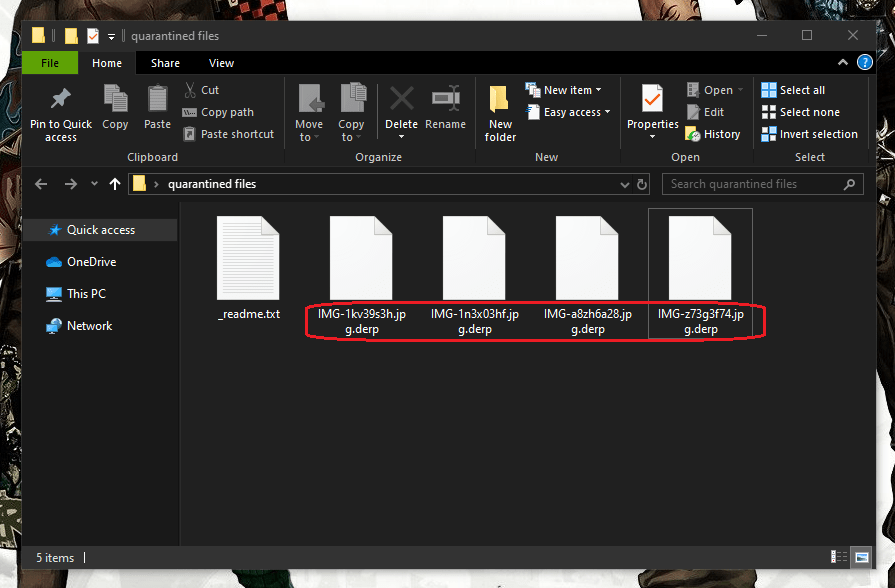
.Derp
.Derp is a very harmful Ransomware cryptovirus that prevents users from accessing their digital files. The .Derp infection demands a ransom in cryptocurrency in order to send the victims a decryption key for their data.
If a ransomware cryptovirus such as .Derp has compromised your system, we don’t have to tell you how terrifying an infection like this one can be.
Ransomware is becoming an ever-increasing problem, and if more and more users are armed with the correct knowledge of this type of malware, it will ultimately become powerless. For this reason, in order to gain a better understanding of what threats like .Derp, .Nols or .Leto are, we suggest reading through the following few paragraphs. Having said that, we should also note that the victims of this infection will find a helpful removal guide at the bottom of the article that will help to detect and remove the dreaded virus from their system. In addition, the guide also includes instructions that may potentially help recover all or at least some of the files that the cryptovirus has encrypted.
The .Derp virus
The .Derp virus is a ransom-demanding infection that uses encryption to block access to your data. The contamination with the .Derp virus can happen instantly without any visible symptoms.
The Ransomware viruses will typically scan your device for certain files, after which they will start creating encrypted copies of those files and deleting the originals. The encrypted copies are essentially unavailable to anyone without the application of a special key for decryption – the one that the hackers promise to send you after you pay them a ransom. The file-encryption process can go absolutely unnoticed in most situations, as most security software will not recognize it as a threat. After all, file encryption is a method of data protection, used in many public and private sectors where sensitive information should be secured from unauthorized access. In Ransomware, however, this method is used in a very sick and money-extorting scheme.
But what can you do to defend yourself? Unfortunately, everyone who has digital data may become a victim of Ransomware, so no one is fully protected from such attacks. As long as the victims keep paying the ransom, the hackers aren’t picky and target both individual web users, as well as small and big companies and institutions. They most commonly distribute the infection via mass spam email campaigns and hide the harmful code in different online places such as freeware and shareware sites, fake ads and pop-up messages, redirect links, files, and attachments shared through social media. This is useful knowledge because using only a little bit of common sense while browsing the web can help you prevent the vast majority of such infections and greatly decrease the risk of getting attacked.
The .Derp file decryption
The .Derp file decryption is a challenging task even for experienced security experts. Yet, recovery of the files locked by the .Derp file encryption may be possible in some cases.
As far as dealing with .Derp is concerned, we suggest that you head over to the removal guide below–it will help you remove the Ransomware from the system, which is actually very important if you want to be able to try some file-recovery methods. Remember that there are other solutions out there apart from the ransom payment, such as advanced decryptors, backups, and professional software, which may be worth the try. So, before giving your money to the hackers, we highly recommend exploring all other choices since there is absolutely no assurance that the crooks will really give you the key for your files.
SUMMARY:
.Derp Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply