*Source of claim SH can remove it.
Data Shield for Chrome
Data Shield for Chrome is a form of rogue browser plugin that security experts recognize as a browser hijacker. Browser hijackers like Data Shield for Chrome will typically shower your browser’s screen with pay-per-click ads and will try to monitor your web surfing behavior and their configurations with the most popular web surfing programs.
The browsing application will also start to operate unusually, causing unintended link changes to separate supported pages or filling in your search results with hard-to-remove advertisements, etc. The appearance of a range of banners, box notifications, pop-ups and several others types of on-screen promotional messages during your site surfing sessions are other very typical effects of a browser hacker attack.
The Data Shield for Chrome Virus
Typically, apps like the Data Shield for Chrome Virus and Main Captcha Top are able to attach to any web browsers without necessarily informing the users clearly about their intentions to make modifications to their key settings. However, the end consequence, after the Data Shield for Chrome Virus has made its “improvements”, is that at the beginning of their next surfing session users will be greeted by a new homepage address or a completely different search engine.
You would need to go straight to the source of the browsing disturbance if you want to uninstall all these irritating new improvements to your browsing app and remove all the nagging commercials without leaving them a chance to come back again. For that, we have created a special removal guide for Data Shield for Chrome to support you during the removal process, since it isn’t always a simple job to get rid of a browser hijacker.
This type of software may sometimes contribute to some system vulnerability problems, as well as user exposure to different online security hazards, including the notorious ransomware and Trojan threats.
While not treated as computer viruses or malware, most browser hijackers appear to be viewed as potentially unwanted programs (PUPs). And that is for a number of reasons, but first and foremost, such apps may compromise the safety of your computer by rerouting you to random and sketchy web locations. A piece of software such as Data Shield for Chrome, may inadvertently expose you to ambiguous sites and pages that can serve as hub for viruses.
Keeping away from any of the Data Shield for Chrome virus advertising materials is a good idea if you want to avoid a close encounter with harmful malware such as Trojans, ransomware, rootkits and other online hazards. That is why having the Data Shield for Chrome virus removed isn’t only about restoring your browser’s settings and surfing the web without nagging ads.
Another explanation why you may want Data Shield for Chrome uninstalled is that the ad-generating processes will consume a huge amount of resources. After all, it requires tremendous RAM and Processor power to display hundreds of advertisements and auto-redirects in your browser. This, in turn, may render the machine latent and unresponsive over time.
In addition, browser hijackers such as Data Shield for Chrome also gather browsing data from compromised machines as part of their background activities. And although these types of data-collection activities are popular and are basically performed by all websites nowadays, in the case of browser hijackers and related applications, this is not clearly mentioned clearly and the users usually do not realize that their browsing activities are being tracked down and processed.
SUMMARY:
| Name | Data Shield for Chrome |
| Type | Browser Hijacker |
| Detection Tool |
*Source of claim SH can remove it.
Remove Data Shield for Chrome Virus
To try and remove Data Shield for Chrome quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Data Shield for Chrome extension (as well as any other unfamiliar ones).
- Remove Data Shield for Chrome by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Data Shield for Chrome and any other suspicious items.
If this does not work as described please follow our more detailed Data Shield for Chrome removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

*Source of claim SH can remove it.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Data Shield for Chrome from Internet Explorer:
Remove Data Shield for Chrome from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
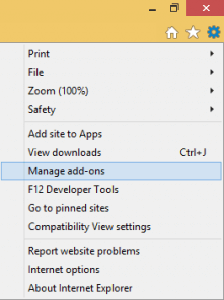
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
 Remove Data Shield for Chrome from Firefox:
Remove Data Shield for Chrome from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

 Remove Data Shield for Chrome from Chrome:
Remove Data Shield for Chrome from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
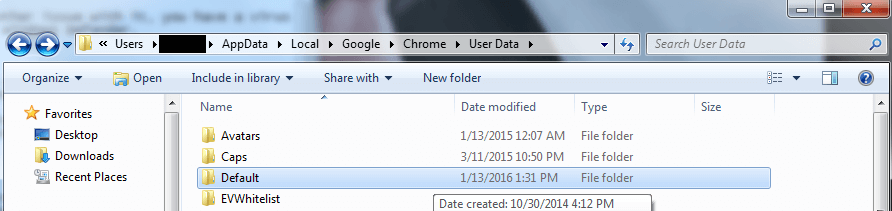
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment