started to generate all over your screen. This is a common activity for many browser hijackers, which, apart from displaying ads, may also initiate page-redirects to various websites and install a new search engine or replace the homepage of your web browser.
Typically, apps like “Clear Your iPhone From Malicious Attacks” easily integrate with Chrome, Firefox, Safari, and other popular browsers and alter their settings without the users’ permission. There is no need to be too worried about the safety of your system, though, because the Browser Hijackers aren’t considered to be a serious threat to the security of the device they are installed in. Such programs are not identical to computer viruses even though many websites across the Internet may make you believe so.
Nonetheless, programs like “Clear Your iPhone From Malicious Attacks” are labeled as potentially unwanted, because they can be extremely annoying and, sometimes, may indirectly expose you to security hazards. That’s why we’ve created a removal guide to help you remove the annoying program and uninstall the changes it might have imposed on your favorite browser. But let’s first help you better understand the specifics of these apps as this will help you deal with them in the best possible way.
Is your device at risk?
The programs of the Browser Hijacker category don’t share any of the typical features related to more serious malware programs. They can’t hack into your system like a Trojan, and surely cannot encrypt your files like Ransomware. Yet, they may open the doors to external security hazards as a by-product of their activities, especially if you are not careful with the content they display. For instance, the pop-ups, the banners, and the box messages that a piece of software like “Clear Your iPhone From Malicious Attacks” may prompt you to click on may not be as safe and as legit as they seem. In reality, such ads can potentially take you to malicious websites containing dangerous programs like the aforementioned Ransomware, or other viruses. Of course, that fairly rarely the case, but when it comes to landing on malicious content, even one compromised ad and a single careless click from your side is enough to deliver malware into your system without.
This is exactly why we encourage the web users to refrain from interacting with any of the content that the Browser Hijacker may display, regardless of how appealing it may appear.
And if you’re not yet convinced that “Clear Your iPhone From Malicious Attacks” should be removed from your device as soon as possible, here’s one more thing to consider. The large amount of promotional materials the hijacker tries to display may often result in higher use of system resources. This, in turn, may result in sluggish system performance, screen freezing, and even browser crashes. So, while such software can often be marketed as a browser-enhancing tool, it seems that, in reality, it is quite the opposite and uninstalling it might be the best solution.
SUMMARY:
| Name | “Clear Your iPhone From Malicious Attacks” |
| Type | Browser Hijacker |
![]()
The main problem with Clear Your iPhone From Malicious Attacks that people have is the automatic addition of new events to the calendar and the sudden pop-ups caused by said events. if you have Clear Your iPhone From Malicious Attacks on your iPhone, you will likely notice that events are getting added to your Calendar app without your permission which, though not directly harmful to the device, could be quite unpleasant. Below, you can see a way to stop the unwanted addition of events to your Calendar.
- Log into your iCloud account on iCloid.com and select the Calendar app.
- Select the Settings icon indicated by a small gear symbol.
- Go to Preferences > Advanced and pay attention to the Invitation settings. Since you are getting your Calendar spammed with unwanted events, you will probably see that the In-app invitations option is checked. You must change that to Email to *your email* and enter an email address you have access to.
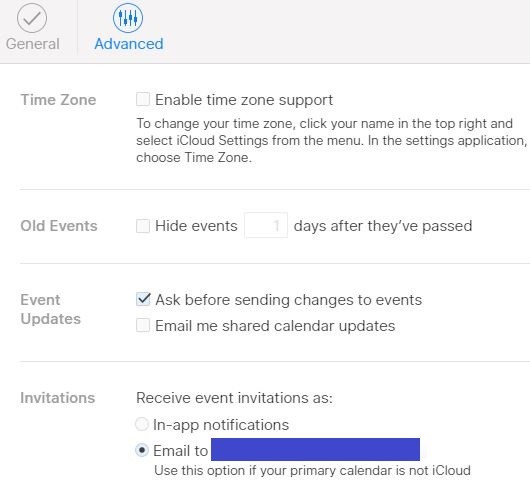
- Lastly, Save the changes so that they’d be applied and the Clear Your iPhone From Malicious Attacks hijacker should no longer be able to spam you with unwanted Calendar notifications.
Note: When providing your email address, it might be better to add an email that you don’t use all that often instead of your main one. The steps from above won’t technically stop the Clear Your iPhone From Malicious Attacks malware from spamming you but would simply redirect its spam attempts to an email address so that you don’t get the annoying notifications. In other words, the email you’ve provided will now be the one getting spammed and so, for that reason, it’s better if the provided email is one that you don’t use on a regular basis.
The previous steps will only stop the aggressive notifications but won’t take care of their cause. If you want to eliminate the Clear Your iPhone From Malicious Attacks malware from your iOS device, please, proceed with the rest of the instructions.
![]()
If there is a pop-up on your screen that you are not able to close down, you must first deal with it before you proceed. It is important to note here that tapping on any Close, X, or other similar buttons that seem to allow you to close down an aggressive pop-up are better left untouched. Tapping on them would more often than not lead to you getting redirected to the site that the pop-up originates from and if that site isn’t safe, you may get your device exposed to threats of different kinds.
Instead, if you want to close an obstructive pop-up message or banner that prevents you from using the device normally and proceeding with the guide, you should double-tap on the Home Screen button and then close all the applications that are currently active. This should make the pop-up disappear and allow you to continue with the guide. In case the pop-up remains on the screen after this, try restarting the device. First, you must Force Quit it by holding down its Power Button and swiping downwards once the Power Off option shows up on the screen. After your iPhone shuts down, start it back up by once again holding the Power Button.
Note that it may be a good idea to stop your Wi-Fi and mobile data so that the iPhone isn’t connected to the Internet as this may help with the completion of the next steps.
![]()
Next, it is time to carefully check what apps you have installed on your iPhone. More often than not, hijackers like Clear Your iPhone From Malicious Attacks enter iOS devices through the help of an app that looks relatively normal but carries the code of the unwanted hijacker software. Therefore, if you remember installing a certain app around the time or just before the calendar spam and the appearance of random pop-ups began, then you should probably remove that app. The same applies to any other application that you think may be somehow linked to the issues you’ve been experiencing. Once you figure out what apps you wish to delete, simply tap and hold that tap on the specific app and an X button should show up over its icon. Tap on that button and the app would be removed from the iPhone.
Note that apps that carry browser hijackers for iPhones are almost always downloaded from outside the official Apple App Store so if you have any such aps on your devices, you should start with removing them first. It is very uncommon for applications downloaded from the App Store to contain questionable code.
![]()
In most cases, completing the previous 3 steps should be enough to solve your problem by removing the browser hijacker and stopping the appearance of any unwanted and obstructive notifications and pop-ups. However, you must still make sure that your Safari browser is clean and that its settings are optimized for security.
To check the current state of your Safari browser, open the Settings app, find the entry for Safari and select it. There, you will see different browser settings and you mus male sure that the options labeled Block Pop-ups and Fraudulent Website Warning are enabled. This will prevent most forms of unwanted and aggressive pop-ups showing up inside the browser and will also prevent potentially unsafe sites from loading.
The next thing you must do is tap on the option labeled Clear History and Browsing Data – this will delete site cookies and cached data but you must bear in mind that it will also log you out of all online accounts that you were logged in through the browser.
If there are other browsers installed on your iPhone, you should repeat this step with them too because most hijacker apps affect all browsers that are installed on the targeted device.
![]()
Though unlikely, there is still a possibility that a browser-hijacking app like the Clear Your iPhone From Malicious Attacks one may be able to stay in the system of your device even after you’ve completed all the steps mentioned thus far. In that case, you may need to resort to performing a Factory Reset of your phone in order to clean it from the unwelcome software.
Some of you may not be very fond of the idea of preforming a Factory reset because you are afraid you may lose important data in the process but there is no need to worry because iPhones have a build-in function that allows them to automatically back up valuable data on iCloud so that nothing gets lost in case the data stored on the device gets damaged or deleted. However, before you Factory Reset the device, you must first check if the backing up feature is enabled on your phone. To do that, open Settings and select your Apple profile (at the top). Now, open the iCloud feature and look at the list of apps that gets displayed – if you think that the data stored in a particular app is important to you, the automatic backup feature for said app must be enabled so toggle it on if it is currently disabled. Usually, it is best to enable automatic backup for all of the shown apps so that no data gets list after the reset.
- Should you manually make a full backup?
Many people may be wondering if it isn’t a to use the iCloud Backup option and create a full data backup of everything that’s on the device. In other cases, this would indeed be a good option but in the current case, doing this may allow the malware app to also get saved on the backup and after you restore your data from the latter after the Factory Reset, the hijacker may enter the system of your iPhone once again, rendering the whole Factory Reset process pointless.
Once you are all set and ready to proceed with the Factory Reset, go to Settings once again, find and open General, and then find the Reset option. Select that option and proceed to provide your confirmation that you indeed want to perform a Factory Reset. The operating system will ask you multiple times if you are certain that you want to proceed so tap on Yes each time. Once the process starts, be patient and don’t turn off the device until everything is complete. Once the process finishes and the device restarts, you should no longer have the unwanted hijacker on the device.

The settings you say to go to are not available at all on the Safari app. There is no “Extensions” to go to, there is no “homepage “, there aren’t even “preferences”
I cannot load apps, am on an iPad that won’t even do an update to the software now. Please help.
Hi Laura Danis, have you tried closing any pop up windows before trying to enter preferences in Safari, you can try to reinstall your browser and then looking for those options after that.
How can i remove it on chrome?? Please help me
Hello Everyone,
I found that this issue, on 10s Max, can be found in the iPhone Settings, Password and Account.
Hello Everyone,
I found that this issue, in a10s Max, iOS 13.3.1 comes as a calendar invitation and it can be found in the iPhone Settings, Password and Accounts, then press on Subscribed Calendars, then calendar named:
“ CLICK SUBSCRIBE” ”ˢᵖᵒⁿˢᵒʳᵉᵈ ᵉᵛᵉⁿᵗˢ”
at the bottom press Delete Account.
Hope this helps.
THANK YOU!!!!
Thank you so much man, this got so annoying. I did not think I would be able to solve this.
You are genious
Thanks GenX6!
You saved my life
god bless you dear
Thank you so much!! That worked!!☺️????????
your post is so much more useful than the original article!
Thank you so much!
Kaine, it was in the original article, but a little bit further up than the steps. He simply made it easier to see, and added the name of one of the spam calendars. I agree, they should’ve made it the first thing on the page because it worked for me immediately too.
There is no option of subscribe calender in my iphone11
Thanks!
yes thank u so much. this crap was driving me crazy
Thanks a lot, It was really helpful !!!
When “Clear your iphone from Malicious attacks” pops up on your iphone, the other thing you can do it. From your iphone, Got to Settings -> Calendar -> Accounts -> Keep only your account and remove the other account and then refresh your calendar app on your iphone. This should permanently remove all the pop ups.
I got this malware after visiting a site that I searched with Google.
I noticed that this forum page was putting pop up messages right as
I was viewing it.
I have an Ipad 3.
Using the tip above from GenX6 I navigated to Mail, Contacts, CALENDAR
and voila this malware had made an account. The server listed
is nedonhimw.fun and then a long string of characters. The
description is Click ?? To Continue
I deleted the account.