Cm99v
Cm99v is a file-attacking virus that experts label as Ransomware. Cm99v seeks to make every potentially important file on your computer inaccessible so that the hackers can later blackmail you for a ransom payment in exchange for the means to unlock your data.
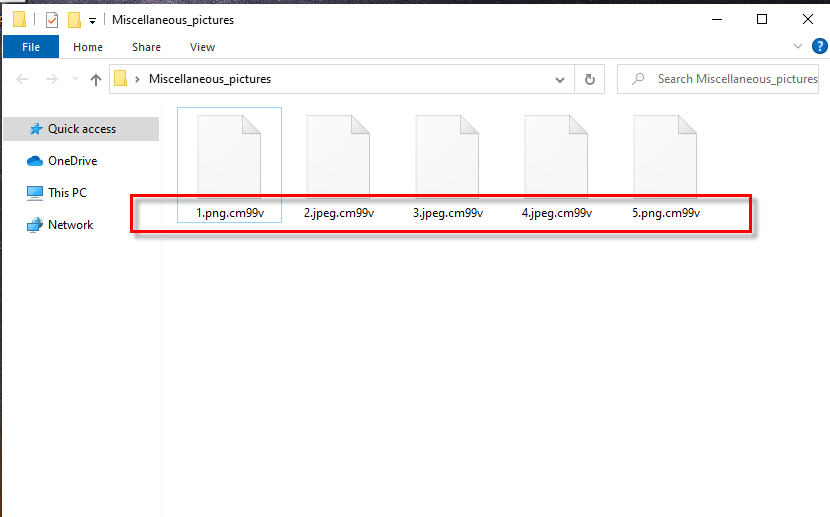
The Cm99v Ransomware will encrypt all of your files.
This type of blackmailing harassment that involves the use of a Ransomware virus is very common and, unfortunately, very effective too. The main issue here is that the virus that locks the files can silently sneak inside the computer because most Ransomware infections don’t trigger signs of their presence. In addition, the technique that is applied in order to make the files unavailable is known as data encryption, which means that once the files get locked by the virus, there is almost no way to open them other than the use of the corresponding decryption key.
The hackers count on that as they display a message on the Desktops of the infected computers through the Ransomware virus. This message tells the attacked victims all they need to know about the ransom payment required to get the key for their files. Many people who can’t afford to lose their important data give in to the harassment and pay the ransom. However, not all of the users who carry out the ransom payment get their files restored. There are a lot of examples where people have sent the money only to receive nothing in return. This is yet another big issue when talking about Ransomware because this means that even if you complete the hackers’ demands, you could still remain incapable of using your files.
The Cm99v ransomware
The Cm99v ransomware is devastating file-targeting malware that can cause severe data loss by permanently locking up the victims’ files. The Cm99v ransomware encrypts the files of the attacked users, and then it generates a note on the Desktop, where it demands a ransom payment.
If you don’t want to risk your money by sending it to the criminals, know that there may be some other options you can go for. We must warn you, however, that there can be no guarantees about the future of your files and about whether you’d be able to recover any of your data. Still, as you can see, even obeying the hackers doesn’t necessarily mean that your files will be recovered so it’s still better to first try the other possible options, some of which will be explained to you in our removal guide.
The Cm99v file recovery
The Cm99v file recovery usually requires the user to decrypt the locked files with the help of the corresponding access key. The Cm99v file recovery, however, may be complete in other ways, such as by using a personal backup or via the shadow copy restoration method.
There are also other alternatives and, even though they may not always work, they are mostly free to try and won’t require you to contact the hackers in any way or form. However, before attempting to recover your data, be sure to first remove Cm99v by following the next steps.
SUMMARY:
| Name | Cm99v |
| Type | Ransomware |
| Detection Tool |
Cm99v Virus Removal
![]()
For a start, we suggest that you Bookmark this page as you will need to get back to it to complete all the instructions from the guide.
Next, it is very important that you reboot your computer in Safe Mode in order to make it easier to detect and remove the ransomware. That’s why don’t skip this preparational step and use the instructions from the active link if you don’t know how to enter Safe Mode.
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Now, head to the Task Manager ( use CTRL + SHIFT + ESC key combination to open it) and then click on the Processes Tab. Try to figure out which of the processes from the list could be related to Cm99v.

As soon as you detect such a process, right-click on it and select Open File Location from the menu that appears. When you get to the file location of the process in question, drop the files found there in the free online virus scanner and run a scan:

When the scan completes, you will know if the tested process and its related files are really dangerous. If this is the case, end the process from the Task Manager and then go to its file location to delete all the files and their folders.
![]()
As soon as you are done with cleaning the malicious processes from the Task Manager, press the Start and R keys from the keyboard together. A Run box will show up on your screen where you have to copy this command:
notepad %windir%/system32/Drivers/etc/hosts
Click the OK button and this should immediately open a text file named Hosts on the screen. Go to the bottom of this file where it is written Localhost and check for unknown IP addresses. In case you detect some, just as it is shown in the image below, this could mean that your computer is hacked.

If that is is your case and you find a number of questionable-looking IPs below “Localhost” leave us a comment below this post so we can advise you on what to do next.
Another important thing that you need to do in order to remove Cm99v from your computer is to head to the System Configuration app (type msconfig in the search field and hit enter) and then remove the ransomware-related entries from the Startup tab. For that, click on the Startup tab as shown on the image and uncheck the checkmark from the entries that seem questionable or have an Unknown manufacturer.

Important! Make sure that all the startup entries that you leave checked are legitimate! Sometimes, ransomware threats may use fake process names and fake manufacturers to prevent their removal.
![]()
Next, after you uncheck the ransomware-related Startup entries, open the Windows search field, type Regedit, and press Enter. Then, when the Registry Editor launches, press CTRL and F together to open a Find box and write the name of the ransomware in the text filed. Then, press the Find More button and delete any entries that are found with that name. Perform the search as many times as needed until no more results are found.
Be careful! If you delete entries not related to the ransomware, you can damage your operating system seriously!
After no more entries show up from the search, go to the Windows Search Field and manually type each of the following:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
When you get to each of the locations, filter the files by date and see if anything new has recently been added by the ransomware. When you reach the Temp folder, delete everything that is contained in there.
In case you have doubts or questions, don’t hesitate to leave us a comment below this post and we will do our best to reply to you shortly.
![]()
How to Decrypt Cm99v files
The decryption of the files that Cm99v has encrypted is a topic for another guide that will show you in detail some file-recovery alternatives.
Make sure that you check it out here once you are done with the instructions for ransomware removal.
In case that Cm99v turns out to be more persistent than expected and doesn’t want to get fully removed from your computer, we recommend you to scan the system with the professional removal tool listed on this page. If any questions arise during any of the steps, we invite you to drop them in the comments section below where our team will have them answered.

Leave a Comment