CoNFicker
The CoNFicker Worm falls into the Trojan horse category. CoNFicker malware really relies on your naiveté, and the vulnerabilities of your system or of the programmers installed on it.
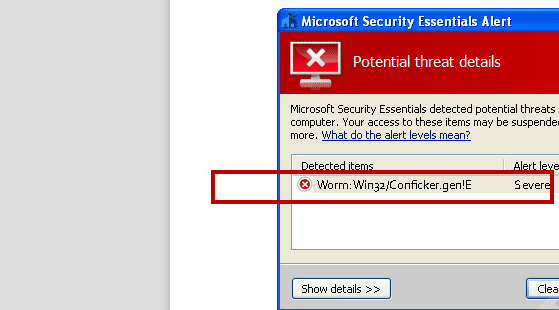
The CoNFicker Virus is a generic detection for a computer worm that is part of Win32/Conficker group
Perhaps you remember the old Greek legend about the Trojan War. This malicious piece functions exactly as the wooden horse from the myth. In the common cases, such a program attacks your PC silently, without any notion or any sign of its existence. . Furthermore, CoNFicker Worm almost never comes empty-handed, as such Trojans usually bring Ransomware along with them. In the description below we have further explained the effects that CoNFicker Worm may have on your PC. Following infecting your PC, this Trojan could reveal its true intentions. Nevertheless, the number of the possible ways of exploiting such viruses is very big. In the text below we will mention the ones that are most widely exploited.
The CoNFicker Virus
The sources that might be spreading CoNFicker Worm Virus are not limited to five or six. Such a malicious piece can hide inside torrents, shareware and video-streaming web pages, other contaminated web sites; as well as inside letters inside your email and their attachments.
Even opening text documents may get you infected. More precisely, you can never be absolutely sure, where this Trojan has come from in case your device has already been infected. What is really bothering about the spreading of this malware is the fact it might benefit from all the possible weaknesses your system/programs could have.
Perhaps you really have no idea that your OS or any of the installed software there is prone to being hacked, however, in case they really are, CoNFicker Virus can use this against you and infiltrate your computer. If you need an example of a program/system vulnerability, one of the most usual ones is an anti-virus tool, which hasn’t been updated for a long time and can’t protect your PC in the best possible way. Never miss any updates or renewals of the license of anti-virus programs, as in such a way you may risk getting infected with many malware versions. The same is true for your OS and any programs installed on it – outdated software may make your system more susceptible to external threats.
What might hackers be exploiting CoNFicker Worm for?
As a usual Trojan, CoNFicker Worm has all the characteristic features of any other virus from this category. In fact, its potential usages may be very diverse, depending on the goals of the hackers, who have created and sent this virus. More precisely, all Trojans are characterized by a very multi-functional nature. Some of the ways, in which they might be used, are:
- Intrusive activities such as spying on all of your online actions like entering credentials or passwords; online communication; online banking processes and/or making any payments. Actually, your entire identity in terms of the data about you available on the web may also be what hackers need to access, change or use in any way.
- Destruction-oriented actions like deleting certain files; even crashing your entire system; or making it function as a bot and send spam as well as mine cryptocurrencies.
- Allowing an even more dangerous malware version than itself to invade your system. Ransomware-like viruses could be described as the worst and the most harassing programs you may ever come across on the web. They can use Trojans to infect your devices, and after that – they can do a research on your most used files, and encrypt them all. Late on, you will be required to pay a ransom in exchange for the access to your encrypted data. Maybe this one is among the most bothering usages of Trojans – the assistance they may provide to other malware versions.
Removal of CoNFicker Virus:
We are thrilled to let you know that we have come up with a possible solution to your issue regarding CoNFicker Worm. Below you will find our removal instructions. We believe that by following them in a careful way, you will be able to remove this virus completely and successfully. Nonetheless, remember to check the Task Manager of your system for any possibly suspicious activities which might be Ransomware-inflicted, as CoNFicker Virus may not have come alone. Be careful and good luck!
SUMMARY:
| Name | CoNFicker |
| Type | Worm |
| Detection Tool |
CoNFicker Worm Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment