Crypto Death
Crypto Death is a message in one of the announcement channels about ransomware spreading around Discord via DMs. The Crypto Death scam’s creators would use different tricks to panic the receivers of the Crypto Death Ransomware message into believing their device has been compromised by a malware and to spread the scam to anyone they can.
Crypto Death Message Scam
Everyone has heard about the notorious Trojan Horse viruses, but not everybody has ever met one. However, once you get one in your computer, the close encounter is not an enjoyable one. One of the most recent Trojans that has been reported to us is the insidious Crypto Death. If you have discovered that this specific piece of malware has invaded your computer, it is in your hands to ensure that the infection is removed in a timely manner, so as to avoid any further harm that it may cause. Besides, we have prepared a very comprehensive removal manual for that purpose. You can discover it just below this article, but we suggest that you first read through the following information before scrolling down to the guidelines so that you have a clearer idea of what you are up against.
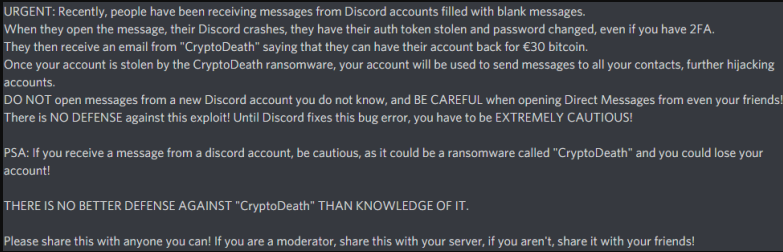
The Crypto Death Chain Letter
One of the most commonly used ways to spread malware via Crypto Death Chain Letter is when a message is sent to the user from a discord account, claiming that the user must be cautious – this is referred as a Crypto Death Chain Letter virus message. Crypto Death Chain Letter try to trick users taht they need to spread the message to all their contacts.
The Trojans are responsible for the overwhelming 70% of all malware infections that happen online, and there are a number of reasons for that. These threats are incredibly stealthy, and can remain undetected for days, weeks, ore even months on the victim’s computer without showing visible symptoms. Another thing about this specific category of malware is that its representatives can be used for a whole list of different criminal activities, making them a versatile instrument for various kinds if cyber crimes. Now, as far as Crypto Death is concerned, this Trojan-based infection can be very unpredictable since its creators can program it to perform different criminal activities in each separate case.
Now, you may wonder precisely what this virus does once your computer gets infected. An infection like Crypto Death can be used to provide remote access to your computer, or transmit any information stored there to the hackers’ servers. This means that all of your most sensitive, and valuable data can get exposed, and be used against you by people with malicious intentions. The malware can secretly collect personal details, and financial information, such as numbers of credit cards, passwords for your online accounts, etc., and place it right into the hands of the cyber criminals who control it. Afterwards, the crooks can hijack your social media accounts, drain your online bank accounts, blackmail you, and many more. Furthermore, they may secretly insert other infection such as Ransomware, or different viruses inside the system, and damage it in such a way that it cannot be repaired.
With all this in mind, it is more than clear that you should take immediate actions, and remove Crypto Death from your computer quickly and reliably. The removal guide below can surely help you with this uneasy task, but we do recommend that you run a full system scan with a trusted security software tool for optimal results.
Needless to say, due to the usual lack of any obvious symptoms, detecting this Trojan can be extremely difficult. That’s why, if you have never dealt with a representative of this malware category before, we highly recommend that you stick to the instructions from the manual guide below, and/or use the recommended advanced malware-removal tool that has been linked on this page.
SUMMARY:
| Name | Crypto Death |
| Type | Trojan |
| Detection Tool |
Remove Crypto Death Discord Ransomware Scam
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment