.Coot
.Coot is a Ransomware virus that “kidnaps” its victims’ files by locking them. .Coot will not release the files unless the victim sends money to the virtual purse of the hacker.
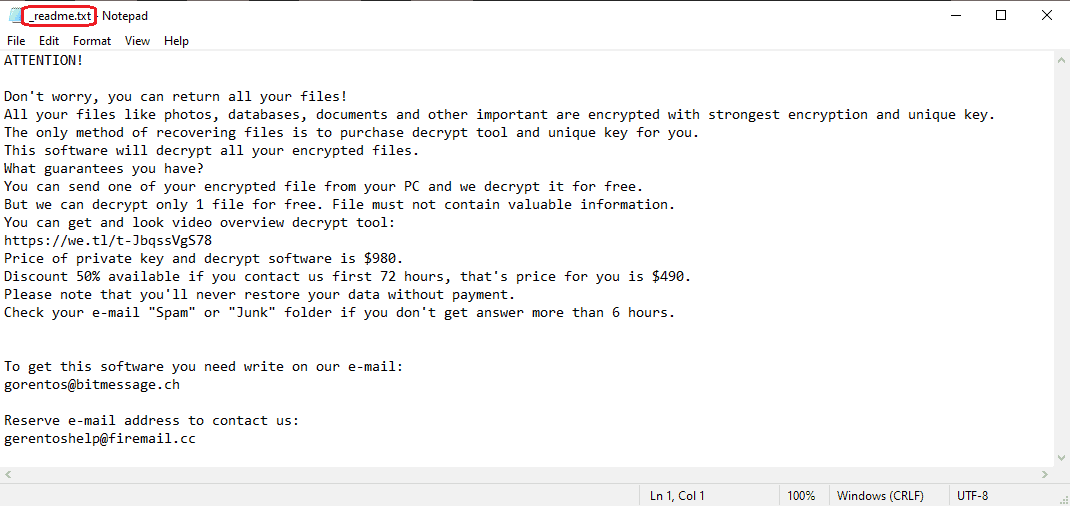
The .Coot Virus will encrypt your files and leave a _readme.txt file when it is done.
Once .Coot infects the system, it will first scan its hard-drives, seeking user files that may be important. Typically, the Ransomware has a list of data formats that it looks for in the infected PC. The formats are of commonly used types of data such as text documents, image files, spreadsheets, presentations, audio and video files, and so on. Once the scan is over and the Ransomware has located the files it is searching for, it will begin the process of encrypting them. During the encryption, each of your files is copied. The copies are identical to the originals in all aspects but one – they are encrypted with the Ransomware’s encryption algorithm. This encryption is what keeps those files inaccessible, and what allows the virus to proceed to the final step of the attack – the ransom demand. However, before it gets there, it first deletes your original files so that you only have the copies that you cannot access.
Once this complex encryption procedure is completed, the malware program informs you about exactly what has happened to your files – it tells you that they have been encrypted, and that a special key is needed to allow your system to read through the encryption. Of course, this key would only be given to you if you send a big sum of money to the hackers.
The .Coot virus
The .Coot virus is a dangerous computer program from the Ransomware category. The .Coot virus is aimed at “kidnapping” your files, and forcing you to pay money to release them.
The problem with the Ransom payment is twofold. Firstly, the sum you are told to pay would typically be quite high, oftentimes a four-digit number. Secondly, the completion of the payment can in no way guarantee the restoration of the files in your system. The hackers behind .Coot, .Nols and .Leto may promise you the key that corresponds to the specific encryption placed on your data, but there is nothing that can make them send it to you after you pay. Many hackers simply scam their victims, and get their money without even helping them solve their encryption-related problem. This is why one of the most common pieces of advice given by numerous specialists in the field of virtual security is to refrain from issuing the payment, as this could oftentimes lead to more trouble. So, if the payment isn’t a reliable solution, what is?
The .Coot file encryption
The .Coot file encryption is the method the ransomware uses to lock the data in your computer. To release the data from the .Coot file encryption, you’d need a unique key.
One thing you need to understand about Ransomware is that you must make sure to remove the threat even if this doesn’t automatically set your files free. If the cryptovirus stays in your computer, more files may get locked-up in the future, and you may get blackmailed again. Also, once you remove .Coot, you’d be free to safely try some of the data recover suggestions that we have included in our guide. This is actually what we would advise you to do instead of paying the hackers. Sadly, this is by no means a universal solution, but it is still a step in the right direction. That is why, if you have had your files encrypted by .Coot, it’s best if you try the next guide, remove the malware program with its help, and then check out the alternative recover suggestions.
SUMMARY:
| Name | .Coot |
| Type | Ransomware |
| Detection Tool |
.Coot Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Provide a help regarding this
I m using windows 10
N coot virus affecting all over my system pls asap
guys have you found how to recover files affected by .coot virus??
plz help me guys
suspicius ip
0.0.0.0 serius.mwbsys.com
0.0.0.0 keystone.mwbsys.com
You must delete those IPs from the Hosts file – they must not be present there.
Hello,
Please did anyone got a solution on this .coot thing?It has changed my file type to coot,
please I am requesting a guys
did u find any solution?
the same thing has happened to me