Clown Ransomware
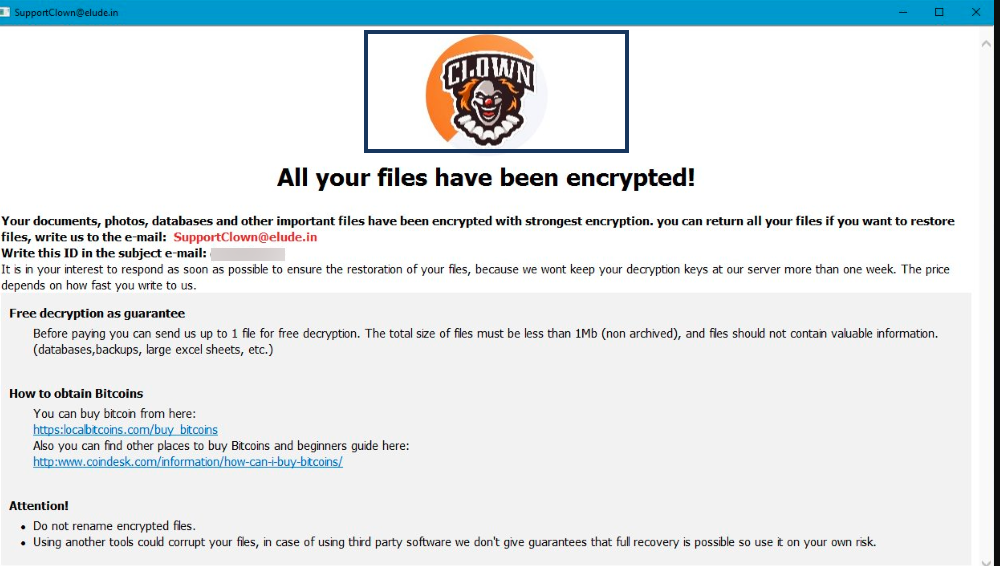
Clown is an infection based on ransomware that launches a stealthy data-encryption process on the infected computer and renders the files found there inaccessible. After completing the encryption process, Clown Ransomware place a ransom-demanding note on the computer and asks for a ransom payment to decrypt the encrypted files.
Typically, Clown Ransomware will begin to encrypt your files once your device has been infected. The problem is that this ransomware cyprovirus can lead to a major data loss, particularly if you store files that have a great value to you on the compromised computer. Clown Ransomware can turn a variety of file types into unreadable bits of data and can keep them inaccessible for an indefinite period of time or until a ransom is paid for them. Basically, this malware will try to extort money from its victims by blackmailing them for the decryption key of their digital information. The crooks behind the ransomware typically come up with an ultimatum and demand an immediate payment of a fixed amount of money which is usually required in Bitcoin or some other cryptocurrency.
As disturbing as this ultimatum can be, there are several alternative approaches that can help the victims of Clown Ransomware neutralize or at least minimize the effects of the attack to some degree and, in this article, we will talk about them. We will also discuss ways to avoid the encryption of new or recovered files in the future and methods that you can use to remove the ransomware cryptovirus from your system.
The Clown Ransomware virus
The Clown Ransomware virus is a piece of malware that prevents users from access to their digital files and forces them to pay a ransom for a decryption key. The Clown Ransomware virus blackmails its victims by applying an advanced encryption code to the files found on the infected computer and placing a ransom note on the screen.
The simplest and most successful way to escape the attack of a cryptovirus like this one is to regularly create backup copies of the most valuable information and keep these copies on an external disk, another computer or cloud storage. This helps you to still access your data from the backup even if a threat like Clown Ransomware hits you. And what is best, you don’t have to worry about paying some crooks a ransom to recover it. The only thing you have to do is remove the ransomware and copy your files onto the clean machine.
However, most users commonly neglect to back up their important files as often as they should. This is why threats such as Clown Ransomware may encrypt valuable files that users don’t have copies of. In such situations, a specially created decryption key is the only thing that can theoretically reverse the applied encryption. However, nobody can tell if such a key really exists. The people behind Clown Ransomware typically offer to provide you with it as soon as you transfer a fixed amount of money to their cryptocurrency account. Unfortunately, there is no guarantee that you will really obtain that key from them. That’s why we normally don’t recommend the victims of ransomware to transfer any money as a ransom because it will only make things worse if the hackers fade away with the money, without giving you anything in return.
The Clown file encryption
The Clown file encryption is an algorithm that gets applied to digital files to prevent users from accessing them. The Clown file encryption is incredibly difficult to remove and the files that get encrypted may remain inaccessible for an indefinite period of time.
Many users who need to urgently retrieve their data see no choice but to pay the ransom required by the hackers behind Clown Ransomware. But this is not the wisest thing to do and, instead of risking your money, on this page we have tried to give you a few different ways of handling the situation. In the removal guide below you can find some free file-recovery tips, as well as comprehensive instructions on how to remove the ransomware from your computer.
SUMMARY:
Remove Clown Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply