Decacopy
To successfully deal with a Trojan Horse attack such as Decacopy on your computer, you will need to find and delete all data related to the malware program, kill all of its processes, and remove all of its registry keys. This, however, can be quite a challenging task, especially if you are faced with a newly released Trojan virus like Decacopy.
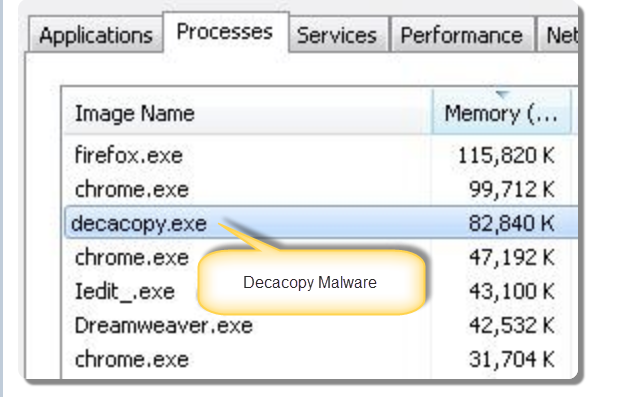
Decacopy is a process running on your system that consumes CPU resources and memory, and appeared to be a malicious file and attack your PC.
However, if you are here because you suspect you may have already landed this particular Trojan, its good that you’ve found this article. Through the help of the instructions below, you should be able to manually locate the malware-related data, and remove it. Also, the advanced removal tool suggested on this page is also an effective solution to the Decacopy-related problem that you have. Usually, the best you could do now is combine both removal solutions, as this will give you the highest chance of eliminating the virus.
The Decacopy Virus
When the malware is a new one, like the Decacopy Virus even if you have an antivirus in place, the security program may still fail to pick up the infection. You see, most antivirus programs rely on their database to detect threats, but if the malware is new, it won’t be present in the antivirus’ database, and detecting the infection may not always take place.
Modern high-tier antivirus suits have tools that allow them to spot new and unknown infections based on the malware’s behavior. However, there’s no guarantee that this will work in all cases, especially when talking about a highly stealthy Trojan such as Decacopy.
Decacopy Clipboard Manager
Decacopy Clipboard Manager is unique with regard to the way it is used. While most other commonly encountered forms of malware have certain specific uses, and you won’t see much deviation from those uses between the malware’s individual representatives, with the Trojan Horse threats. The use of the infection is oftentimes situational, and can change from one instance to the other.
Deca copy Lite Clipboard Manager
Deca copy Lite Clipboard Manager can acquire important and valuable data from the computer of their victims, take control of the targeted computer, and use it in some way for the benefit of the hacker. A big portion of the Trojan Horse representatives are capable of creating and exploiting weaknesses in the systems they infect, and silently sneak in additional malware. Ransomware, for instance, is a form of malware that oftentimes needs the help of a Trojan to infiltrate the systems of its victims.
We can go on and on about the many different ways in which a virus like Decacopy can be utilized, but currently it is more important that you learn how you can save your system, and remove the infection that’s currently in it. That is why we will now leave you with our guide, which you are advised to complete so as to liberate your computer.
SUMMARY:
| Name | Decacopy |
| Type | Trojan |
| Detection Tool |
Remove Decacopy Virus
Here is quick method that may help you remove Decacopy Virus from your computer that you may want to try before getting into the detailed steps that our team has described in the manual removal guide below.
- Start by pressing the Start menu button of your Windows and navigating to the Control Panel.
- From there, go to Programs and Features>>>Uninstall a Program.
- You will see a list of all the programs that have been installed on your computer.
- From that list, carefully search for Decacopy, as well as other unfamiliar apps that you can’t remember installing or ones that look questionable.
- Uninstall Decacopy and the unfamiliar apps from your system.
If these quick instructions have not resolved your problem and Decacopy is still present on your computer, then follow the step-by-step manual instructions in the removal guide below:
![]()
There are steps in this manual removal guide that will require you to exit this page and restart your operating system. Therefore, we recommend Bookmarking it, so you can refer back to the guide and continue with the removal process.
Before proceeding to the next steps, Reboot your computer in Safe Mode (click on the active link for instructions on that).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
The first thing that you need to do if you have been infected with the Decacopy Virus on your computer is to go to the Processes Tab and detect which proceccess are related to it and are dangerous.
The quickest way to do that is to press CTRL + SHIFT + ESC key combination, go through the Processes Tab’s list and try to figure out which of the processes that are shown could be related to the danger.

If you detect such processes, right-click on them and then choose the Open File Location option from the menu. After that, scan the files found in these locations with the recommended free online scanner that you can find on this page.

When you reach the folder with infected files and open it, end the processes that are related to these files and delete the entire folders.
Note: No scanner is perfect, thus, there might be files that have not been flagged as part of the infection. If you have a strong reason to believe that specific files and processes are infected but they haven’t been detected by the scanner, don’t leave them on the computer but carefully check them and delete them.
![]()
The thrid important step related to the removal process of Decacopy is to enter the Control Panel.
To do that, hold the Start Key and R key together. A Run box will open where you have to type appwiz.cpl and click OK.

Once you enter the Control Panel, your job is to carefully check for questionable entires and Uninstall them.
In case that a pop-up window like the one shown below appears on your screen, make sure you select “No”.

![]()
The fourth step requires you to tinker with some very important system files and registry entries, thus, you have to be very careful and strictly follow the described instructions in order to prevent an involuntary system corruption or potential file damage.
One quick way to avoid the deletion of important OS-related files, is to use a professional malware removal tool.
If you decide to go for the manual method, then go to the search filed of your Windows, type the msconfig command and hit the Enter button.
A System Configuration window will pop-up as shown on the image below:

Go to the Startup tab and remove the checkmark of entries that look suspicious or have and “Unknown” Manufacturer.
Important! In case you have a suspicion that a more serious threat (such as a ransomware or some other malware) has compromised your computer, do the following:
Hold the Start button of the keyboard and the R button simultaniously. A Run window will show up on your screen. In the text field, copy the following command:
notepad %windir%/system32/Drivers/etc/hosts
Then press the Enter key to run the command.
This will open a file on your screen that can help you figure out if you have been compromized by hackers.
In case that this is your situation, you will detect a lot of strange IP addressses connected to your computer.
The image below explains you what to look for:

In case that in your file you detect some suspicious IPs below the “Localhost” section, please contact us by leaving a comment at the end of this article.
![]()
The final step of the Decacopy Virus removal requires you to deal with specific entries loated in the Registry Editor and remove them.
To do that, go to the windows search filed, type Regedit and hit the Enter button.
Once you enter the Registry Editor, press the CTRL and F keyboard keys together and type the Name of the virus that you are searching for.
Next, right click on any entries that have the same or a similar name and delete them.
If no virus-related entries are detected in this way, you will have to manually go to the directories shown below and delete their content.
Here are the directories:
- HKEY_CURRENT_USER/Software/*Malicious Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/*Malicious Directory
HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/ Malicious Directory
If none of the steps in this guide can help you to remove Decacopy, then download the recomended malware removal tool from this page. Also, if you have any questions or concerns, don’t hesitate to leave us a comment below.

Hey, i have some “x client host” in hosts, i am sure this is some virus client ip, what now?
Hi Peter,
i would suggest you to remove that entry.
Hey when I try to delete the deacopy lite it just says would you like this publisher to make changes to your system what do I do?
Hi Adrian,
did you go through the whole guide? If the Pop up come back again click No.
Thanks by following step mentioned in your article my issue is resolved.