*Dapo is a variant of Stop/DJVU. Source of claim SH can remove it.
Dapo
Dapo is identified by security specialists as what is known as a ransomware cryptovirus. This means that Dapo has the ability to encrypt files on its victims’ computers.
In essence, this boils down to the fact that after Dapo has invaded your machine, it will scan it for specific file types (usually the most commonly used ones such as documents, pictures, audios and videos, etc.). After this it compiles a list of these files, which it then proceeds to create encrypted copies of, one by one. Simultaneously, the originals of the files are deleted. And upon the completion of this rather tedious process, the victim user is left with a whole bunch of files that cannot be opened or accessed in any way.
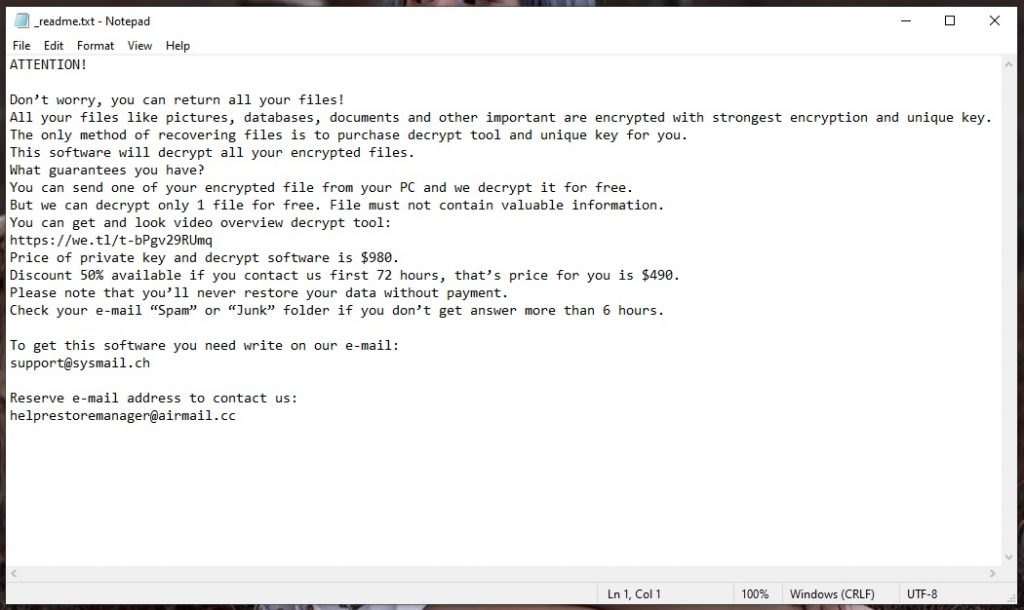
In addition, to make sure that the victims are aware of what has transpired, the ransomware will typically leave a ransom note someplace where it will for sure be seen, like on the computer desktop. Furthermore, it will contain an ultimatum that states you are required to pay a certain amount of money, otherwise you will never regain access to your files. Hence, the hackers behind Dapo, Qapo, Erop want you to pay ransom for your files, which is where this malware category get its name from.
However, don’t be too quick to fall for these threats. There are other alternatives available to you, and you don’t necessary have to spend obscene amounts of money on a decryption code that may not even work. Below we have put together a detailed removal guide with the help of which you will be able to remove Dapo, which is a vital step that you should take regardless of what you choose to do regarding the ransom payment. And in the second part of the guide you will see our suggestions concerning the recovery of your files.
The Dapo virus
The Dapo virus is particularly dangerous because of the complex encryption algorithm it uses. There is little that can guarantee that the effects of the Dapo virus will be reversed and you will be able to use your files again.

In addition, this very same encryption is what ensures that ransomware doesn’t trigger most antivirus programs out there. And since these types of viruses are particularly stealthy, meaning they do not have any noticeable symptoms, this makes them practically invincible once they’ve made their way into your system.
Therefore, one surefire way to disarm a virus like Dapo is by preventively backing up your most valuable data and storing it on a cloud service, or better yet, on a separate hard drive. And of course, practicing basic safety measures when browsing the web is essential to preventing ransomware attacks. This implies staying away from sketchy web locations, avoiding spam like the plague and sticking to trusted web sources and content.
The .Dapo file extension
You may have noticed that all the encrypted files share an identical suffix – this is the .Dapo file extension. The .Dapo files extension basically ensures that no software will be able to recognize the file format of the encoded data.
SUMMARY:
| Name | Dapo |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Dapo is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Dapo Ransomware

Bookmarking this page is a good idea as a start because if you want to complete the guide, you may need to restart your system several times during the instructions below.
Dapo is a ransomware that may secretly add one or more malicious components inside the system, most of which may come in the form of rogue applications that look indistinguishable from a regular app. The challenge here is to find those rogue applications and uninstall them from the computer.
For that, click on the Start menu button and type Programs and Features in the search bar.
Next, select the result and carefully scroll the list of installed applications in a search for a potentially rogue program that could be linked to the ransomware.
Apps that have been installed right before Dapo appeared on your system are most likely to be linked to the threat, so check them out online and if you find that they are sketchy, highlight them with the cursor and click on the Uninstall button at the top.
Follow all the steps from the uninstallation wizard and pay special attention to any checkmarks related to components of that program that have been installed along with it.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Dapo is a variant of Stop/DJVU. Source of claim SH can remove it.
Aside from installing rogue apps, a ransomware like Dapo may start various malicious processes in the system without the victim’s knowledge. That’s why the next thing that you need to do if you want to remove Dapo is to search for these processes and stop them.
You can do that by navigating to the Processes tab in the Windows Task Manager. To open the Task Manager, press CTRL + SHIFT + ESC together and then click on the Processes Tab.
Explore the list of running processes and try to find anything that may be operated by the ransomware. Processes with odd names and high CPU and Memory usage should best be researched online and then checked with a reliable anti-malware scanner.

To check a given process that you find suspicious, right-click on it and select Open File Location.
You can use the free virus scanner below to check all files in that location for malware:

If danger is found in them, quickly end the related process (right-click>>>End Process) and delete the dangerous files and their folders.

In case you aren’t sure that you have stopped all ransomware-related processes, and you think that there might be something else that is running in the background of the system without your knowledge, it is best to reboot the computer in Safe Mode during the next steps. (check the link with instructions on how to reboot in Safe Mode).
Next, after the computer reboots, use the Windows and R key combination to open a Run box on the screen.
In that Run box copy the following line and click on the OK button:
notepad %windir%/system32/Drivers/etc/hosts
A Notepad file named Hosts will open.
Scroll the text in the file and search for Localhost.
If you see nothing suspicious in there, then you don’t need to worry.
If the ransomware has made changes in that file, however, you will see a number of questionable IP addresses there, in which case we advise you to drop us a comment with a copy of those IPs, so we can check them and advise you on what to do next.

Next, you need to open System Configuration by typing msconfig in the windows search bar and pressing the Enter keyboard key:

In Startup search for items that have been added recently or look suspicious and cannot be related to any of the programs that are usually starting when your computer boots.
If a given item grabs your attention, Uncheck its checkmark to disable it.
- Please keep in mind that the ransomware may camouflage its items by using fake Manufacturer and process name, so be careful and research online every suspicious process in the list.

*Dapo is a variant of Stop/DJVU. Source of claim SH can remove it.
Aside from adding components in your Startup Items list, Dapo may alter the Registry without your knowledge by adding malicious files to several directories.
To check the Registry for changes, type Regedit in the windows search field and press Enter.
Next, open a Find window by pressing CTRL and F together.
Write the name of the ransomware inside the Find box and click on the Find Next button to perform a search. Delete any results that are found with that name.
Caution! You can damage your system if you delete entries not related to the ransomware. To avoid that risk, please use the professional removal program recommended on this page to clean your computer from malicious files.
Next, go to the Windows Search Field and type each of the following:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Open the results and check for any suspicious folders and files that have been added recently.
When you reach to Temp, delete everything stored in there.

How to Decrypt Dapo files
After you remove Dapo, you may be eager to recover some of the files that have been encrypted. For that, we recommend you to check our comprehensive guide with file decryption steps that can be found here.
If you run into any trouble, please don’t hesitate to leave us a comment, and we will do our best to help you out.

Leave a Comment