*Source of claim SH can remove it.
Core Sync
Core Sync is originally a component related to the Creative Cloud desktop app and gets installed along with it in order to sync data between your computer and Creative Cloud. Malware, however, may often use the Core Sync process as disguise and insert a Core Sync file that is not genuine.
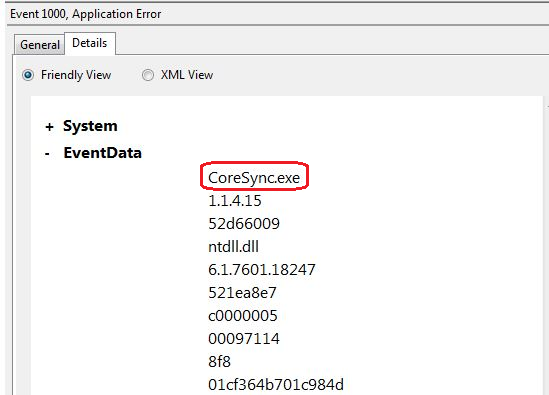
If the location of CoreSync.exe is in a subfolder of the Windows folder for temporary files, then this mean that your system has been compromised to a Trojan Horse virus.
The Trojan Horse viruses are pretty common online infections. Yet the majority of web users still don’t know much about these terrible threats. For instance, we have received a number of messages from users who have been infected with one of the new Trojan Horse variants called Core Sync. The users have been asking questions about how to deal with the infection and what to expect from it. That’s why we’ve come up with the current article and the removal guide that you can find below. But before you go to the instructions there, we suggest you read the information that follows to learn a bit more about what Trojans like Core Sync might be able to do.
What is Core Sync?
Core Sync is a component created to automatically sync files with Adobe’s servers. In some cases, however, Core Sync may be a Trojan in disguise that may run malicious processes in the background of your system.
A key feature of all Trojan Horse viruses is the fact that they can hardly be detected by regular web users without the help of a strong security program. That’s what makes infections like Core Sync a preferred tool for any hacker or cybercriminal. As a matter of fact, a Trojan can go unnoticed for weeks, or maybe even months, so it’s great that you actually got to know about the presence of Core Sync on your computer. Sadly, we can’t tell you what kind of harm to expect from the infection since one of the qualities of the Trojans has to do with their versatility. With the help of a program like Core Sync, a hacker can do anything from data theft and espionage to total system destruction, and more.
CoreSync
CoreSync is a malware with cryptocurrency mining functionalities that malicious actors use to trigger and conceal their cryptomining operations. CoreSync uses background processes and files of the system to launch mining operations that exploit the resources of the infected computer.
Core Sync.exe is the name of a cryptojacking Trojan horse and should not be mistaken with the genuine Core Sync.exe file which is a software component of Adobe Acrobat by Adobe. The location of the malicious Core Sync.exe file will be in a temporary file folder.

One of the possible uses for Trojan-based programs is for malware distribution and delivery, so the presence of Core Sync on your computer can lead to potential infection with Ransomware, Spyware, and who knows what else. A Trojan can also be used to turn your computer into a bot and allow the hackers to control it remotely without you even suspecting it. You may become a subject of 24/7 surveillance, a victim of money theft or theft of valuable information which not only can be sent to the hackers’ servers but also could be destroyed after that.
As you can see, Trojans such as Core Sync are not to be underestimated and it is important that you quickly remove the one in your system. As mentioned earlier, you can use the removal instructions below but they may not always get rid of everything related to the malware program. That’s why, in case of doubt or if you need to speed up the removal process, you can use the professional removal tool posted below instead. In just a few minutes, this tool will scan the infected device and will find and remove Core Sync from your machine.
The CoreSync Virus
The CoreSync Virus is a stealthy computer infection that sneaks without the users’ concent and launches cryptojacking operations. The CoreSync Virus is categorized as a Trojan Horse and is used to generate profits for its criminal creators. In most cases, Core Sync can provide the hackers with remote access to the infected computer and let them manipulate different system processes.
And as soon as you successfully remove Core Sync from your computer, it would be wise to take appropriate precautions to prevent potential future infections. You can start by getting your device updated with all the latest updates and by installing an antivirus or an anti-malware program of good quality. Another important aspect of having a virus-free computer is making sure you don’t visit questionable web locations and keep away from spam, emails from unknown senders, and suspicious attachments.
SUMMARY:
| Name | Core Sync |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
How To Remove Core Sync?
Core Sync should be removed as soon as possible as it may secretly launch cryptomining and other malicious processes in the background of the system and eat up a large portion of the computer’s resources. The removal guide below explains the exact instructions on how to remove Core Sync, so please, follow them carefully if you want to deal with this threat.
If Core Sync has infected your Windows machine, please continue with the guide on this page.
If Core Sync has infected your Mac computer, please use our How to remove Ads on Mac guide to deal with the infection.
In some cases, Core Sync may be removed from the system with the help of these quick instructions:
- Open the Start menu of your windows by clicking on the Start button.
- Then, navigate to the Control Panel and select Programs and Features
- In the list of programs that have been installed on your computer, search for Core Sync, as well as apps that could be related to it.
- Once you find it, uninstall Core Sync by right-clicking on it or by selecting the Uninstall button at the top.
- Do the same for any other questionable or unfamiliar programs that you can’t remember installing yourself.
If these instructions can’t help you to get rid of Core Sync completely, then follow the step-by-step removal guide below:

Before you do anything else, please Bookmark this page so you can refer back to it quickly because during the removal process you will need to quit your browser and relaunch it again.
Next, make sure you Reboot the computer in Safe Mode so that only the most nessesary processes and apps are launched.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Now, head to the Windows Task Manager so you can check what processes are currently running on your computer.
Press the CTRL + SHIFT + ESC key combination and tap on the Processes Tab. Once you get there, look at the list and try to figure out which of the active processes are malicious and could be related to Core Sync. Keep in mind that it is not nessesairy that they have the Core Sync name which is why you may need a bit of computer knowledge to filter the regular system and app-related processes from the malicious ones.

Once you determine the dangerous processes, right click on each of them individually and select Open File Location. Then scan the files in that location with our free online virus scanner to check if they really are malicious:

If the scanner flags them as threats, end the processes related to these files and delete the folders that contain them.
Note: In case the scanner doesn’t identify something as a threat but you are 100% sure that it is part of the infection – don’t leave it on the computer but delete it. Sometimes, new threats may remain under the radar of even the best security software for some time.

Once you are done with removing the malicious processes, press the Start Key and R keys together and, in the Run box that openes, type appwiz.cpl.

Click OK and the Control Panel will open. Carefully check for suspicious entries in there and uninstall them. A dialog box like the one below may show up when you click the Uninstall option:

Make sure you select NO.

*Source of claim SH can remove it.
Then, open the System Configuration by typing msconfig in the search field and pressing enter.

Select the Startup tab from the tabs that are available. You will see a list of StartUp items. Find the ones that have an “Unknown” Manufacturer or look suspicious and remove the checkmark infront of them.
- Important! Your computer might be hacked by some other malware (such as Ransomware, Spyware, etc.) while the present threat is in the system. To rule out this possibility, you need to check your Hosts file for other IPs:
To open the Hosts file, press the Start Key and R keys together and copy this in the Run dialog that opens:
notepad %windir%/system32/Drivers/etc/hosts
Hit the Enter button to execute the command.
As soon as you do that, a new file that looks like this should open:

If you notice that there are a lot of suspicious IPs below “Localhost“, this might be an indication that you have been hacked. Please, write us in the comments if this is your case, so we can advise you on your next actions.

In the final step, you will deal with the Registry Editor and will have to find and delete the directories related to Core Sync.
To open the Registry Editor, type Regedit in the windows search field and press Enter. Then, open the Find dialog (CTRL+F) and in the empty text box type the name of the threat that you are searching for. Right click and delete any results with this name (or a similar one). After that, go manually to the directories below and delete/uninstall them:
- HKEY_CURRENT_USER-Software-Random Directory.
HKEY_CURRENT_USER-Software-Microsoft-Windows-CurrentVersion-Run-Random
HKEY_CURRENT_USER-Software-Microsoft-Internet Explorer-Main-Random
In the event that the steps in this guide can’t help you remove Core Sync, then you may need to download the recommended anti-virus program on this page or try our free online virus scanner. In case any questions arise, we will be glad to answer them in the comments section below.

Leave a Comment