.Devon
.Devon is a malicious software from the ransomware type that extorts money from web users through blackmail. Typically, .Devon encrypts important digital files on the computer and threatens the victims that they’ll never access those files again if they refuse to pay the ransom. During the time Devon is in the process of encrypting the files in your computer, it also generates a unique key that matches the encryption on your files. Supposedly, if you pay the ransom demanded by Devon, the criminals behind the virus will provide you with this key. However, whether or not that would truly happen is uncertain because you can’t trust the people responsible for the encryption of your files.
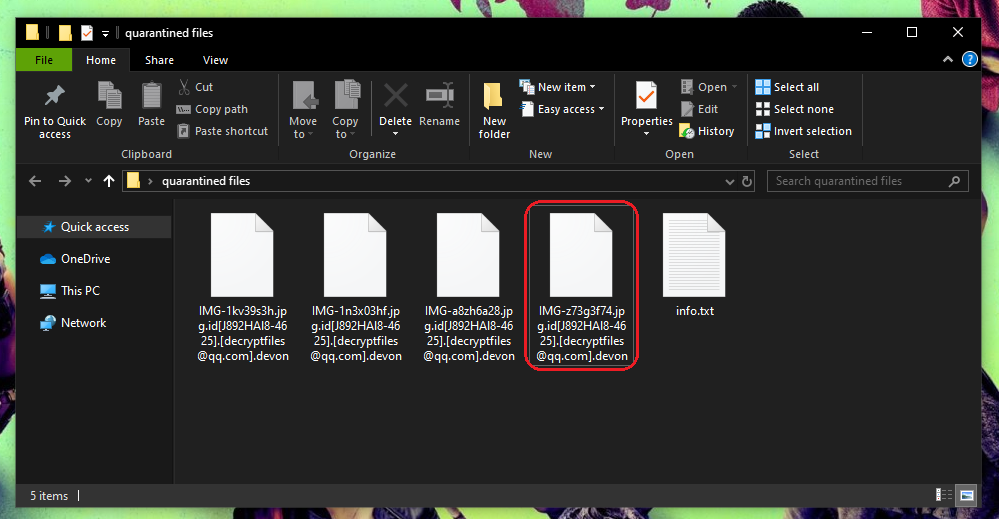
The .Devon Virus will encrypt your files.
If an unusual ransom message has appeared on the screen of your computer and along with that you have found out that you cannot open some of your most needed files, then this is a sign that you have been infected with .Devon ransomware. This particular infection is a new representative of the ransomware cryptovirus subcategory; and as such, it is aimed at blocking access to a variety of file types and asking a ransom payment so as to make them accessible again. .Devon uses cryptography to render a list of target files inaccessible and then generates a threatening message on the screen of the owners of the infected device. In that message, the crooks behind the ransomware demand payment of a fixed amount of money and promise that once they receive the payment they will send a special decryption key to recover the encrypted information.
On this page, however, we offer another course of action that does NOT involve paying ransom to some ruthless cyber crooks. We suggest you find out how to remove .Devon and recover your files from backups instead of transferring money to some online account. If you are interested to learn how stay on this page and check out the removal guide below.
The Devon virus
The .Devon virus is a ransom-demanding piece of malware that tricks web users into paying ransom for the liberation of their encrypted files. To extort money, the .Devon virus firstly encrypts files that are considered of great value for the victim and then places a threatening ransom-demanding message on their screen. The Devon Ransomware must be removed from your computer before you try to recover any of the locked files because there’s a chance that it will re-encrypt any of the data you may manage to bring back. The same applies to any new files you may download or create in your computer while the virus is still in it.
.Devon can typically infiltrate a computer with the help of a Trojan horse where the later serves as a backdoor for the ransomware to enter the system undetected. However, a cryptovirus like this one can be found also in spam emails and their attachments, in malvertisements, in misleading links and other sketchy web locations, cracked software installers and low-quality websites. One single click is all that it takes to get infected, and, sadly, there are hardly any visible symptoms that can give the malware away. In fact, since the file encryption is not a process that destroys anything in the system, most antivirus programs may fail to detect it and take action to stop it on time.
The Devon file decryption
The .Devon file decryption is one of the possible methods to regain access to the file that the .Devon ransom has encrypted. The specific thing about the .Devon file decryption is that it requires a decryption key, which is kept in secret by the hackers who control the infection. One very overlooked precaution measure extremely effective against Devon and other similar threats is the creation of backups. Having an external backup pretty much guarantees that you will always have safe copies of your files even if Devon or another Ransomware attacks your computer.
Thanks to its ability to skip the security software, the ransomware can complete its agenda undisturbed and surprise its victims with the scary ransom notification. What is particularly intimidating is that, in most such ransom notifications, the hackers don’t hesitate to use threats. They typically scare the users that if they don’t pay the demanded sum, the ransom will double, or the decryption key that can liberate the encrypted files will be destroyed forever, leaving the sealed data inaccessible for good. Unfortunately, most of these threats are genuine and the hackers stick to them. And even sending your money cannot guarantee that they will not do one of the above. If you take the initiative in your hands, however, and remove .Devon, you may be able to use personal backups or extract some files from your system for free, just as shown in the removal guide below.
SUMMARY:
Devon Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply