.Coos
.Coos is a computer virus that blocks valuable user files and doesn’t release them until a ransom is paid by the user. .Coos is a form of malware that doesn’t typically trigger any visible symptoms, making its attacks very difficult to notice in time.
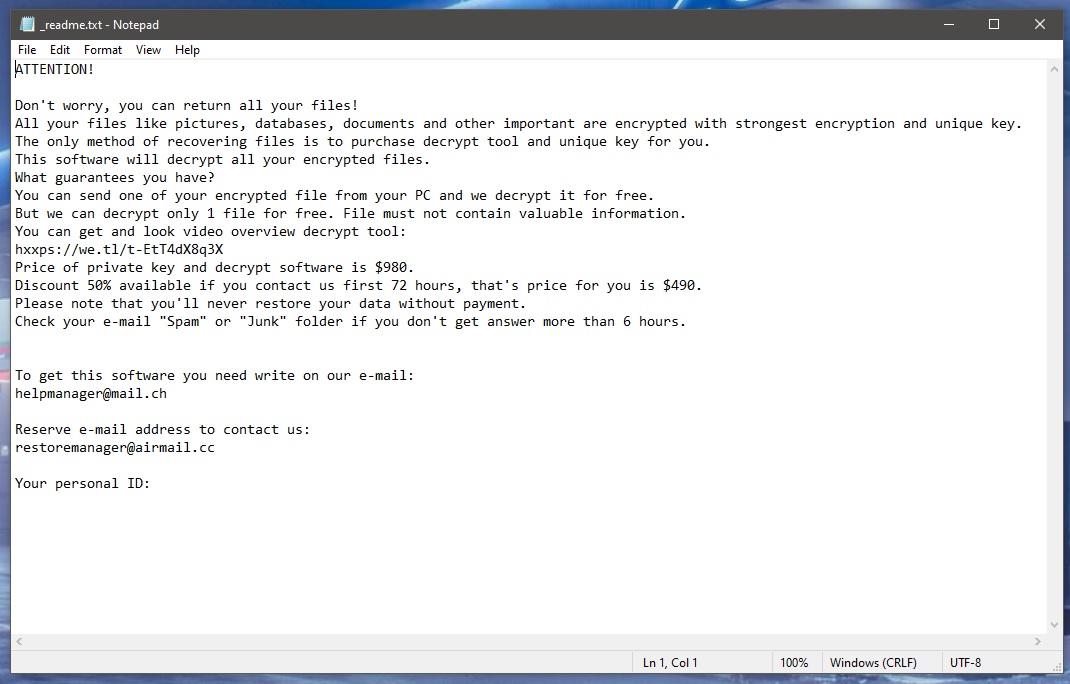
The Coos virus will leave a _readme.txt file with instructions
Once the virus enters a given computer, it immediately scans the machines for certain file types. Any piece of data belonging to the predefined file types that’s present on the computer is to get encrypted by the Ransomware. Typically, the file types targeted by the Ransomware are ones that are commonly used and are likely to contain sensitive information. The idea is that the virus would lock up some highly valuable files that its victim cannot afford to lose. After that, .Coos would request a ransom payment for the decryption key that corresponds to the data-encryption applied to the files. Of course, not all victims of Ransomware keep valuable data in their systems. Those who don’t aren’t too affected by the virus attack because they don’t stand to lose any particularly important files. Another group of users who would probably not have too much trouble dealing with .Coos is the one that consists of people who have exhaustive file backups. A file backup could pretty much negate all the harmful effects of a Ransomware attack because it ensures that the user always has safe and accessible copies of their valuable files.
The .Coos virus
The .Coos virus is a threat that attacks Windows computers with the aim to make the files stored on them unavailable. The .Coos virus launches a data-encrypting process to complete its goal and then displays a ransom-demanding message on the infected computer’s Desktop.
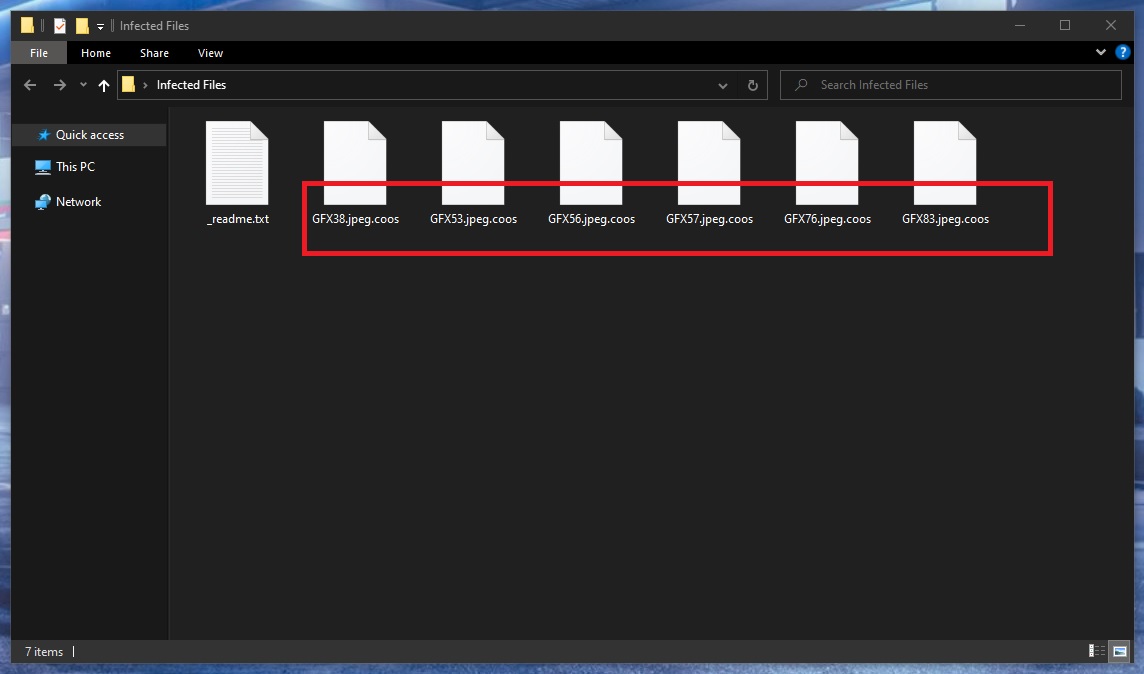
The Coos Virus will encrypt your files
Within this intimidating message, the attacked user is told that there is only one way they could get their files back and that is the payment of the demanded ransom. Obviously, these claims are primarily there to intimidate you. As you can already see, if, for example, you have previously backed up your files, there won’t be any need to pay the ransom. However, what if you have no backups and the files locked by the Ransomware are important to you. Well, then it would be a good idea to try some of the alternatives you will find in our guide.
The .Coos file encryption
The .Coos file encryption is a file-locking method that employs the use of a sophisticated algorithm that makes the affected files unreadable to any program. The .Coos file encryption can be overcome through the use of the matching decryption key generated by the virus.
This key, however, won’t’ be given to you unless you pay the ransom demanded by the Ransomware. The problem is that it may not be given to you even in case you complete the payment. There are simply no guarantees here because, after all, the people behind viruses like .Coos, .Qlkm, .Igal are anonymous online criminals. This is why we would advise you to opt for our guide and remove the Ransomware with its help. After that, you can focus on the file-recovery suggestions that may allow you to bring some of your most important files back without paying a ransom.
SUMMARY:
| Name | .Coos |
| Type | Ransomware |
| Detection Tool |
Remove .Coos Ransomware
![]()
We highly recommend that you Bookmark this page before you move to the steps below as, during the removal process, you will be asked to exit your browser and you will need to quickly refer back to this page if you want to complete the whole guide.
The next thing that you need to do after you bookmark this article is to reboot your computer in Safe Mode (use the instructions from the active link). Safe Mode will run only the most essential programs and processes and will help you detect and remove .Coos much easily.
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
The actual removal of .Coos starts with the detection of the ransomware-related processes in the Task Manager. For that, open the Windows Task Manager app (use the CTRL + SHIFT + ESC key combination) and then click on the Processes Tab. The moment you do that, you should be able to see a detailed list of the processes that are active on your computer. The challenge here is to correctly detect the .Coos-related processes as it is not necessarily that they have the same name as the ransomware.

One quick way to check a process that you find questionable is to right-click it and select Open File Location. Then use the free online virus scanner below to scan the files that are found in that location:

As soon as the scan completes, you will see the results, and if the tested files end up being malicious, you should go to the Processes tab, end the related process and then delete the malicious files and their folder.
![]()
The next thing that you need to do when you are done with stopping the .Coos-related processes from the Task Manager is to check the Hosts file of your computer for any signs of hacking.
For that, press the Start and R keys from the keyboard together and paste this command in the Run box that pops up on your screen:
notepad %windir%/system32/Drivers/etc/hosts
Press the Enter key from the keyboard and this should immediately open a text file named “Hosts” on the screen. Inside that file, go to the Localhost section at the bottom and check if there are any strange IP addresses below. The image here describes exactly what you should be looking for:

Normally, there shouldn’t be any suspicious IPs below “Localhost” but if they are, this could be a possible indication that the computer has been hacked. However, don’t be too quick to confirm this, and better write to us in the comments below this post so we can give you a professional answer.
Next, you need to remove the ransomware entries from the system startup. This can be done from the System Configuration app which can be opened by typing msconfig in the windows search field and pressing the enter button. On the window that appears, select the Startup tab and see the list of entries there.

Similar to what you did in the Task Manager try to detect which of the startup entries are dangerous and are related to .Coos and simply Uncheck the checkmark from the box in front of them. Do the same for any entries with “Unknown” Manufacturer and make sure that you leave only legitimate entries in this tab.
![]()
Ransomware infections like .Coos may add some entries in the Registry in order to facilitate their malicious processes in the background of the system. That’s why you have to go to the Registry Editor app (type Regedit in the windows search field and press Enter) and search for any entries that have the same name as the ransomware. The quickest way to do that is to press CTRL and F keys from the keyboard once in the Registry Editor and to type the name of the virus in the Find dialog box. Next, click on the Find More button and delete any results that are detected.
Attention! Your system can be severely damaged if you delete entries unrelated to the ransomware! Be extremely careful what you delete in the Registry Editor and if you run into any trouble, don’t hesitate to write to us in the comments section below this post.
Next, you have to manually go to the directories below by typing each of them in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Once you get to each of the above directories, check if anything new has recently been added to them. When you reach the Temp folder, delete everything that is found there. If you face any difficulties during any of the steps, remember that you can leave us a comment below and we will do our best to help!
If the ransomware is persistent and doesn’t want to get removed even after you complete all the steps in the guide, we recommend that you scan the computer with the professional removal tool found on this page to check and remove any hidden malicious files.
![]()
How to Decrypt .Coos files
The decryption of the files that .Coos has encrypted is a challenging task. Thus it requires a separate guide with more details about the file-recovery solutions, as well as some steps that may help you get some of your files back. You can check the file-decryption guide here.

please tell me what to do with spy hunter, im afraid i might do something wrong so please tell me what to do with it
Hello brooke, I don’t think there is something to mess up with SpyHunter, it’s pretty straight forward. You just download and install it, after that you can scan your computer for viruses completely free and when it is finished it will offer you to either buy the product or wait 48 hours to clean your system for free. It will help you with malware removal, but if your files have the .coos extension they cannot be decrypted, because this is one of the newest ransomware variants.
thank so much