Cybercriminals stole data from LG and Xerox in a ransomware attack
Back in June, the hacker group known as Maze launched a successful ransomware attack against LG and Xerox with the goal to blackmail the firms for a payment. In the time between then and now, the firms were given time to decide on whether to comply with the hacker’s demands or to face the supposed consequences of having their stolen data uploaded and made public on Maze’s leak portal/website. Today seems to have been the final day from the deadline and since neither firm has given in to the hackers’ demands, their data has been uploaded to the leak site of the Maze gang.

The Maze Ransomware attack
When the Maze gang attacks with its eponymous Ransomware, the infection goes through several stages. First, the virus steals any sensitive data it can find on the victim’s servers, and then it encrypts the files that are present there. The victims are told to pay a ransom to receive the matching decryption key for the locked data. However, oftentimes, especially in the case of big companies like Xerox and LG, the victims would have extensive backups of their data and would have no problem recovering the files. This is why, if the ransom payment is refused, the hackers from the Maze gang threaten to make the stolen data public by uploading it to their leak website, which is what seems to have happened in the current case.
One interesting thing to note, however, is that the people from the Maze gang themselves have made a statement that they had decided to skip the data-encryption stage when attacking LG because so that LG’s clients wouldn’t get affected by the attack. On the other hand, there’s currently no information about whether any data on the servers of the Xerox company got encrypted or if their data only got stolen by the Maze ransomware.
Aftermath
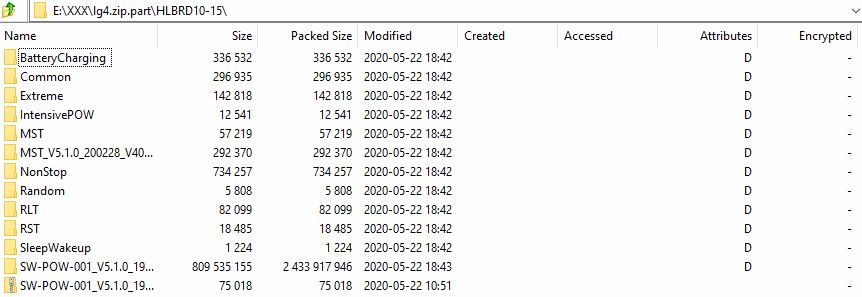
Currently, anyone can visit the leak site of the Maze gang and have a look at the leaked data (which is something we do not endorse). The result from the data leak for LG is that around 50GB of firmware source code (closed) related to different LG products (laptops, smartphones, tablets, etc.) has been uploaded to the leak website of the hackers behind the Maze Ransomware. LG has made a generic statement during June about the attack on their network by the Maze Ransomware in which the company says they will look into the attack and contact the respective authorities if necessary. So far, after the stolen data was made public, there has been no official statement from the company.
For Xerox, the “kidnapped” data seems to contain information about Xerox employees and customer operations. So far, no customer-specific information has been found inside the data leaks. Xerox is yet to make any sort of an official statement and there is very little additional information about the attack on their servers.

What made the attack possible?
According to Troy Mursch, the co-founder of the security-research company known as Bad Packets, both of the companies attacked by the Maze Ransomware in June had unpatched Citrix ADC servers during the time of the attack. The specific weakness used to infiltrate the servers is known as CVE-2019-19781, which is a vulnerability that the Maze gang seems to oftentimes exploit.
An interesting piece of information is that the research firm known as Shadow Intelligence reports that, at the time of the data leak, another cyber criminal was selling access details for the research and development center of LG America. The “offer” was put on a hacking forum and the price for the access details was between 10,000 and 13,000 US dollars.

Leave a Comment