What is the Nelasod Virus?
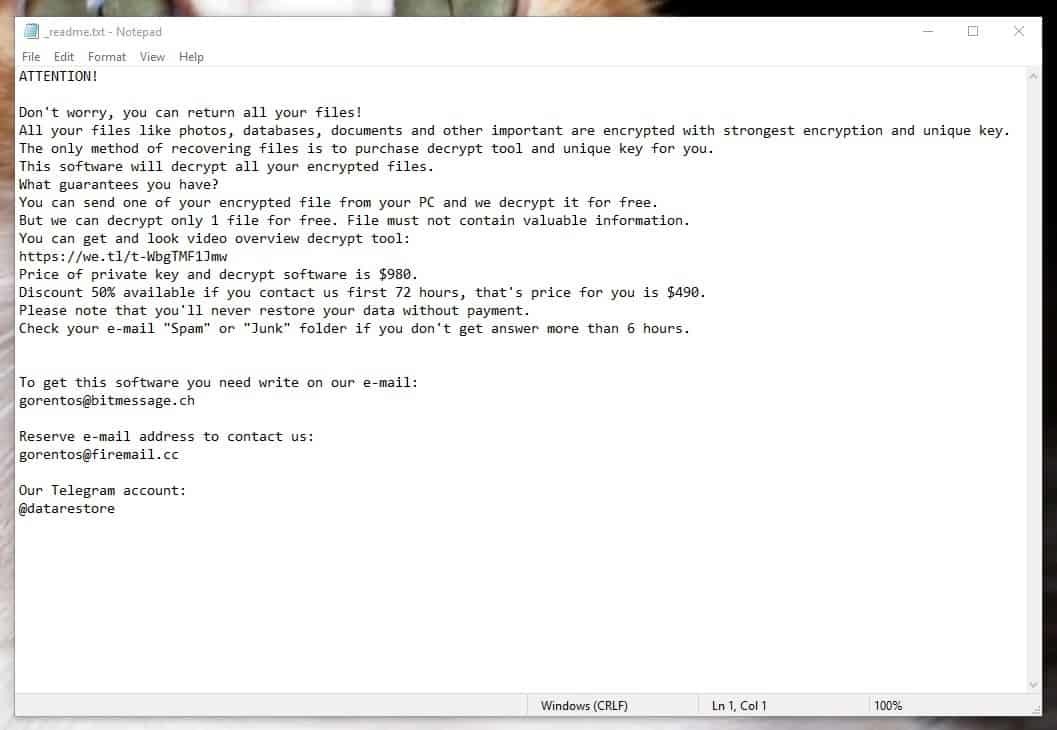
The web space can be very helpful but sometimes, it can also be something very dangerous if you’re not observant and careful enough. Having said that, probably the most devastating of all the current system threats out there is the vicious Ransomware cryptovirus. The main thing that those virus programs are famous for is their ability to ask ransom from the targeted users, hence the name Ransomware. The exact cryptovirus we will be focusing on in the next paragraphs is one which is notorious for sealing the targeted user’s data by utilizing an advanced data-encryption code and afterwards requesting a ransom payment in return for the decryption key that can decrypt the documents. The virus’ name is Nelasod and most likely a lot of you have come across this article simply because you’ve been searching for a method to cope with it. If you are indeed one of the numerous victims of this dangerous virus, bear in mind that the following lines include some very important information which might help you remove the harmful software and avoid the ransom payment.
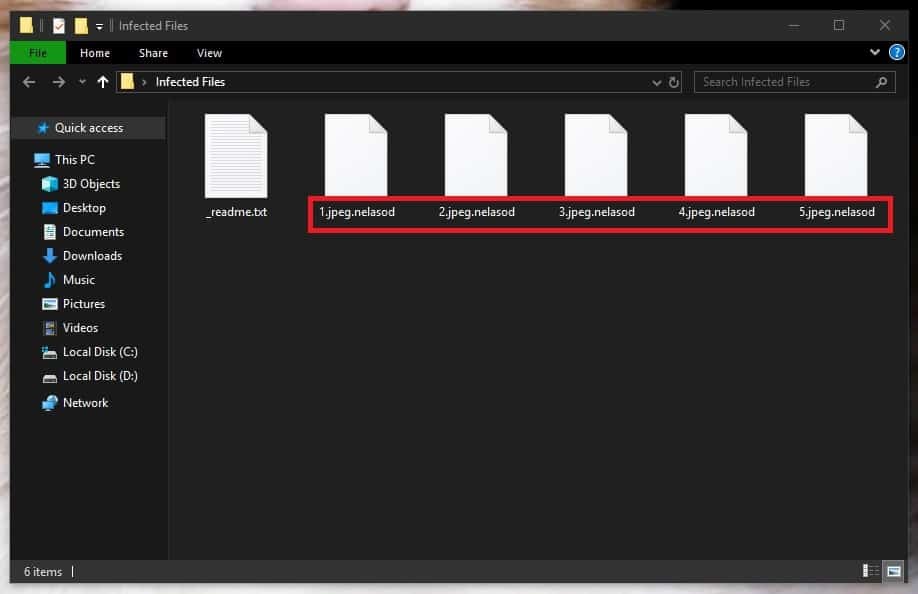
First of all, however, take into account that in the event you have a Ransomware named Nelasod, Format or Access on your computer, then you definitely are not dealing with a regular type of malware. The kind of malware is programmed to lock up your personal files. At the same time, no actual damage is caused to any element of your system. In reality, the encryption procedure isn’t hazardous on its own – its primary use is to keep digital data safe from unauthorized access with the help of encryption and a special decryption key. Yet, malware like Nelasod utilizes that against the users. The reason why this is so important is that, since no real harm is done to the computer, noticing the virus invasion can become incredibly difficult. Perhaps that’s the primary reason why this category of malware normally doesn’t get spotted by the vast majority of anti-malware applications – it doesn’t trigger any reaction from the protection software because no actual damage is caused by it. Another reason for the malware to remain hidden is the fact that the potential symptoms caused by the infection are usually pretty much undetectable.
Should you pay the ransom to get your encrypted with .nelasod files?
Assuming that your machine has been invaded by Nelasod, you might be thinking about completing the requested ransom payment as a means to get your files back. In reality, however, there is no method that can ensure the successful restoration of your encrypted files. Agreeing to carry out the ransom payment certainly ensures that you would lose a certain amount of money, though. That’s why, before you decide to give your money to the hackers behind Nelasod, it is a good idea to explore the alternatives that don’t involve ransom payment. For instance, you may want to give a try to some file-recovery methods, which may eventually save some of your encrypted data, or you may want to remove Nelasod and use your own file backups to get things back. In any case, remember the fact that there have been cases of victims of Ransomware that have paid enormous amounts of ransom for decryption key from the hackers and haven’t been given anything in return. Therefore, do not pay anything right away and seek some legitimate alternatives which can save you money and nerves.
SUMMARY:
Nelasod Ransomware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply