This page aims to help you remove Cosakos Virus Ransomware for free. Our instructions also cover how any .cosakos file can be recovered.
The computer threat represented by Ransomware cryptoviruses isn’t anything new – this type of malware has been around for much longer than most users may thing, dating back to the end of the last century. However, it wasn’t up until the past several four or five years that these malicious computer infections became such a huge and global threat on the Internet. Currently, Ransomware is one of the worst possible forms of malware that you can get inside your computer, and the main reason for this is because if you get your files encrypted by such a virus, you may never get them back no matter what you do. Still, giving up trying to minimize the damage done by a Ransomware is definitely not something that we would advise you to do. In fact, we are writing this article to help our readers with Cosakos – this is a new cryptovirus that was recently set loose on the Internet and it is currently looking for its latest victims. If you have Cosakos in you computer, after reading this post, you should be able to make an informed decision about what to do next in order to deal with this infection in the best way possible.
How does the .Cosakos virus operate?
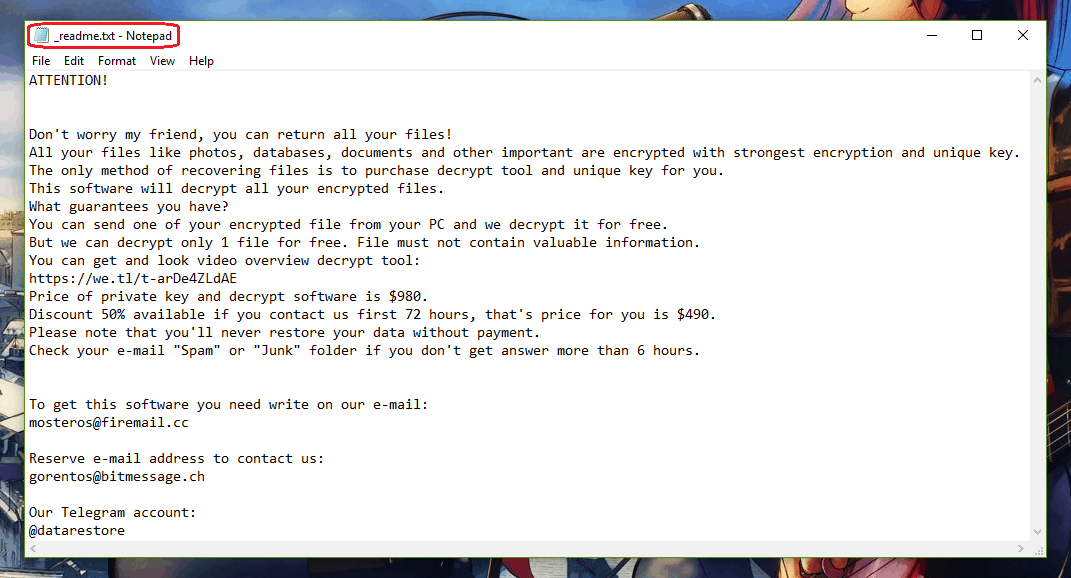
You will find this message left by the .Cosakos Virus in a _readme.txt file.
Once it infiltrates the computer, Cosakos much like other ransomware such as Mogranos or Nelasod silently initiates a data-encryption process, which covertly encrypts all of the personal user files in the computer. Though certain symptoms like increased RAM and CPU use, as well as decreased free storage space, may be observed, it is rather difficult to notice them, especially on a more powerful computer.
After the completion of the encryption process, the Ransomware goes on to display a ransom-demanding message on the screen of the invaded machine. The message is usually in the form of a big banner or a notepad file placed on the Desktop, and the text in it informs the victim that the only way to receive the decryption key for their files is if they send money (usually in BitCoin) to the hackers behind Cosakos. Sending the ransom money, however, isn’t a particularly good idea – there is always the risk of not getting the key for your files even after the payment has been made in accordance with the hackers’ demands. This is why our suggestion for you is to try to eliminate the infection and then try some of the alternative restoration suggestions that you will find here.
Recovering from the .Cosakos file encryption
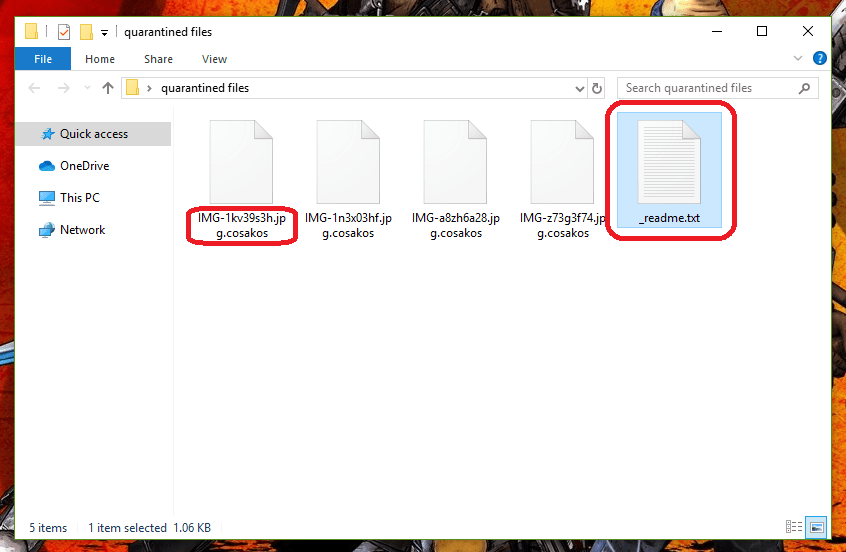
How an encrypted .Cosakos File looks like.
In order to be perfectly honest with you, we must tell you that such a recovery may not always be an option at the given moment. If you remove the virus, you will likely still need to deal with its encryption as it would still be on the files. Some of the possible alternatives we have here may work, but there is no guarantee of that. This is why it is important to check your other devices, online accounts, and clouds for the presence of any forgotten backups – you can use these to restore some of your data in case all else fails, but make sure to first remove the virus with the help of the removal guide below before you attempt to restore any of the files, or they may get encrypted all over again.
SUMMARY:
| Name | Cosakos |
| Type | Ransomware |
| Detection Tool |
Cosakos Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Please anybody help me . The ransomware has encrypted all files in my computer (except folders and shortcuts) to .cosakos . I already reinstalled my Windows 10 for this problem . But the files are the same . I am begging you guys please tell me a way to decrypt these files .