The DarkRadiation ransomware
Malware researchers are warning web users over a new strain of ransomware called “DarkRadiation”. As per the available information, the new threat implements its code in Bash and targets Linux and Docker cloud containers.
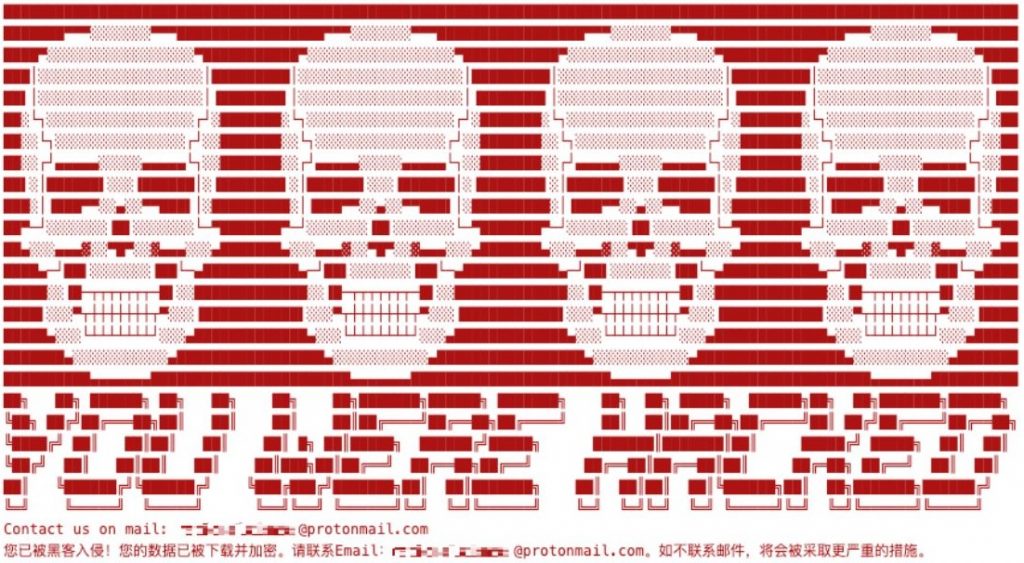
Researchers from Trend Micro released a study last week which claimed that the ransomware was built in Bash scripting and targeted Red Hat/CentOS and Debian Linux systems. The DarkRadiation malware encrypts different folders in various system directories using OpenSSL’s AES algorithm and CBC mode. In addition, it utilizes Telegram’s API to inform the threat actor(s) of the infection’s status. Presently, there is no information on the ransomware’s methods of distribution. Fortunately, there is no proof of the ransomware being used in real-world attacks as of the time of this writing.
The discovery of the threat follows an analysis of a set of hacking tools, that were first noticed on 28th of May. DarkRadiation ransomware is notable for its heavy use of Bash scripts to extract the actual malware and apply encryption, and for the use of Telegram API to interact with C2 servers through hardcoded API keys. The infection process passes through several stages before the malware completes its final agenda.
It is speculated that the ransomware is still under development, and it utilizes obfuscation techniques to jumble the Bash script by utilizing an open-source program named “node-bash-obfuscate. A distinctive feature of DarkRadiation ransomware is that the encrypted files infected with the ransomware receive a radioactive symbol ‘.☢’ as an additional file extension.
As soon as it compromised the system, the ransomware checks if it is run as the root user and has elevated permissions, after which it installs Wget, cURL, and OpenSSL libraries while also making snapshots of all users who are currently logged into the compromized system. These results are then sent to an attacker-controlled server through the Telegram API.
In the last stage of the infection, before proceeding to the actual encryption process, the ransomware fetches a list of all of the system’s available users, overwrites their passwords with “megapassword,” and creates a new user account named “ferrum” with a “MegPw0rD3” password. Then, it deletes all the shell accounts.

Leave a Comment