The Decocash Scam
In the digital age, scams have become as common as morning coffee. One such scam that has been making rounds recently is the Decocash scam. This scam cleverly disguises itself as a Coca Cola Customer Satisfaction Survey, promising rewards and cash prizes, only to leave victims with empty pockets and a sense of betrayal. The perpetrators behind the Decocash scam employ a strategic approach, leveraging the trusted reputation of Coca Cola to ensnare their targets. Through meticulously crafted emails, text messages, or social media posts, they entice recipients to participate in what appears to be a genuine survey, promising generous payments in return for their feedback. The allure of freebies, coupled with the recognition of a globally recognized brand like Coca Cola, creates an illusion of credibility that is difficult to resist.
Coca Cola Customer Satisfaction Survey
Customer satisfaction surveys, including the Coca Cola Customer Satisfaction Survey, are a legitimate and common practice among many businesses. These surveys are designed to gather feedback from customers about their experiences with the company’s products or services. However, scammers have found a way to exploit this practice for their gain, leading us to the Coca Cola Customer Satisfaction Survey scam. Unsuspecting individuals are targeted with false promises of rewards, leading them down a treacherous path of deceit and betrayal. This malicious scheme tarnishes the reputation of the genuine Coca Cola Survey and undermines the trust that customers place in legitimate feedback channels.
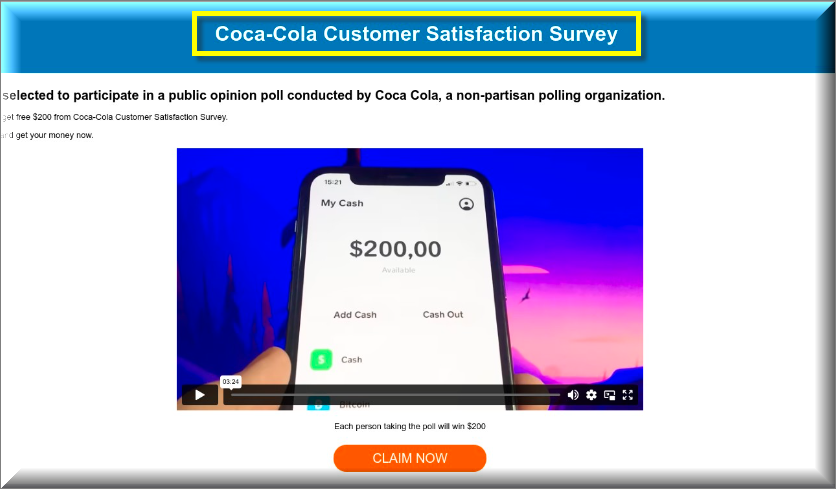
Coca-Cola Customer Satisfaction Survey Cash App
The scam operates by luring unsuspecting victims with the promise of cash rewards via Cash App, a popular money transfer service, in the guise of the Coca-Cola Customer Satisfaction Survey Cash App. The victims are led to believe that by participating in the survey and providing their Cash App details, they will receive a cash reward through the Coca-Cola Customer Satisfaction Survey Cash App. However, instead of receiving money, they end up losing it. This clever ploy preys on the trust individuals place in both the Cash App and the renowned Coca-Cola brand, exploiting their expectations for personal gain.
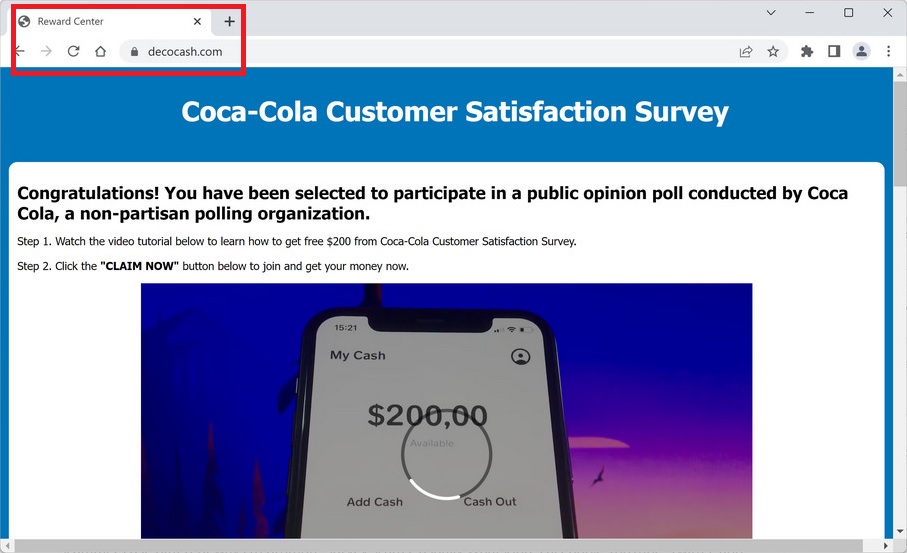
What is Decocash.com Coca Cola Survey?
The Decocash.com Coca Cola survey is a deceptive and manipulative scam intended to deceive individuals into sharing their personal information and financial details. Disguised as a legitimate Coca Cola customer satisfaction survey, this fraudulent scheme preys on the unsuspecting individuals, enticing them with the allure of cash rewards in exchange for their valuable time and feedback. The perpetrators behind the Decocash.com Coca Cola survey exploit the trust and recognition associated with the Coca Cola brand, cunningly leveraging its reputation to deceive people, promising them cash rewards for their time and feedback. This being said, it is important to remember that authentic customer surveys are typically conducted through official channels, such as the company’s website or authorized communication platforms.

The Decocash.com Cash App
The Decocash.com Cash App is the tool used by the scammers to carry out their fraudulent activities. Victims are asked to provide their Cash App details under the pretense of receiving their promised cash rewards. However, once the scammers gain access to this sensitive information through the Decocash.com Cash App, they exploit it to maliciously drain the victims’ accounts, leaving them devastated and financially harmed. It is crucial for individuals to remain cautious and vigilant when it comes to sharing their personal financial details, particularly in connection with suspicious platforms. Being mindful and verifying the authenticity of survey invitations can help safeguard against falling victim to survey scams and other fraudulent activities.
Is Decocash.com Legit?
The simple answer is no. Decocash.com is not a legitimate website. It is a front for a scam operation that preys on unsuspecting individuals. The promise of easy money through a simple survey is a classic bait-and-switch tactic used by scammers to lure their victims. That’s why, it’s crucial to stay vigilant and be skeptical of any offer like Decocash.com that seems too good to be true. Always verify the legitimacy of a survey before providing any personal or financial information. And remember, if it sounds too good to be true, it probably is. Stay safe out there!
SUMMARY:
| Name | Decocash |
| Type | Browser Hijacker |
| Detection Tool |
How to remove Decocash.com Scam
To try and remove Decocash quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Decocash extension (as well as any other unfamiliar ones).
- Remove Decocash by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Decocash and any other suspicious items.
If this does not work as described please follow our more detailed Decocash removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Decocash app and kill its processes
Uninstall the Decocash app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Decocash. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Decocash, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Decocash.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Decocash changes made to different system settings
Undo Decocash changes made to different system settings
It’s possible that Decocash has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Decocash from your browsers
Remove Decocash from your browsers
- Delete Decocash from Chrome
- Delete Decocash from Firefox
- Delete Decocash from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- irefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

I Apologize for the inconvenience…I hope to get 200$ yesterday for the time it took me to do all your company ask from myself… Just wondering when do I get my money? 4 hours was what I should be expecting not 24 hours…
I want to be part of your game
Hi Kennedy minadzi,
Decocash.com Coca Cola Customer Satisfaction Survey is a scam and we have no connections to this, i suggest you to check the guide and remove this scam. I strongly recommend you to not take part of this scam!
I need money to buy my sister something for her birthday
Hi Angelina Ramos,
Decocash.com Coca Cola Customer Satisfaction Survey is a Scam and you will not receive any money.
I am happy
Wow, I was completely unaware that Decocash.com was a scam and I’m so glad I stumbled upon your blog post. I took the Coca Cola survey last week and I’m relieved to know now that I didn’t compromise my personal info. Thank you for exposing this scam and keeping us informed, it’s much appreciated!