Cuba Ransomware
Cuba Ransomware is a file-encrypting version of a ransomware infection that can attack computers without showing visible symptoms. The ultimate goal of Cuba Ransomware is to render a list of user files inaccessible so that it can ask the owners for ransom.
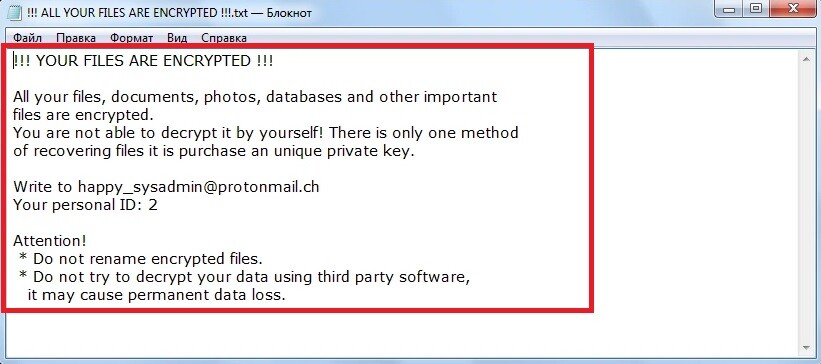
The Cuba Ransomware Ransom Note
Basically, the way this infection operates revolves around a classic blackmail scheme where the files of the victims are held hostage in exchange for some money. Typically, Cuba Ransomware targets commonly used files that are considered of great value such as documents, databases, archives, images, videos, etc. so that once they become encrypted with its secret algorithm, the victims won’t be able to access them with any software unless they apply a special decryption key. This decryption key is precisely what the hackers behind the ransomware virus ask a ransom for and they promise to send it only to those users who agree to fulfill all their demands.
However, it is still questionable whether they will actually send you a key once you have paid them. It would certainly not be unexpected for the hackers to disappear with the money without providing you with a key. After all, the moment they get what they want, they would be least bothered to deal with you and your encrypted files. Moreover, even if they send you something in exchange for your money, there is no guarantee that this will be precisely the key that will successfully decrypt your files.
In this line of thinking, trying to resolve the ransomware problem by means of alternative actions is a much better idea. In fact, it is essential to remove Cuba Ransomware from your computer if you want to be able to use it and potentially recover some of your files on it. Otherwise, if the file-encrypting virus is present in the system, it will continue to encrypt any new file that you create or manage to restore. That’s why, at the end of this article, we have published a detailed removal guide to help you locate and eliminate the ransomware in a quick and effective manner. We have also included as section with free method for file recovery which you can try out.
The Cuba Ransomware virus
The Cuba Ransomware virus is a piece of malware of the ransomware type that can operate under the radar of most antivirus programs. The cryptography used by the Cuba Ransomware virus is not harmful and thus antivirus programs typically don’t do anything to disable it or notify you about the encryption process.
In addition, some more advanced versions of ransomware can even disable your antivirus program to ensure it won’t interfere with their file encrypting process. This, along with the complexity of the encryption code, has greatly helped make ransomware the most dangerous type of malware. That’s why the best way to stay protected is to rely on prevention particularly by keeping away from possible transmitters of such infections and sketchy web content such as spam messages, fake online advertisements or cracked software installers. What is even more important, though, is to create backups of your data on a remote disk or cloud server so that you never have to experience data loss or restricted access.
The Cuba Ransomware file extension
The Cuba Ransomware file extension is an odd suffix that ensures the encrypted files cannot be recognized by any software. The Cuba Ransomware file extension replaces the original file extension and is attached at the end of each encrypted file name.
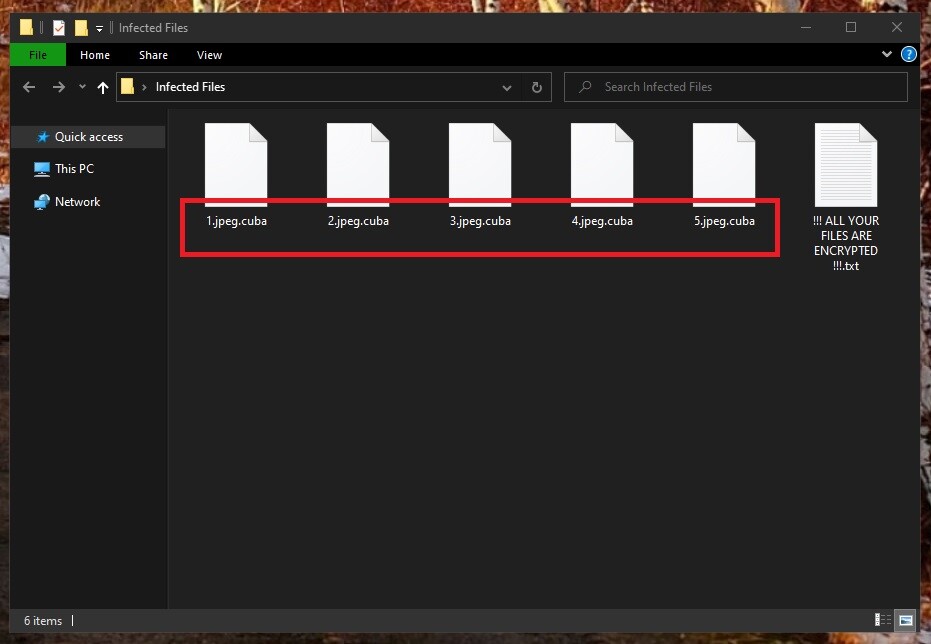
The Cuba Ransomware encrypted files
SUMMARY:
| Name | Cuba Ransomware |
| Type | Ransomware |
| Detection Tool |
Remove Cuba Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment