The CVE-2021-36934 vulnerability
A recently discovered security flaw in the current beta version of the upcoming Windows 11 could allow threat actors to infiltrate the system and gain the highest privileges level, which, in turn, can enable them to do anything they want on the attacked computer.

The flaw affects the Security Account Manager (SAM), which is the Windows database that stores account information such as usernames and account passwords for the computer.
The newly-discovered vulnerability
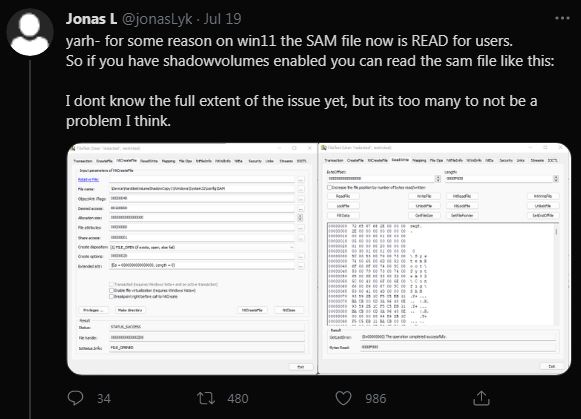
The flaw (tracked as CVE-2021-36934) was first discovered by a researcher who goes by the name of Jonas Lyk. He posted on his Twitter account that he has noticed a bug in the coding of the beta version of Windows 11. According to his post, the contents of the Security Account Manager (SAM) database could be read by accounts with low-level (user) privileges.
If a regular user account can have access to the contents of the SAM database, this means that a hacker doesn’t initially need Admin privileges on the Windows computer that they attack in order to eventually gain control of the entire system. Instead, they could exploit this newly-found bug and thus gain access to system settings that should otherwise only be accessible to Admin-level users. Of course, the hacker would still need to gain remote access to the victim’s computer, but it’s significantly easier to do this with low-level privileges.
How the bug can be used
Gaining access to the information stored in the SAM database could allow attackers who only have user-level privileges to learn the passwords of Admin accounts and access said accounts. From there on, there’s no limit to what the hacker could do, given enough time. This vulnerability could also enable threat actors to extract sensitive data that’s cryptographically protected. In other words, noting on the computer would be safe if an attacker manages to successfully exploit this security flaw. It would even be possible for the hackers to create entirely new accounts with elevated privileges on the computer, while at the same time restricting the privileges of any other accounts.
The flaw is also present in Windows 10
As it turns out, this Windows 11 flaw isn’t a regression from Windows 10 (as was initially believed) but rather a vulnerability that has been present in Windows systems for quite some time. Apparently, all Windows 10 versions from the last two and a half years also have this bug in their code.
Further research revealed that the flaw gets manifested when the Volume Shadow Copy Service is active. This is a Windows feature that makes it possible for the system or other programs in it to take disk snapshots without the file system getting locked.
One important thign to note is that the bug, as of the moment of writing this, has not yet been patched out so there’s currently no fixing patch for it that you can install to secure your system.
Thus far, there hasn’t been any information about the bug getting exploited in the wild, though, according to Microsoft, the likelihood of this happening has increased after the vulnerability was publicly announced.
Microsoft is currently investigating the problem and is working towards fixing it.

Leave a Comment